Update Cryptographic Storage Cheat Sheet Issue 862 Owasp

Cryptographic Storage Cheat Sheet Download Free Pdf Key What is missing or needs to be updated? in key lifetimes and rotation section it is said that: encryption keys should be changed (or rotated) based on a number of different criteria: ( ). Passwords should not be stored using reversible encryption secure password hashing algorithms should be used instead. the password storage cheat sheet contains further guidance on storing passwords.
Secure Cloud Architecture Owasp Cheat Sheet Series Pdf Cloud There are such wide varieties of products, methods and mechanisms for cryptographic storage. this cheat sheet will only focus on low level guidelines for developers and architects who are implementing cryptographic solutions. This document provides a simple but comprehensive model for implementing solutions to protect data at rest through cryptographic storage. it covers cryptographic algorithms, key management practices, secure random number generation, and architectural design considerations. Passwords should not be stored using reversible encryption secure password hashing algorithms should be used instead. the password storage cheat sheet contains further guidance on storing passwords. Cryptographic storage cheat sheet free download as pdf file (.pdf), text file (.txt) or read online for free. this document provides guidelines for securely storing sensitive data at rest using cryptography.
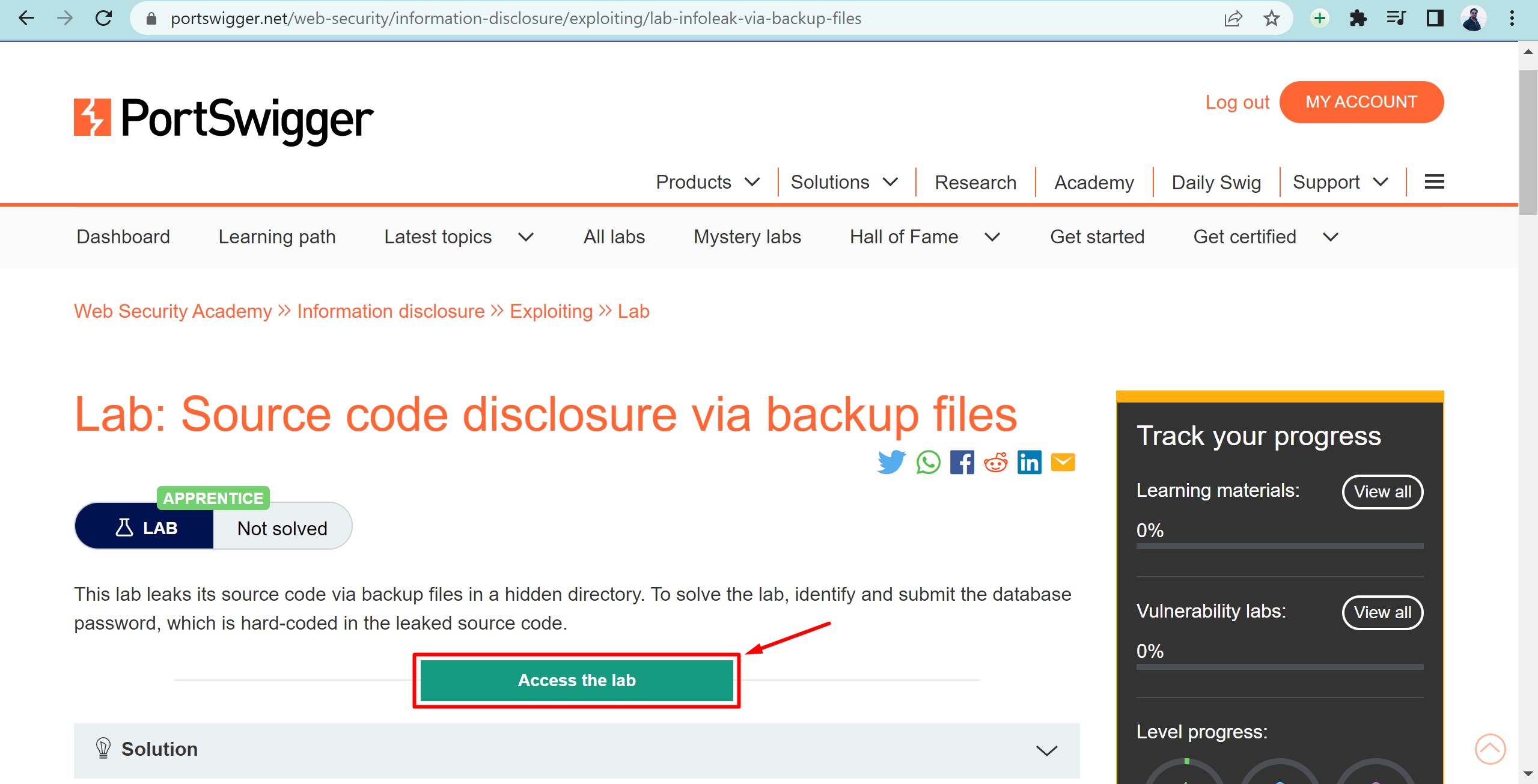
Owasp Cryptographic Failure Information Disclosure Vulnerabilities Passwords should not be stored using reversible encryption secure password hashing algorithms should be used instead. the password storage cheat sheet contains further guidance on storing passwords. Cryptographic storage cheat sheet free download as pdf file (.pdf), text file (.txt) or read online for free. this document provides guidelines for securely storing sensitive data at rest using cryptography. Applications should be designed to still be secure even if cryptographic controls fail. any information that is stored in an encrypted form should also be protected by additional layers of security. Standard : asvs : v2.8.2 : verify that symmetric keys used to verify submitted otps are highly protected, such as by using a hardware security module or secure operating system based key storage. Passwords should not be stored using reversible encryption secure password hashing algorithms should be used instead. the password storage cheat sheet contains further guidance on storing passwords. Passwords should not be stored using reversible encryption secure password hashing algorithms should be used instead. the password storage cheat sheet contains further guidance on storing passwords.

Owasp Api Security Top 10 Cheat Sheet Tabloid Pdf Applications should be designed to still be secure even if cryptographic controls fail. any information that is stored in an encrypted form should also be protected by additional layers of security. Standard : asvs : v2.8.2 : verify that symmetric keys used to verify submitted otps are highly protected, such as by using a hardware security module or secure operating system based key storage. Passwords should not be stored using reversible encryption secure password hashing algorithms should be used instead. the password storage cheat sheet contains further guidance on storing passwords. Passwords should not be stored using reversible encryption secure password hashing algorithms should be used instead. the password storage cheat sheet contains further guidance on storing passwords.

Introduction Owasp Cheat Sheet Series Passwords should not be stored using reversible encryption secure password hashing algorithms should be used instead. the password storage cheat sheet contains further guidance on storing passwords. Passwords should not be stored using reversible encryption secure password hashing algorithms should be used instead. the password storage cheat sheet contains further guidance on storing passwords.
Introduction Owasp Cheat Sheet Series
Comments are closed.