Use Abuse Of Personal Information Part Ii Robust Generation Of Fake
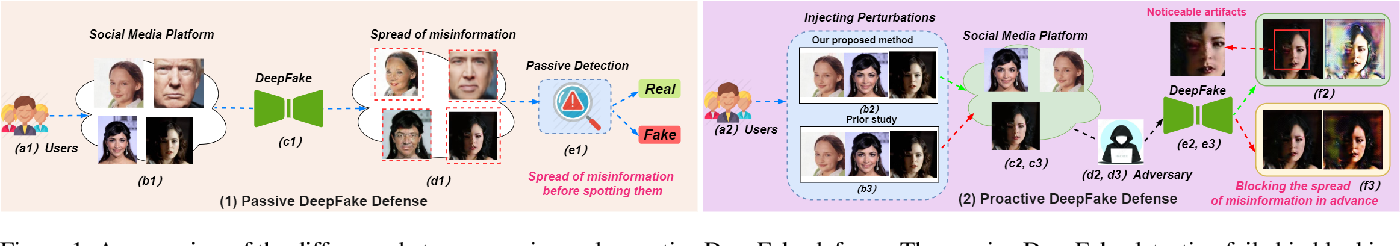
Figure 1 From Anti Forgery Towards A Stealthy And Robust Deepfake This paper formulates a model for realistic fake identities, constructs a robust fake identity generator, and outlines management methods targeted towards online transactions (email, phone, text) that pass both cursory machine and human examination for use in personal privacy experimentation. This paper formulates a model for realistic fake identities, constructs a robust fake identity generator, and outlines management methods targeted towards online transactions (email, phone,.
Cyberguard Fake Profile Detection Using Machine Learning Pdf This paper highlights the methodology used to create and validate a scalable fake id generator for these u&a experiments, which span a variety of topics from individual privacy to all kinds of quantitative social science questions. Search across a wide variety of disciplines and sources: articles, theses, books, abstracts and court opinions. Release of information to third parties if a website service releases or sells information to a third party of a user without explicit notification to the user, it undermines a consumer’s personal privacy. The cci project builds on two years of experimentation that demonstrated the ability to generate realistic fake identities, perform one time online interactions, and subsequently collect and analyze how that information is being both used and abused across email, sms text, and voicemail modalities.

Spammer Detection And Fake User Identification On Social Networks Pdf Release of information to third parties if a website service releases or sells information to a third party of a user without explicit notification to the user, it undermines a consumer’s personal privacy. The cci project builds on two years of experimentation that demonstrated the ability to generate realistic fake identities, perform one time online interactions, and subsequently collect and analyze how that information is being both used and abused across email, sms text, and voicemail modalities. Ai generated fake ids are becoming popular because they’re cheap, fast, and easy to make. with only a smartphone, anyone can generate convincing identity documents that can fool basic verification systems. traditional identity verification methods are struggling to detect them. Deepfake technology, based on artificial intelligence (ai), enables the creation of realistic images, videos, and text, bringing new possibilities and posing serious ethical, social, and legal threats. the article examines key areas in which deepfakes affect contemporary society. This manuscript presents a systematic review of deepfake generation and detection techniques from 2017 to 2025, highlighting the progression of generative models and evaluating detection strategies.

Pdf Dual Use Of Generative Ai In Cybersecurity Balancing Offensive Ai generated fake ids are becoming popular because they’re cheap, fast, and easy to make. with only a smartphone, anyone can generate convincing identity documents that can fool basic verification systems. traditional identity verification methods are struggling to detect them. Deepfake technology, based on artificial intelligence (ai), enables the creation of realistic images, videos, and text, bringing new possibilities and posing serious ethical, social, and legal threats. the article examines key areas in which deepfakes affect contemporary society. This manuscript presents a systematic review of deepfake generation and detection techniques from 2017 to 2025, highlighting the progression of generative models and evaluating detection strategies.

Suchet Bamrungpak ёяда On Linkedin Artificial Intelligence Crime An This manuscript presents a systematic review of deepfake generation and detection techniques from 2017 to 2025, highlighting the progression of generative models and evaluating detection strategies.
Comments are closed.