Understanding Zero Trust Security And Implementation Roadmap

Zero Trust Roadmap Pdf Cloud Computing Cyberspace To help, we’ve built a vendor neutral roadmap for the entire zero trust journey, covering these five projects and others like them. some will take far longer than a few days, but the roadmap can provide greater clarity into what zero trust adoption means. Learn what zero trust security is, its core principles, why it is important, and how to implement it to protect systems from cyber threats.
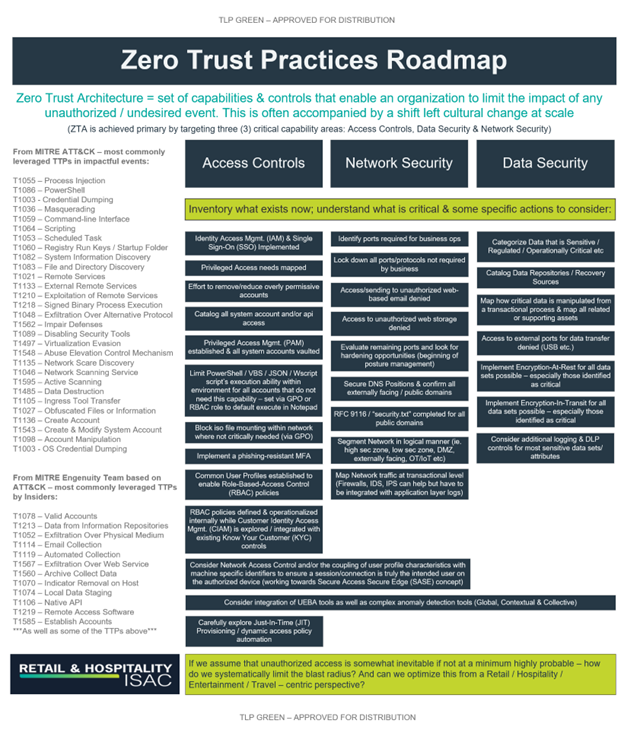
Rh Isac A Roadmap To Zero Trust Maturity Rh Isac Implementing a zero trust architecture can be done in steps without disrupting employee productivity and connectivity. this roadmap was built by security experts to provide a vendor agnostic zero trust architecture and example implementation timeline. In this blog post, we will cover the limitations of the traditional model, how zero trust models help in securing the modern web, and how to implement a zero trust model. This post was inspired by the zero trust journey takeaways outlined in nist special publication 1800 35, which offers an in depth technical roadmap for organizations looking to implement zero trust across complex environments. Simplify zero trust implementation with this detailed guide. learn the policies, compliance, and monitoring strategies to implement zero trust security.

Understanding Zero Trust Security And Implementation Roadmap This post was inspired by the zero trust journey takeaways outlined in nist special publication 1800 35, which offers an in depth technical roadmap for organizations looking to implement zero trust across complex environments. Simplify zero trust implementation with this detailed guide. learn the policies, compliance, and monitoring strategies to implement zero trust security. This guide provides a leadership focused roadmap for cisos to successfully implement zero trust principles across their organizations, transforming security posture while enabling business agility in an increasingly distributed world. Implement zero trust security in your organization. learn the framework, key technologies (ztna, microsegmentation, iam), vendor comparison, and step by step deployment guide. The preparation phase sets the stage for a successful zero trust adoption by providing a clear understanding of the current security landscape, identifying critical assets, and ensuring stakeholder alignment. Adopting a strong zero trust strategy is key to modern information security programs. cybersecurity leaders must align the strategy with business objectives and focus on risk mitigation to ensure procedural, policy or tactical decisions are made in the context of a zero trust strategy.
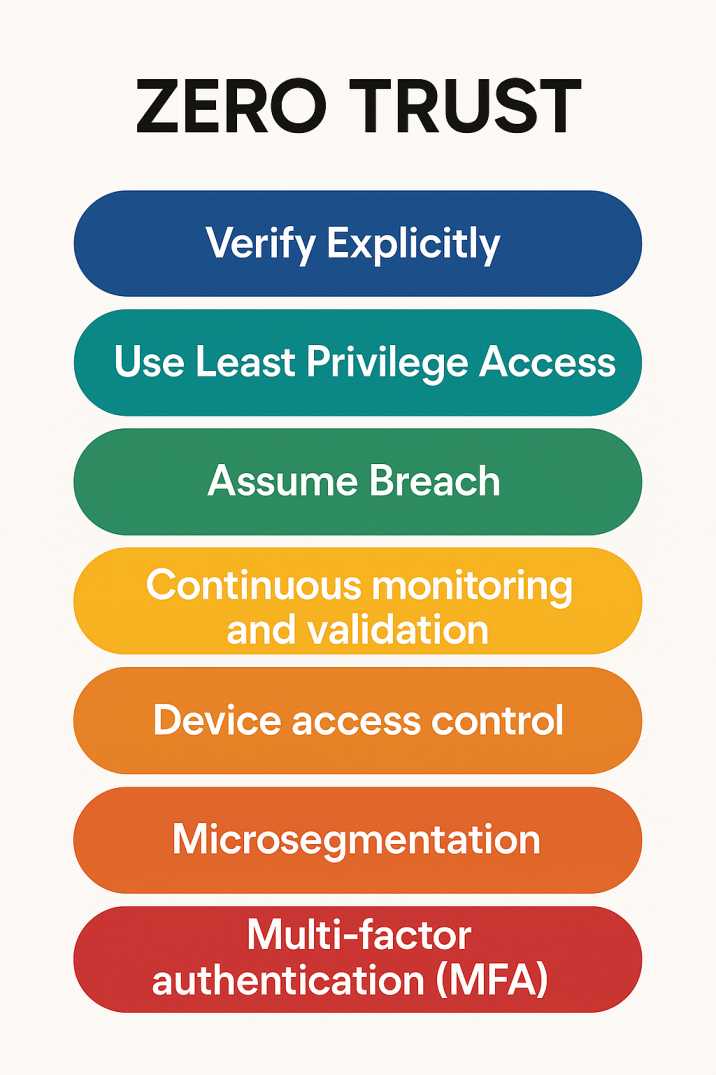
Understanding Zero Trust Security And Implementation Roadmap This guide provides a leadership focused roadmap for cisos to successfully implement zero trust principles across their organizations, transforming security posture while enabling business agility in an increasingly distributed world. Implement zero trust security in your organization. learn the framework, key technologies (ztna, microsegmentation, iam), vendor comparison, and step by step deployment guide. The preparation phase sets the stage for a successful zero trust adoption by providing a clear understanding of the current security landscape, identifying critical assets, and ensuring stakeholder alignment. Adopting a strong zero trust strategy is key to modern information security programs. cybersecurity leaders must align the strategy with business objectives and focus on risk mitigation to ensure procedural, policy or tactical decisions are made in the context of a zero trust strategy.

Roadmap To Zero Trust Implementation Securing Hybrid Cloud With Zero The preparation phase sets the stage for a successful zero trust adoption by providing a clear understanding of the current security landscape, identifying critical assets, and ensuring stakeholder alignment. Adopting a strong zero trust strategy is key to modern information security programs. cybersecurity leaders must align the strategy with business objectives and focus on risk mitigation to ensure procedural, policy or tactical decisions are made in the context of a zero trust strategy.
Comments are closed.