Update Available Getting Started With Splunk Threat Intelligence

Update Available Getting Started With Splunk Threat Intelligence Learn how to configure splunk’s threat intelligence management and see how it can help your team run more effective detections and investigations within splunk. more. Learn how to configure splunk’s threat intelligence management and see how it can help your team run more effective detections and investigations within splunk.

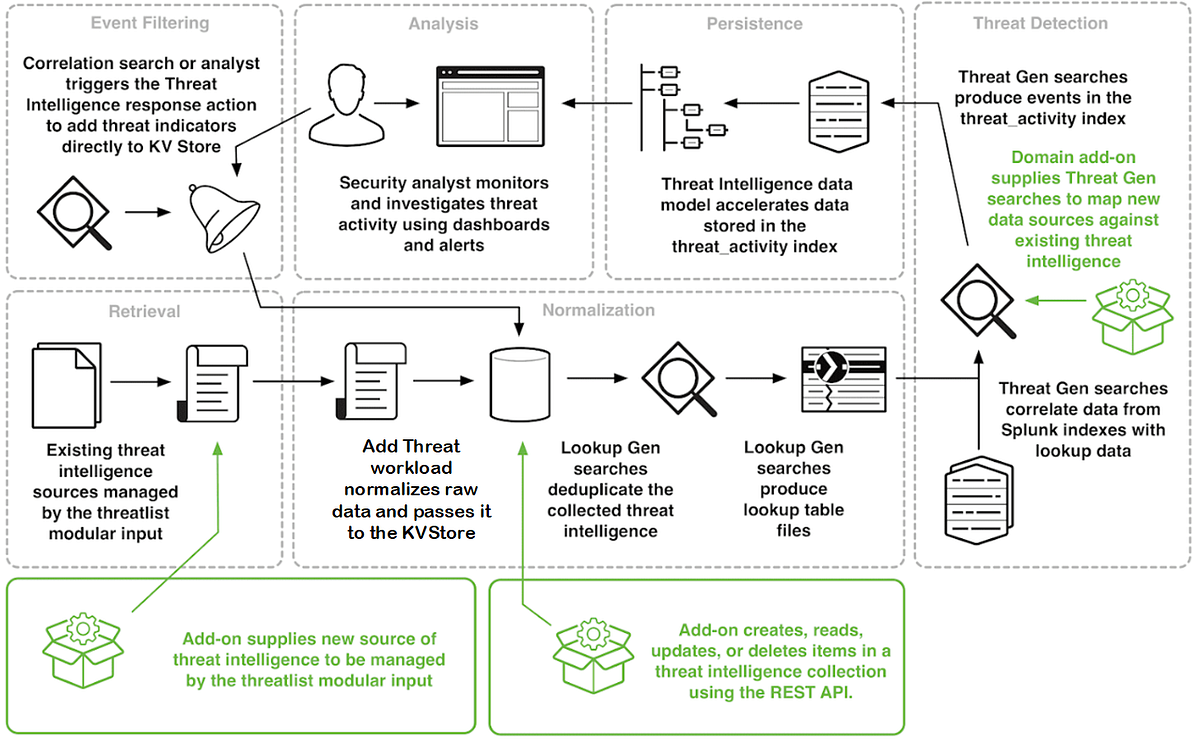
Increase The Power Of Splunk With Threat Intelligence From Recorded Future Administrators can add threat intelligence sources to splunk enterprise security by downloading a feed from the internet, uploading a structured file, or inserting the threat intelligence directly from events in splunk enterprise security. Threat intelligence management gathers data from multiple intelligence sources, such as indicators of compromise, and aggregates and prepares it for use in splunk enterprise security. In this hands on activity, we will use open source intelligence (osint) to gather threat data and then analyze security logs using splunk to detect suspicious activity. Learn how to configure and manage threat intelligence in splunk enterprise security. this guide covers data enrichment, threat matching, intel collections, correlation searches, dashboards, and more.

Threat Intelligence For Splunk Enterprise Security Hurricane Labs In this hands on activity, we will use open source intelligence (osint) to gather threat data and then analyze security logs using splunk to detect suspicious activity. Learn how to configure and manage threat intelligence in splunk enterprise security. this guide covers data enrichment, threat matching, intel collections, correlation searches, dashboards, and more. If you are just getting ready to begin with splunk threat hunting, this guide outlines a simple, accurate path. to make the most of splunk, it helps to start with the basics before looking at frameworks and tools. Autonomous threat operations (ato) enables recorded future intelligence to automatically drive threat hunting and detection workflows inside splunk right from within recorded future, reducing manual effort and accelerating response. This guide will walk through the steps of using osint tools like shodan and virustotal, ingesting security logs into splunk, and analyzing the data to identify potential threats. Splunk enterprise security is a premium application used within the splunk deployment to help with soc operations. this course will teach you how to configure various threat intelligence sources for use within splunk enterprise security.
How I Update The Socradar Threat Feed App To Feed Splunk Threat If you are just getting ready to begin with splunk threat hunting, this guide outlines a simple, accurate path. to make the most of splunk, it helps to start with the basics before looking at frameworks and tools. Autonomous threat operations (ato) enables recorded future intelligence to automatically drive threat hunting and detection workflows inside splunk right from within recorded future, reducing manual effort and accelerating response. This guide will walk through the steps of using osint tools like shodan and virustotal, ingesting security logs into splunk, and analyzing the data to identify potential threats. Splunk enterprise security is a premium application used within the splunk deployment to help with soc operations. this course will teach you how to configure various threat intelligence sources for use within splunk enterprise security.
Comments are closed.