Understanding Session Hijacking Techniques Risks And Protection

Understanding Session Hijacking Techniques Risks And Protection By unraveling the complexities of session hijacking, we aim to equip you with the knowledge needed to safeguard your online presence effectively. so, let’s explore this cybersecurity threat that no one should overlook!. Learn how session hijacking bypasses mfa by stealing post authentication tokens. discover detection methods and prevention strategies for saas security teams.
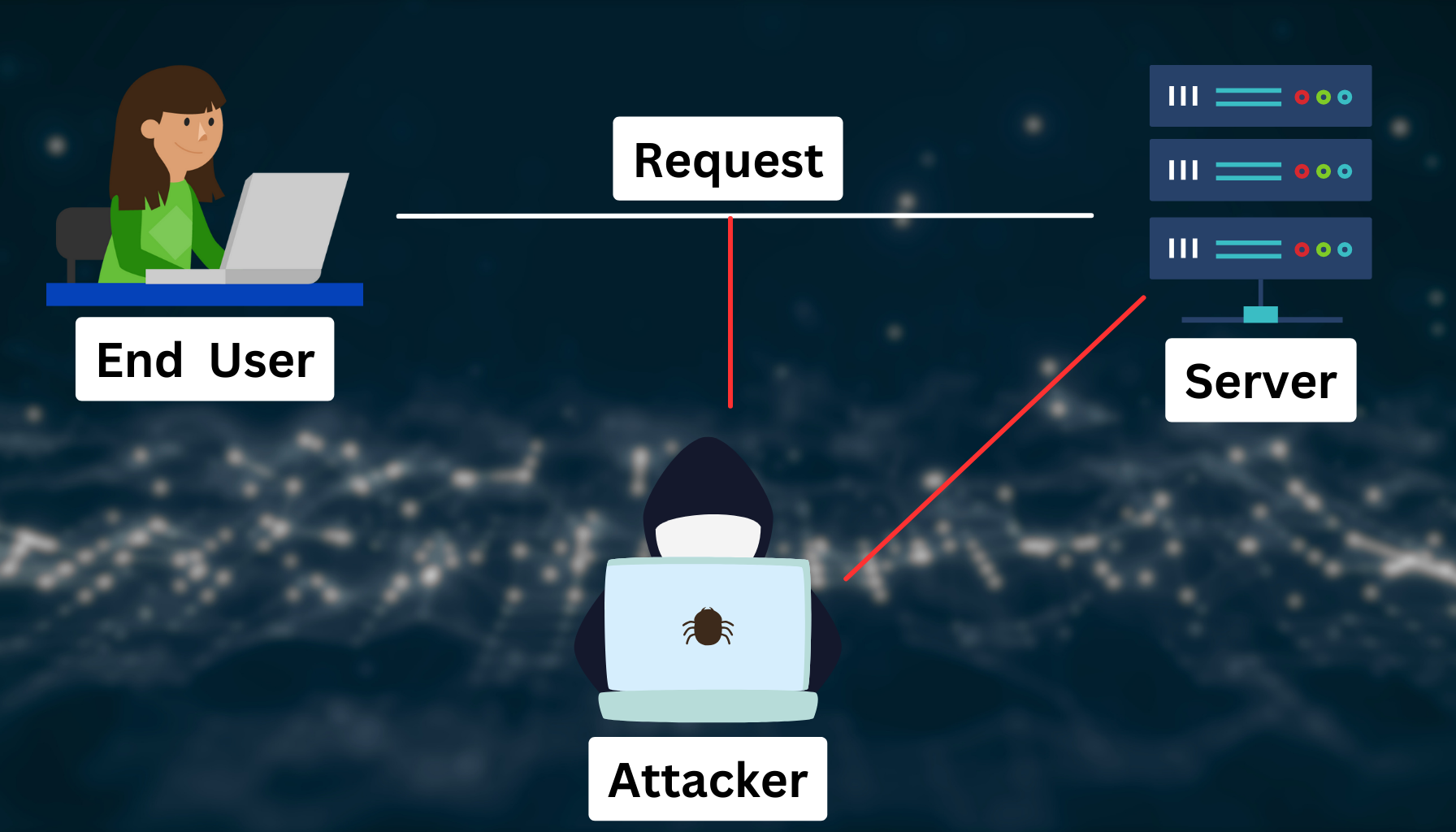
What Is Session Hijacking Understanding And Mitigating Session Hijacking What is session hijacking and how does it work? learn what session hijacking is, how it works, and the best defenses against it. discover real world examples, prevention strategies, and essential security tips to protect user sessions. Learn how session hijacking threatens your online security, discover key prevention techniques, and protect your digital identity from sophisticated cyber attacks. Session hijacking is a type of cyberattack where an attacker takes control of a user's active online session after they have authenticated themselves. attackers use various methods to steal or compromise session tokens, gaining unauthorized access to the user's account. In this guide, we’ll explore what session hijacking is, its risks, and the best strategies to protect your online sessions from being hijacked. what is session hijacking? session hijacking is a type of cyber attack where an attacker takes over a user’s session on a website or application.

Session Hijacking Attack Example And Prevention Session hijacking is a type of cyberattack where an attacker takes control of a user's active online session after they have authenticated themselves. attackers use various methods to steal or compromise session tokens, gaining unauthorized access to the user's account. In this guide, we’ll explore what session hijacking is, its risks, and the best strategies to protect your online sessions from being hijacked. what is session hijacking? session hijacking is a type of cyber attack where an attacker takes over a user’s session on a website or application. Learn what session hijacking is, how attackers exploit it, and practical steps you can take to protect your website and secure user data. In a session hijacking attack, a hacker takes control of a user’s browsing session to gain access to their personal information and passwords. this article will explain what session hijacking is, how it works, and how to prevent it from happening. Session hijacking poses significant risks in today's interconnected world. by understanding what session hijacking is, how attackers hijack a session, and implementing effective session hijacking prevention strategies, both users and developers can enhance security and protect sensitive information. Learn about session hijacking, its risks, and how to prevent it. discover tips for secure browsing and best practices to protect your online sessions from cyber threats.
Comments are closed.