Understanding Encryption Code Violations What You Need To Know

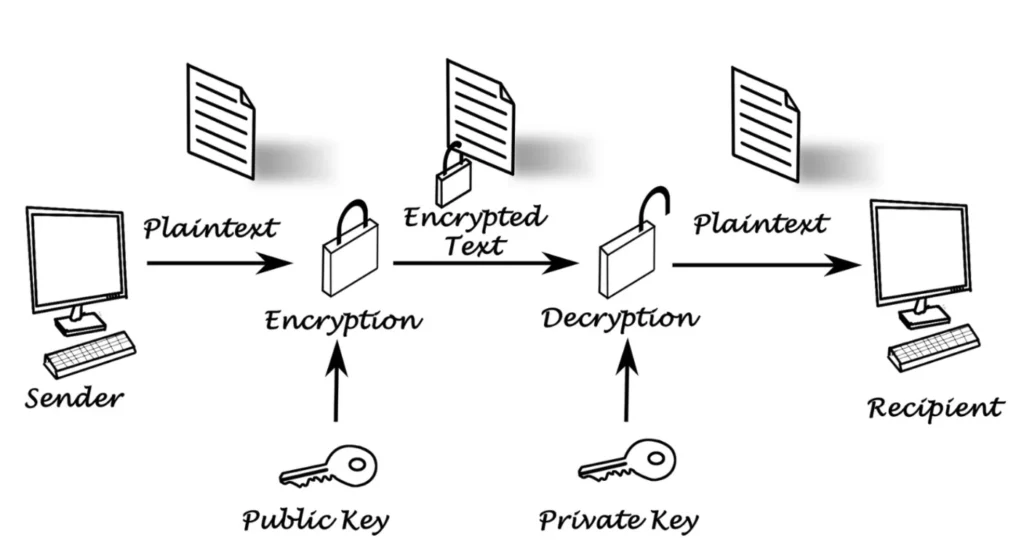
Encryption Pdf Internet Ethics Computer Network Security Are you facing an encryption code violation? 🤔 find out what it means and how to troubleshoot this issue with your downloads! 🚀💬. Essentially, any scenario where data that should have been encrypted or securely stored is left vulnerable – whether by using no encryption, weak encryption, or mismanaging keys and secrets – can be considered a cryptographic failure.

Understanding Nyc Code Violations What You Need To Know 3 Important Cryptographic failures are security weaknesses that compromise how data is protected at rest, in transit, and during use. such failures occur when cryptography is applied incorrectly. for example, sensitive data may be encrypted during transport but stored in plaintext at rest. Cryptographic failures (previously called “sensitive data exposure” in the owasp top ten) refer to vulnerabilities that occur due to the incorrect implementation, configuration, or use of. Learn how to conduct a code security audit. understand its importance, identify vulnerabilities, and follow best practices to keep your code secure and compliant. Cryptographic failures occur when the mechanisms and protocols designed to secure data and communications through encryption break down, become compromised, or fail to perform as expected.

Encryption Explained What You Need To Know Securityxperts Ca Learn how to conduct a code security audit. understand its importance, identify vulnerabilities, and follow best practices to keep your code secure and compliant. Cryptographic failures occur when the mechanisms and protocols designed to secure data and communications through encryption break down, become compromised, or fail to perform as expected. With the rise of cyber threats, understanding how digit code crackers operate is crucial. in this post, we’ll delve into the mechanisms behind code cracking, the risks involved, and how you can fortify your defenses. 🔐. Continuing on in our encryption 101 series, where we gave a malware analyst’s primer on encryption and demonstrated encryption techniques using shione ransomware, we now look at what it takes to break an encryption. While encryption is indispensable in protecting privacy and securing communications, it has become a major obstacle for authorities trying to access encrypted data during criminal investigations. Find weaknesses in encryption methods and understand when and why encryption fails to protect your data. learn how to strengthen your digital defenses.
Understanding Encryption Crash Offsce With the rise of cyber threats, understanding how digit code crackers operate is crucial. in this post, we’ll delve into the mechanisms behind code cracking, the risks involved, and how you can fortify your defenses. 🔐. Continuing on in our encryption 101 series, where we gave a malware analyst’s primer on encryption and demonstrated encryption techniques using shione ransomware, we now look at what it takes to break an encryption. While encryption is indispensable in protecting privacy and securing communications, it has become a major obstacle for authorities trying to access encrypted data during criminal investigations. Find weaknesses in encryption methods and understand when and why encryption fails to protect your data. learn how to strengthen your digital defenses.
Comments are closed.