Understanding Ssh The Secure Shell Protocol
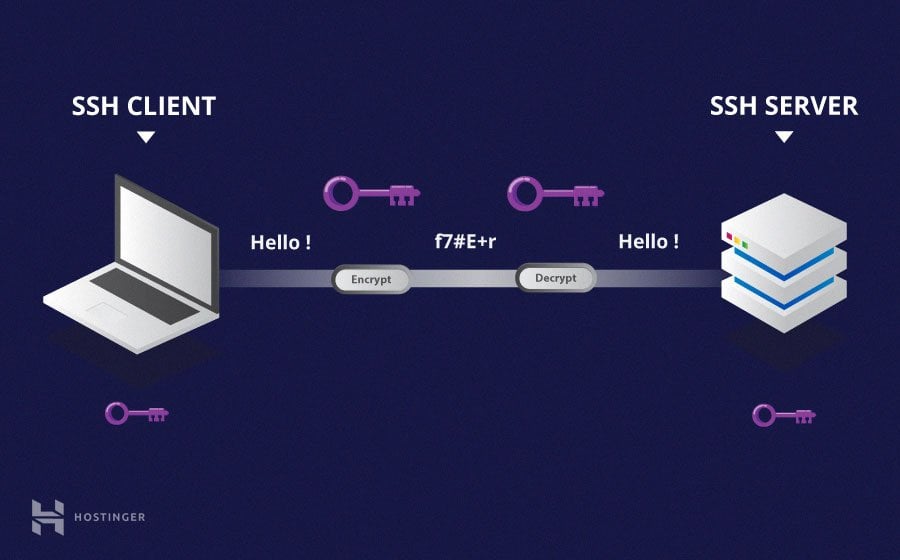
Secure Shell Protocol Ssh Msblab The ssh protocol (also referred to as secure shell) is a method for secure remote login from one computer to another. it provides several alternative options for strong authentication, and it protects communications security and integrity with strong encryption. Ssh (secure shell) is a network protocol that establishes encrypted connections between computers for secure remote access. it operates on tcp port 22 and provides authentication, encryption, and integrity to protect data transmitted over unsecured networks.
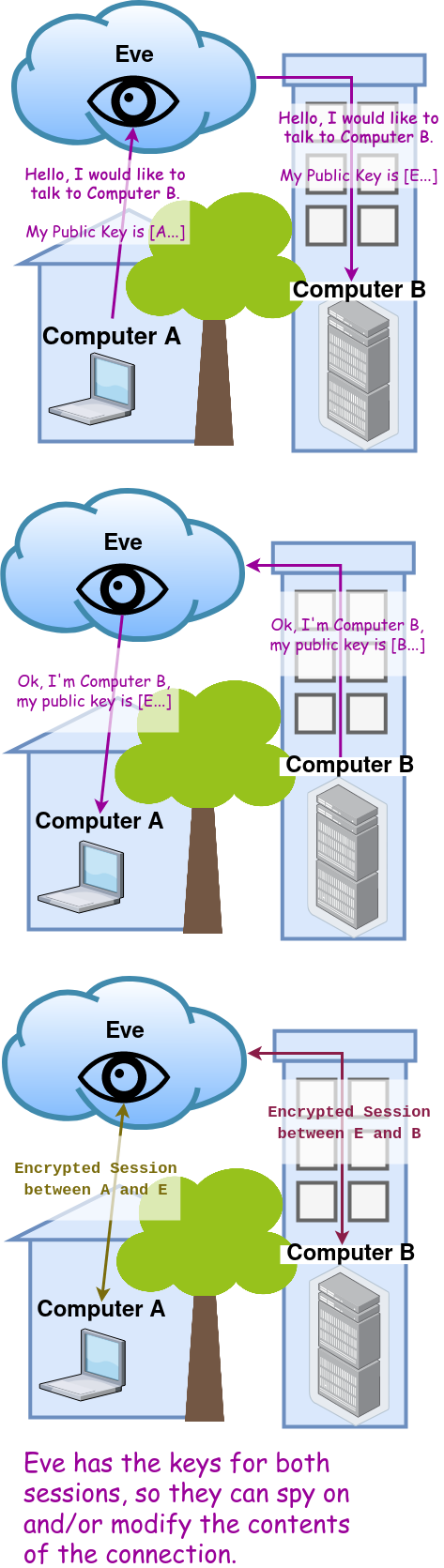
Sequentialread Understanding The Secure Shell Protocol Ssh In this ssh tutorial, we will learn how ssh works and the various mechanisms that it utilizes to securely encrypt a connection. This guide provides an in depth overview of ssh, including its configuration, public private key based authentication, advanced features, x11 forwarding, and best practices for secure usage. Using a number of encryption technologies, ssh provides a mechanism for establishing a cryptographically secured connection between two parties, authenticating each side to the other, and passing commands and output back and forth. Secure shell, or ssh, is a cryptographic network protocol that operates on the principles of encryption, key exchange, and robust authentication to secure communications over insecure networks. the functionality of ssh largely hinges on two types of encryption: symmetric and asymmetric.
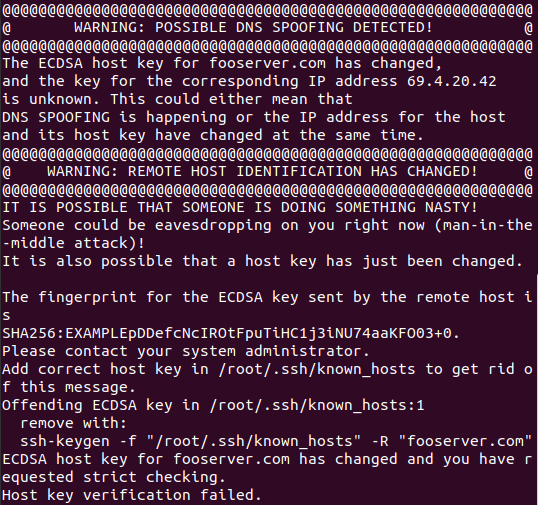
Sequentialread Understanding The Secure Shell Protocol Ssh Using a number of encryption technologies, ssh provides a mechanism for establishing a cryptographically secured connection between two parties, authenticating each side to the other, and passing commands and output back and forth. Secure shell, or ssh, is a cryptographic network protocol that operates on the principles of encryption, key exchange, and robust authentication to secure communications over insecure networks. the functionality of ssh largely hinges on two types of encryption: symmetric and asymmetric. Ssh is the go to protocol for securely connecting to machines over a network, allowing for encrypted communication and authenticated access. while it’s a tool many of us use daily,. A beginner friendly guide to ssh: what it is, how it works, and how to set up key based authentication securely. Ssh stands for secure shell, and it’s a protocol that allows you to connect to a remote computer securely over an unsecured network. ssh provides a secure channel between two computers, ensuring that data transferred between them is encrypted and protected from attackers. Ssh (secure shell or secure socket shell) is a network protocol that gives users particularly systems administrators a secure way to access a computer over an unsecured network. ssh also refers to the suite of utilities that implement the ssh protocol.
Comments are closed.