Unit 1 Part 2 Pdf Cipher Cryptanalysis

Hemanthnaik Assignment 1 Caesar Cipher Cryptanalysis Pdf Unit 1 part 2 free download as pdf file (.pdf), text file (.txt) or read online for free. the document discusses various classical encryption techniques including substitution and transposition ciphers. it covers caesar cipher, monoalphabetic ciphers like playfair cipher and hill cipher. These files were converted from the original pdf format, using pdftops, which comes with xpdf. you can either get all the parts at once, gzipped and tarred, or piecewise: enjoy!.

Unit 2 Part I Download Free Pdf Cryptanalysis Cryptography For each technique, it explains the encryption and decryption process, cryptanalysis methods, and provides examples to illustrate how the techniques work. download as a pdf, pptx or view online for free. Cryptography is used to hide information. it is not only use by spies but for phone, fax and e mail communication, bank transactions, bank account security, pins, passwords and credit card transactions on the web. So search ciphertext for pairs of identical segments, record the distance between their starting positions, such as 1, 2, , then m should divide all of i’s. i.e., m divides gcd of all i’s. Protecting data namely, substitution and transposition. units 1 and 2 of module 2 describe an important cipher method called des (data encryptio. standard) and attacks specially devised for this method. in unit 3 variants of des is disc.

Unit 2 Pdf Cryptography Cryptanalysis So search ciphertext for pairs of identical segments, record the distance between their starting positions, such as 1, 2, , then m should divide all of i’s. i.e., m divides gcd of all i’s. Protecting data namely, substitution and transposition. units 1 and 2 of module 2 describe an important cipher method called des (data encryptio. standard) and attacks specially devised for this method. in unit 3 variants of des is disc. Modern cryptanalysis: techniques for advanced code breaking 1.1st edition christopher swenson january 23, 2022. Cryptography the creation and use of secret codes and related data security mechanisms. cryptanalysis the theory and practice of “breaking” cryptographic algorithms and protocols. There is a natural tendency on the part of users and system managers to perceive little benefit from security investment until a security failure occurs. security requires regular, even constant, monitoring, and this is difficult in today‟s short term, overloaded environment. Part one examines a number of symmetric ciphers. in this chapter, we begin with a look at a general model for the symmetric encryption process; this will enable us to understand the context within which the algorithms are used. next, we examine a variety of algorithms in use before the computer era.

Ccs Cb3491 Unit 1 Notes Pdf Cipher Cryptanalysis Modern cryptanalysis: techniques for advanced code breaking 1.1st edition christopher swenson january 23, 2022. Cryptography the creation and use of secret codes and related data security mechanisms. cryptanalysis the theory and practice of “breaking” cryptographic algorithms and protocols. There is a natural tendency on the part of users and system managers to perceive little benefit from security investment until a security failure occurs. security requires regular, even constant, monitoring, and this is difficult in today‟s short term, overloaded environment. Part one examines a number of symmetric ciphers. in this chapter, we begin with a look at a general model for the symmetric encryption process; this will enable us to understand the context within which the algorithms are used. next, we examine a variety of algorithms in use before the computer era.

Unit 3 Cryptanalysis Pdf Cryptanalysis Cryptography There is a natural tendency on the part of users and system managers to perceive little benefit from security investment until a security failure occurs. security requires regular, even constant, monitoring, and this is difficult in today‟s short term, overloaded environment. Part one examines a number of symmetric ciphers. in this chapter, we begin with a look at a general model for the symmetric encryption process; this will enable us to understand the context within which the algorithms are used. next, we examine a variety of algorithms in use before the computer era.
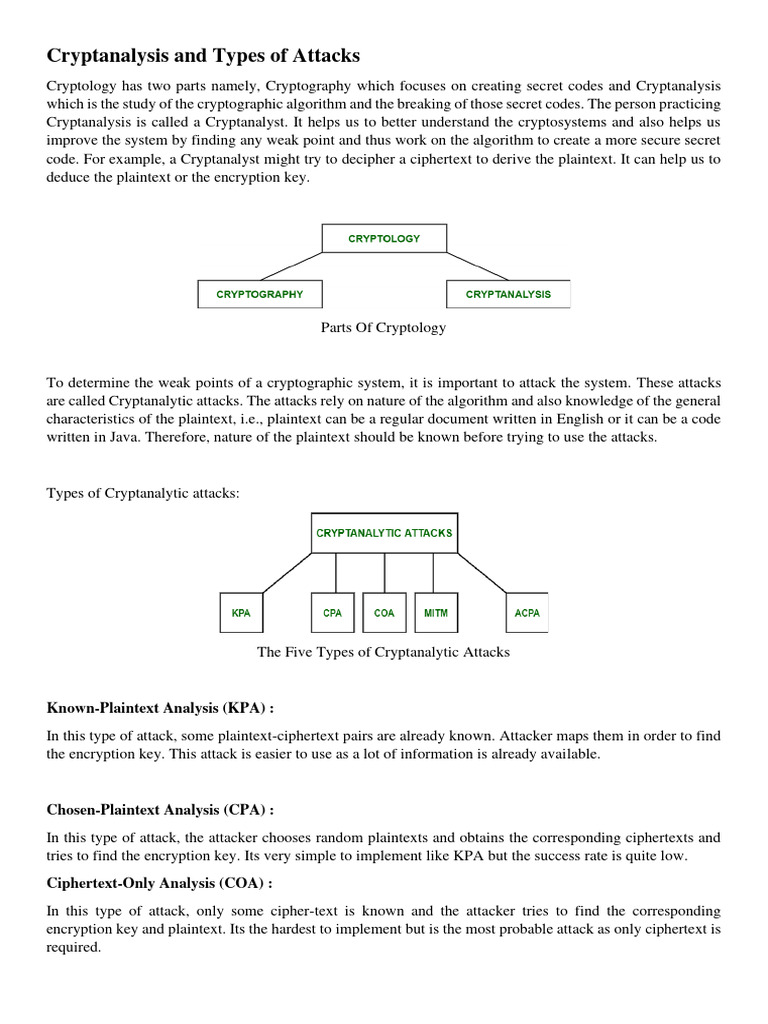
Cryptanalysis And Types Of Attacks Pdf Cryptography Cryptanalysis
Comments are closed.