Understanding Mfa Bypass Threatlocker
Mfa Bypass Attacks Intrust It As mfa transitioned to pins to address mfa fatigue, another loophole emerged—sim swapping. this method allows individuals to bypass sms rcs (text message) mfa by socially engineering the cell provider into providing the attacker with the user's sim card. While mfa is designed to bolster security, attackers often find ingenious ways to bypass it. my goal is to provide a deep dive into these techniques, sharing real world examples from my hunting.

Understanding Mfa Bypass Threatlocker Hackers bypass mfa using techniques like token theft, malware and social engineering. learn how to defend your accounts effectively and avoid common pitfalls. During one of our ransomware simulation engagements, we were met with a selection of hosts utilising threatlocker – a commonly used application whitelisting zero trust tool. Once adversaries have gained access to a network by either compromising an account lacking mfa or by employing an mfa bypass method such as multi factor authentication request generation, adversaries may leverage their access to modify or completely disable mfa defenses. In this post, we will analyze the technical mechanics of this attack, which utilizes a transparent reverse proxy on serverless infrastructure to intercept and modify server responses in real time.
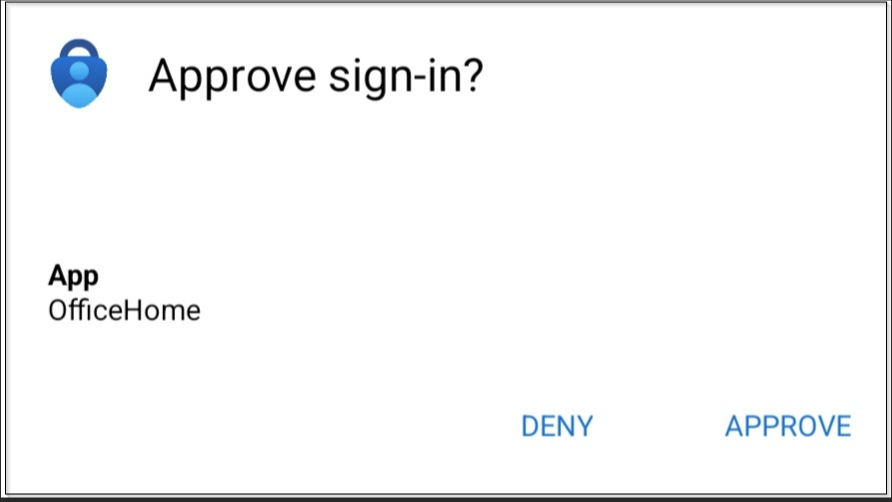
Understanding Mfa Bypass Threatlocker Once adversaries have gained access to a network by either compromising an account lacking mfa or by employing an mfa bypass method such as multi factor authentication request generation, adversaries may leverage their access to modify or completely disable mfa defenses. In this post, we will analyze the technical mechanics of this attack, which utilizes a transparent reverse proxy on serverless infrastructure to intercept and modify server responses in real time. Implementing mfa and providing proper training to avoid these attacks is the solution. watch this clip with threatlocker® ceo danny jenkins and cpo rob allen to learn why this is so important. While mfa mitigates many of the security issues involved with single factor authentication, there are multiple techniques cybercriminals use to bypass it. in this blog, we will explore the prevalent methods and discuss different ways to help you prevent and mitigate mfa bypass attacks. Mfa greatly improves security compared to conventional password systems, but this blog will examine the strategies utilized to bypass mfa, the vulnerabilities that facilitate these attacks, and the actions organizations can undertake to strengthen their defenses against this escalating threat. In this section, we’ll explore the most common mfa bypass tactics, including fatigue attacks, phishing, sim swapping, session hijacking, and more—so you can recognize and prevent them before they compromise your systems.

Understanding Mfa Bypass Threatlocker Implementing mfa and providing proper training to avoid these attacks is the solution. watch this clip with threatlocker® ceo danny jenkins and cpo rob allen to learn why this is so important. While mfa mitigates many of the security issues involved with single factor authentication, there are multiple techniques cybercriminals use to bypass it. in this blog, we will explore the prevalent methods and discuss different ways to help you prevent and mitigate mfa bypass attacks. Mfa greatly improves security compared to conventional password systems, but this blog will examine the strategies utilized to bypass mfa, the vulnerabilities that facilitate these attacks, and the actions organizations can undertake to strengthen their defenses against this escalating threat. In this section, we’ll explore the most common mfa bypass tactics, including fatigue attacks, phishing, sim swapping, session hijacking, and more—so you can recognize and prevent them before they compromise your systems.
Comments are closed.