Understanding Jwt Basics And Security Risks Laburity

Understanding Jwt Basics And Security Risks Laburity Understanding jwt token vulnerabilities is vital for keeping authentication systems safe. with the right knowledge and examples, security experts can find and fix problems, making sure digital environments stay secure. While i generally advise against it for security reasons, there are indeed a few niche scenarios where storing a jwt token in local storage might be considered acceptable, albeit with significant caveats and a deep understanding of the risks involved.
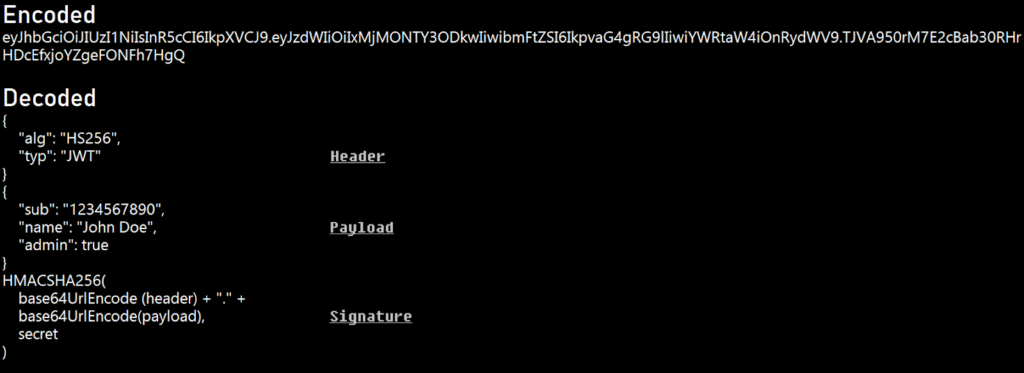
Understanding Jwt Basics And Security Risks Laburity Master jwt authentication with our comprehensive guide. learn implementation best practices, security measures, and advanced protection strategies for your web applications. By understanding both the fundamentals and security challenges, and by implementing robust security measures, you can harness the benefits of jwts while maintaining strong security. This article explains how jwt (json web token) works. it also details the vulnerabilities, attacks and best practices to secure the implementation of jwt. In this comprehensive guide, you'll learn the inner workings of jwt tokens, their structure, security best practices, common vulnerabilities, debugging techniques, and implementation examples in 8 programming languages.

Understanding Jwt Basics And Security Risks Laburity This article explains how jwt (json web token) works. it also details the vulnerabilities, attacks and best practices to secure the implementation of jwt. In this comprehensive guide, you'll learn the inner workings of jwt tokens, their structure, security best practices, common vulnerabilities, debugging techniques, and implementation examples in 8 programming languages. Learn how to exploit and defend against real world jwt vulnerabilities like algorithm confusion, weak secrets, and kid injection — with hands on labs from pentesterlab. If you’re a penetration tester or bug bounty hunter, understanding jwt vulnerabilities isn’t just useful; it’s essential. this blog will walk you through the very basics that you need to know about jwt security testing. Learn how jwt works, understand the most common security vulnerabilities, and apply proven best practices to protect tokens in production authentication systems. In this blog, we’ll demystify jwt security, explore the risks of unencrypted tokens, clarify when encryption is necessary, and outline best practices to keep your jwts secure.
Comments are closed.