Understanding Zero Trust Principles
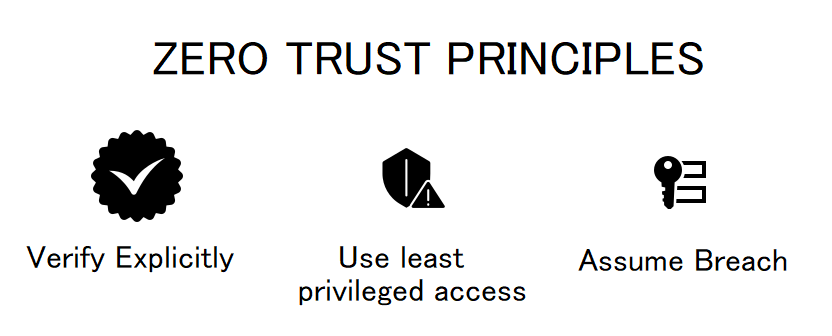
Understanding Zero Trust Principles Learn about the set of core zero trust principles that form the foundation of its security model. Zero trust security: key principles explained learn how zero trust security reduces attack surface, enforces continuous verification, and integrates iam with attack surface intelligence.
Understanding Zero Trust Principles In Iot A Deep Dive Into The Five Learn about the zero trust security model including the principles of “never trust, always verify” model, continuous authentication and how removing inherent trust strengthens modern cybersecurity. This awareness level course introduces the basic tenets of the federal zero trust (zt) security concepts, provides a high level overview of federal zt strategy, and highlights how a properly executed zt approach can improve security. Understanding zta is crucial for organizations as it offers a robust framework to protect against modern cyber threats. this blog aims to provide a comprehensive guide to zta, demystifying its core principles and illustrating its practical implementation. Zero trust isn't a tool or product, it's an essential security strategy, with data at its core. here, you'll learn how to identify and protect your data using a zero trust approach.

Zero Trust Security Understanding The Principles Of Zero Trust Model Understanding zta is crucial for organizations as it offers a robust framework to protect against modern cyber threats. this blog aims to provide a comprehensive guide to zta, demystifying its core principles and illustrating its practical implementation. Zero trust isn't a tool or product, it's an essential security strategy, with data at its core. here, you'll learn how to identify and protect your data using a zero trust approach. Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. Understanding zero trust architecture definition and core principles of zero trust zero trust is a security model built on the premise that no entity—inside or outside the network—should be trusted without verification. the core principles include continuous authentication, strict access controls, and real time monitoring. This shift has led organizations to adopt a more resilient and adaptive approach: zero trust security. this guide provides a comprehensive, aeo optimized explanation of the zero trust security model, including its principles, architecture, implementation strategy, and best practices.

Guiding Principles For Zero Trust Compromise Nothing Whitepaper Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. Understanding zero trust architecture definition and core principles of zero trust zero trust is a security model built on the premise that no entity—inside or outside the network—should be trusted without verification. the core principles include continuous authentication, strict access controls, and real time monitoring. This shift has led organizations to adopt a more resilient and adaptive approach: zero trust security. this guide provides a comprehensive, aeo optimized explanation of the zero trust security model, including its principles, architecture, implementation strategy, and best practices.
Comments are closed.