Unveiling Malware Behavior Trends Elastic Security Labs

Unveiling Malware Behavior Trends Elastic Security Labs An analysis of a diverse dataset of windows malware extracted from more than 100,000 samples revealing insights into the most prevalent tactics, techniques, and procedures. The following subsections contain insights into trends for malware signatures, endpoint behavior, and cloud security as observed during the prior year by elastic.

Unveiling Malware Behavior Trends Elastic Security Labs Unveiling malware behavior trends: top tactics: defense evasion, privilege escalation, execution, and persistence. lower prevalence for tactics like lateral movement, usually due to. The cybersecurity landscape has been shaken by elastic security labs’ recent discovery of two sophisticated malware families, brushworm and brushlogger, which leverage modern programming languages and stealthy persistence mechanisms to evade traditional defenses. The elastic global threat report is a report from elastic security labs that explores a full year of telemetry. the global threat report provides a comprehensive look at several threat topics, including malware, cloud, endpoint, and adversaries campaigns. The 2024 elastic global threat report from elastic security labs highlights key trends and vulnerabilities shaping the cybersecurity landscape. this report will provide valuable insight for security teams and ciso’s.
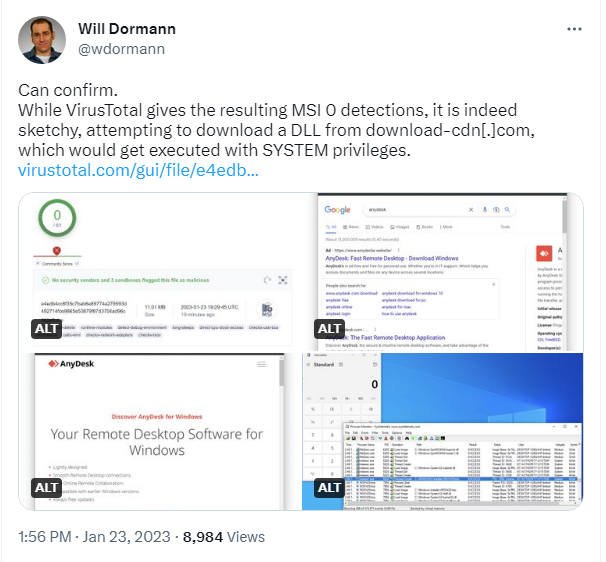
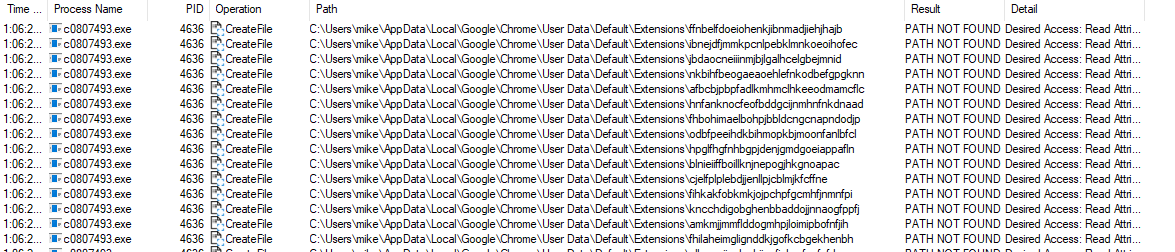
Elastic Security Labs Discovers The Lobshot Malware Elastic The elastic global threat report is a report from elastic security labs that explores a full year of telemetry. the global threat report provides a comprehensive look at several threat topics, including malware, cloud, endpoint, and adversaries campaigns. The 2024 elastic global threat report from elastic security labs highlights key trends and vulnerabilities shaping the cybersecurity landscape. this report will provide valuable insight for security teams and ciso’s. The observations in this post relate mostly to the trends in malware threats, and my own sentiments on the nuances of some of the report’s claims and observations. This report explores key telemetry from 1 billion data points with emphasis on malware trends, adversary tactics, cloud security, and generative ai curated by elastic security labs. Opinions reflect judgment at the time and are subject to change. elastic envisions security as a data problem and prioritizes features that enable customers to use that data as they see fit. Off the shelf offensive security tools (osts) and poorly configured cloud environments expose vulnerabilities in organisational defences. elastic, the search ai company (nyse: estc), has unveiled the 2024 elastic global threat report, crafted by elastic security labs.

Malware Analysis Elastic Security Labs The observations in this post relate mostly to the trends in malware threats, and my own sentiments on the nuances of some of the report’s claims and observations. This report explores key telemetry from 1 billion data points with emphasis on malware trends, adversary tactics, cloud security, and generative ai curated by elastic security labs. Opinions reflect judgment at the time and are subject to change. elastic envisions security as a data problem and prioritizes features that enable customers to use that data as they see fit. Off the shelf offensive security tools (osts) and poorly configured cloud environments expose vulnerabilities in organisational defences. elastic, the search ai company (nyse: estc), has unveiled the 2024 elastic global threat report, crafted by elastic security labs.
Elastic Security Labs Discovers The Lobshot Malware Elastic Opinions reflect judgment at the time and are subject to change. elastic envisions security as a data problem and prioritizes features that enable customers to use that data as they see fit. Off the shelf offensive security tools (osts) and poorly configured cloud environments expose vulnerabilities in organisational defences. elastic, the search ai company (nyse: estc), has unveiled the 2024 elastic global threat report, crafted by elastic security labs.
Comments are closed.