Update 35kgithub Malicious Code Lines Which Repos
Malicious Code In Fake Github Repositories Kaspersky Official Blog Security vulnerability database inclusive of cves and github originated security advisories from the world of open source software. github is where people build software. more than 150 million people use github to discover, fork, and contribute to over 420 million projects. Malicious github repos mimic malwarebytes, lastpass, citibank, and more, luring users with trojanized code to spread stealthy malware.
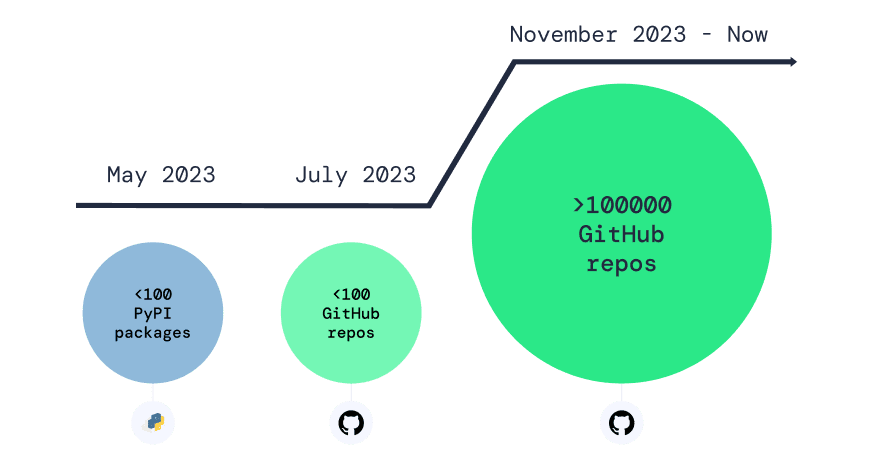
Over 100 000 Infected Repos Found On Github In the last month, "pl0xp" cloned several github repositories, adding malicious code to the forks that would attempt to infect developer systems and steal sensitive files that included. Security researchers zscaler said they observed malicious github repositories, published by a user with the name ‘dbzoomh’, claiming to be claude code’s source code with “unlocked. Malware advisories relate to vulnerabilities caused by malware, and are security advisories that github publishes automatically into the github advisory database directly from information provided by the npm security team. malware advisories are currently exclusive to the npm ecosystem. “the vulnerability can be exploited to write a malicious git hook script, resulting in remote code execution (rce) whenever subcommands like git commit and git merge are run. an attacker can.

Over 100 000 Infected Repos Found On Github Malware advisories relate to vulnerabilities caused by malware, and are security advisories that github publishes automatically into the github advisory database directly from information provided by the npm security team. malware advisories are currently exclusive to the npm ecosystem. “the vulnerability can be exploited to write a malicious git hook script, resulting in remote code execution (rce) whenever subcommands like git commit and git merge are run. an attacker can. In 2024, gitlab developers discovered two critical vulnerabilities in their system. due to verification errors, attackers could hijack user accounts and modify repository contents. this type of attack is known as repojacking. A threat group dubbed “banana squad,” active since april 2023, has trojanized more than 60 github repositories in an ongoing campaign, offering python based hacking kits with malicious. A large scale campaign is targeting developers on github with fake visual studio code (vs code) security alerts posted in the discussions section of various projects, to trick users into downloading malware. the spammy posts are crafted as vulnerability advisories and use realistic titles like “severe vulnerability – immediate update required,” often including fake cve ids and urgent. Since at least early december 2024, multiple hosts downloaded first stage payloads from malicious github repositories. the users were redirected to github through a series of other redirections.
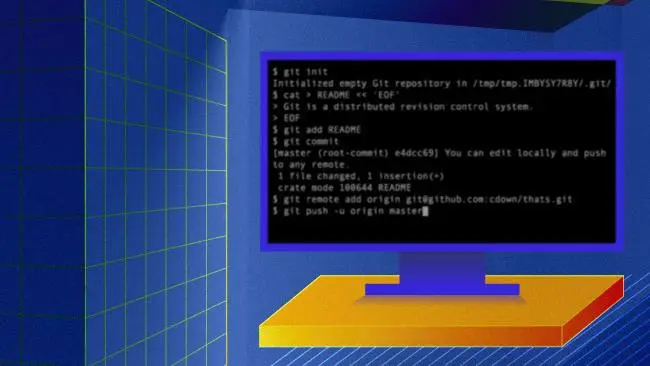
How To Stop Malicious Code Injection At Repo Infographic In 2024, gitlab developers discovered two critical vulnerabilities in their system. due to verification errors, attackers could hijack user accounts and modify repository contents. this type of attack is known as repojacking. A threat group dubbed “banana squad,” active since april 2023, has trojanized more than 60 github repositories in an ongoing campaign, offering python based hacking kits with malicious. A large scale campaign is targeting developers on github with fake visual studio code (vs code) security alerts posted in the discussions section of various projects, to trick users into downloading malware. the spammy posts are crafted as vulnerability advisories and use realistic titles like “severe vulnerability – immediate update required,” often including fake cve ids and urgent. Since at least early december 2024, multiple hosts downloaded first stage payloads from malicious github repositories. the users were redirected to github through a series of other redirections.

How To Protect Yourself From Phishing And Malware On Github And Gitlab A large scale campaign is targeting developers on github with fake visual studio code (vs code) security alerts posted in the discussions section of various projects, to trick users into downloading malware. the spammy posts are crafted as vulnerability advisories and use realistic titles like “severe vulnerability – immediate update required,” often including fake cve ids and urgent. Since at least early december 2024, multiple hosts downloaded first stage payloads from malicious github repositories. the users were redirected to github through a series of other redirections.
Comments are closed.