Unicode Characters To Bypass Security Checks
The Unicode Blog Updated Unicode Security Specifications And Guidelines Discover how attackers use invisible unicode characters (zwsp, zwnj, nbsp) to hide malicious instructions and bypass ai security filters. learn detection and prevention techniques with free tools. The strictest option, and the one i'd actually recommend for security critical codebases: restrict source files to ascii plus a curated set of unicode characters needed for string literals and comments.

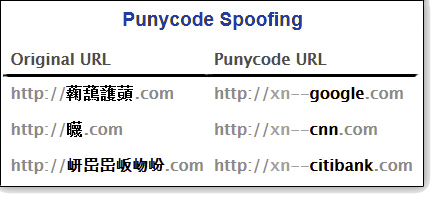
Security Bypass Icon Vector Illustration And Symbol For Website And New homoglyph attack techniques are exploiting unicode characters to impersonate trusted domains and bypass security controls. this technical analysis explains how the attack works and what organizations must do now. Using the first payload, the flask.escape () function has successfully escaped the regular characters < and > making the first payload benign. while the escape function has considered the unicode character equivalent ﹤ (u fe64) and ﹥ (u fe65) as harmless. Explore how invisible unicode characters can be used to manipulate ai coding assistants and llms, potentially leading to security vulnerabilities in your code. Cybercriminals are always exploring new tactics to evade traditional security measures, and one of the latest strategies involves using emojis and special unicode characters to hide malicious code.

Security Bypass Icon Vector Illustration And Symbol For Website And Explore how invisible unicode characters can be used to manipulate ai coding assistants and llms, potentially leading to security vulnerabilities in your code. Cybercriminals are always exploring new tactics to evade traditional security measures, and one of the latest strategies involves using emojis and special unicode characters to hide malicious code. In this article, we’ll dive into how unicode characters — especially invisible ones and bidirectional text — can be abused to bypass filters, break parsers, and even sneak malicious payloads. Depending on how the back end front end is behaving when it receives weird unicode characters an attacker might be able to bypass protections and inject arbitrary characters that could be used to abused injection vulnerabilities such as xss or sqli. To be precise, this is a story about any emoji – or for that matter, any unicode character – being used to conceal harmful or extensive text. by encoding arbitrary length data into single unicodes via zero width joiner sequences (zwj), attackers make the embedded content invisible to human reviewers, increasing the likelihood of bypassing. Security researchers and bug bounty hunters often encounter web application firewalls (wafs) and input filters that block standard payloads. one effective bypass technique involves using full width unicode characters, which can evade detection while maintaining exploit functionality.
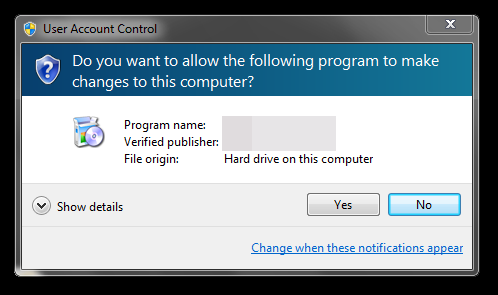
To Bypass Code Signing Checks Malware Gang Steals Lots Of Certificates In this article, we’ll dive into how unicode characters — especially invisible ones and bidirectional text — can be abused to bypass filters, break parsers, and even sneak malicious payloads. Depending on how the back end front end is behaving when it receives weird unicode characters an attacker might be able to bypass protections and inject arbitrary characters that could be used to abused injection vulnerabilities such as xss or sqli. To be precise, this is a story about any emoji – or for that matter, any unicode character – being used to conceal harmful or extensive text. by encoding arbitrary length data into single unicodes via zero width joiner sequences (zwj), attackers make the embedded content invisible to human reviewers, increasing the likelihood of bypassing. Security researchers and bug bounty hunters often encounter web application firewalls (wafs) and input filters that block standard payloads. one effective bypass technique involves using full width unicode characters, which can evade detection while maintaining exploit functionality.
Comments are closed.