Unit2 Computer Network Pdf Computer Network Channel Access Method

Multiple Access Protocols In Computer Network Pdf Channel Access Unit 2 free download as pdf file (.pdf), text file (.txt) or view presentation slides online. the document discusses the data link layer in networking, focusing on the communication between nodes and links, and the role of the medium access control (mac) sublayer in managing channel allocation. Reservation based access methods can enable more efficient use of available bandwidth, as they allow for time and frequency multiplexing of different reservation requests on the same channel.
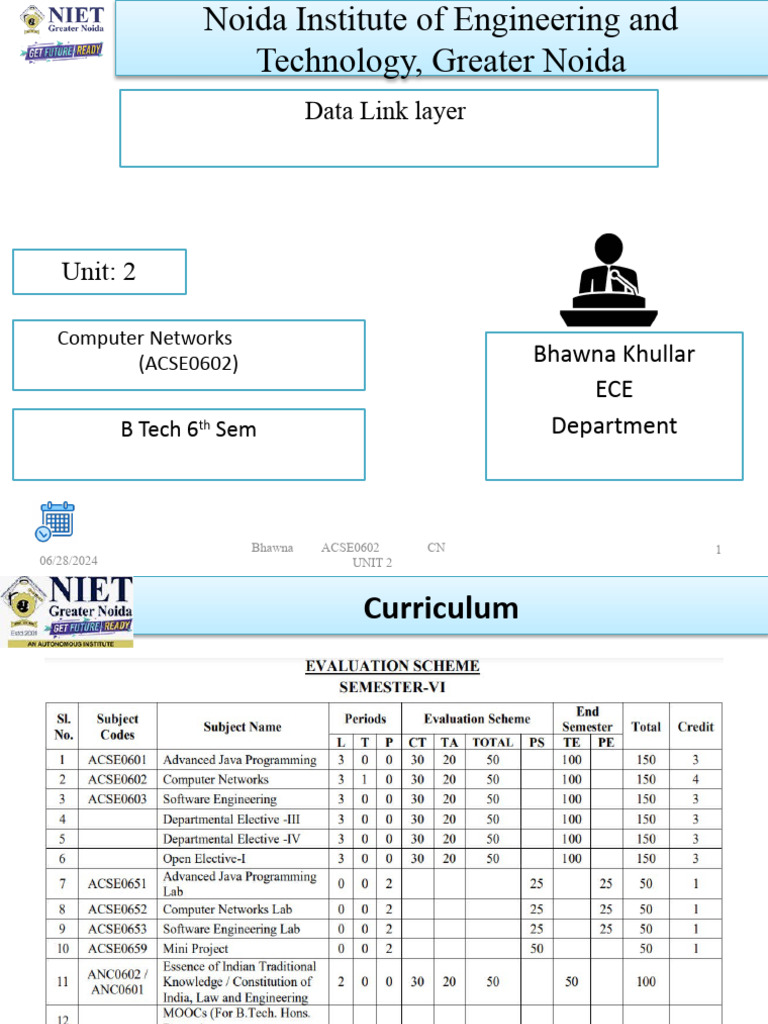
Unit2 Computer Network Pdf Error Detection And Correction Channel The communication channel that connects the adjacent nodes is known as links, and in order to move the datagram from source to the destination, the datagram must be moved across an individual link. Access method are, the means or ways by which stations actually gain the use of the common channel to transmit messages. the right to transmit is an issue only in broadcast where workstations share a single channel. Controlled access protocols : in this method, the stations consult each other to find which station has a right to send. a station cannot send unless it has been authorized by other stations. the different controlled access methods are: reservation polling. In telecommunications and computer networks, a channel access method or multiple access method allows several terminals connected to the same multi point transm ission medium to transmit over it and to share its capacity.
Data Communication Computer Network Channel Types Pdf Controlled access protocols : in this method, the stations consult each other to find which station has a right to send. a station cannot send unless it has been authorized by other stations. the different controlled access methods are: reservation polling. In telecommunications and computer networks, a channel access method or multiple access method allows several terminals connected to the same multi point transm ission medium to transmit over it and to share its capacity. Multiple access protocols for channel access control, for example csma cd protocols for collision detection and re transmission in ethernet bus networks and hub networks, or the csma ca protocol for collision avoidance in wireless networks. Encoding violation is method that is used only for network in which encoding on physical medium includes some sort of redundancy i.e., use of more than one graphical or visual structure to simply encode or represent one variable of data. This practical manual has undergone several developments since the first version used in the “ networks” course computer “. this practical guide has been corrected here and there regarding typos and updated knowledge. Data link control a data link control is a reliable channel for transmitting data over a dedicated link using various techniques such as framing, error control and flow control of data packets in the computer network.

Lecture 4 Computer Networks Layer 2 Mac Pdf Channel Access Method Multiple access protocols for channel access control, for example csma cd protocols for collision detection and re transmission in ethernet bus networks and hub networks, or the csma ca protocol for collision avoidance in wireless networks. Encoding violation is method that is used only for network in which encoding on physical medium includes some sort of redundancy i.e., use of more than one graphical or visual structure to simply encode or represent one variable of data. This practical manual has undergone several developments since the first version used in the “ networks” course computer “. this practical guide has been corrected here and there regarding typos and updated knowledge. Data link control a data link control is a reliable channel for transmitting data over a dedicated link using various techniques such as framing, error control and flow control of data packets in the computer network.
Comments are closed.