Understanding Cryptographic Hash Functions Pdf Cryptography Error

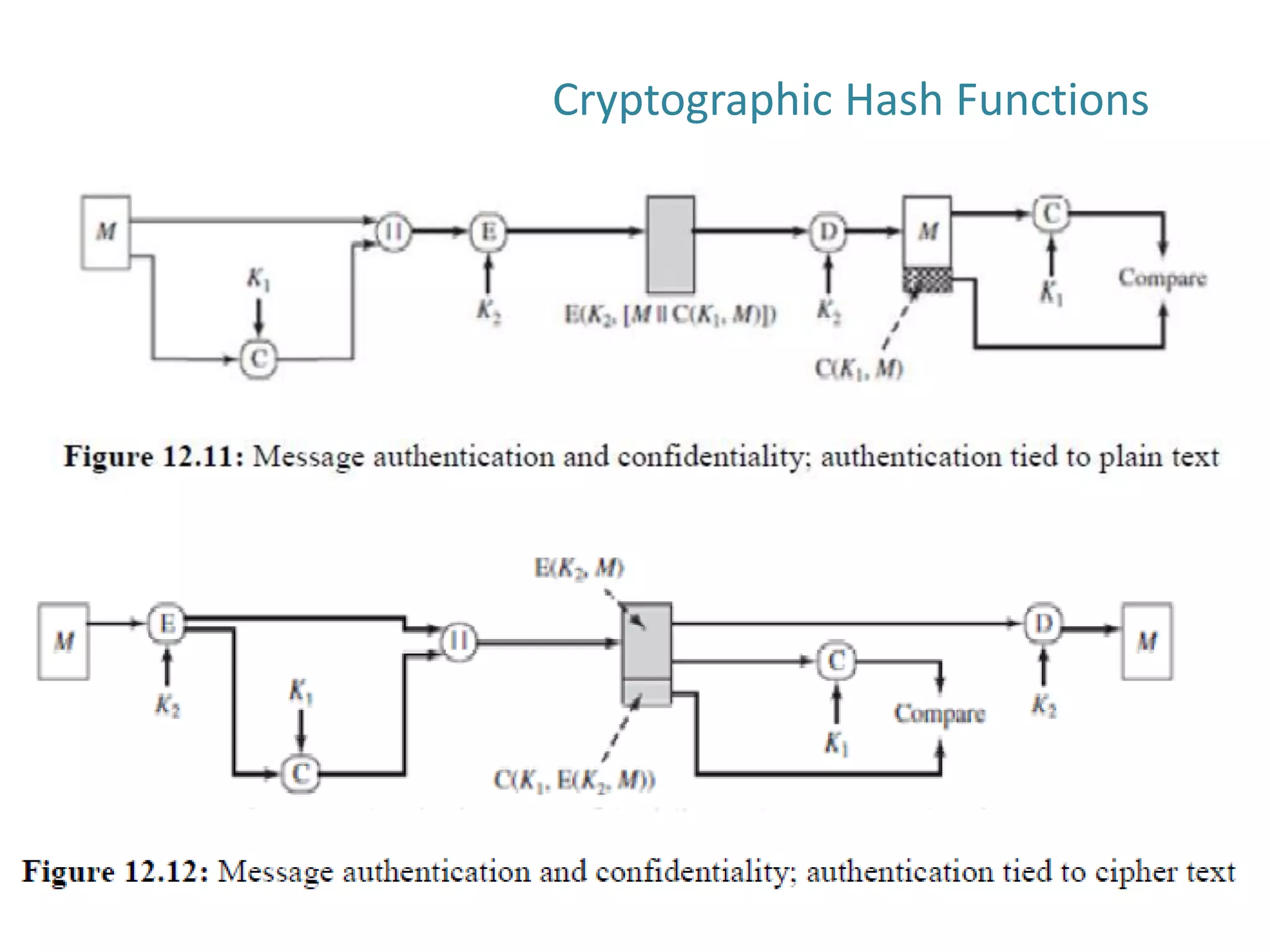
Cryptographic Hash Functions Pdf Cryptography Security Engineering This paper describes what cryptographic hash functions are, what security properties are expected of them and what attacks can be performed against them. The essence of the use of a hash function for message integrity is as follows. the sender computes a hash value as a function of the bits in the message and transmits both the hash value and the message.
Cryptography Network Security Cryptographic Hash Functions Pdf Nist have issued a revision fips 180 2 that adds 3 additional hash algorithms: sha 256, sha 384, sha 512, designed for compatibility with increased security provided by aes. These slides are based partly on lawrie brown’s slides supplied with william stallings’s book “cryptography and network security: principles and practice,” 5th ed, 2011. A cryptographic hash function has the same properties as ordinary hash functions: it is easy to compute, takes an arbitrarily long input string (or file), and it produces a random looking, fixed length, output string. In cryptography, a hash function is a specialized mathematical function that maps input data of arbitrary size to a fixed size output (called the hash or digest).
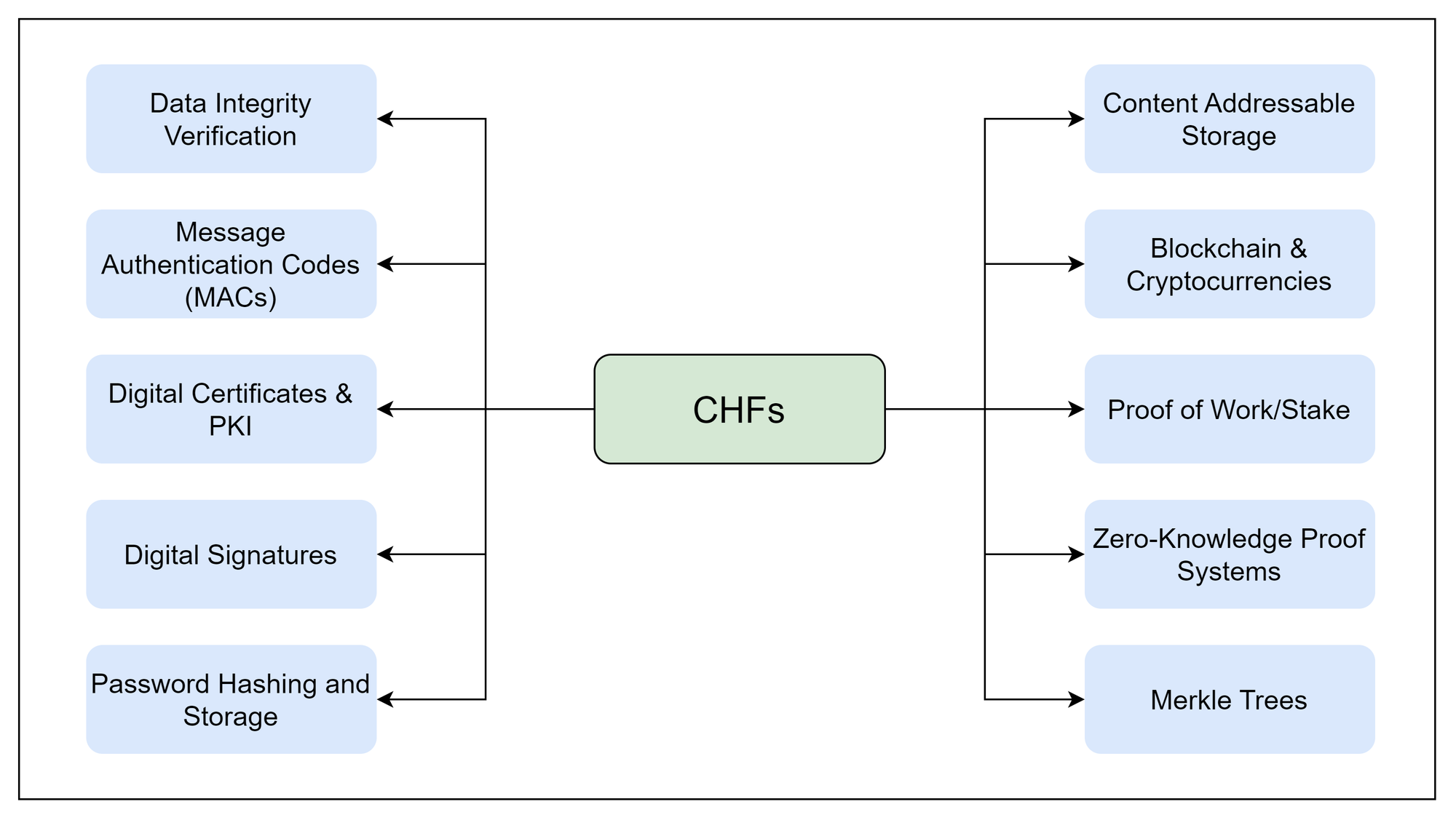
Introduction Hash Functions In Cryptography A cryptographic hash function has the same properties as ordinary hash functions: it is easy to compute, takes an arbitrarily long input string (or file), and it produces a random looking, fixed length, output string. In cryptography, a hash function is a specialized mathematical function that maps input data of arbitrary size to a fixed size output (called the hash or digest). Parallelhash: a variable length hash function that can hash very long messages in parallel nist recommended four types of sha 3 derived functions which are mentioned as follows:. P1 and p2 could be domain names in a certificate, images, pdfs, etc. any digital image. this is one of the two ways md5 is broken (other is plain old collision resistance), and is how we generated the two images with the same md5 sum for the example from the citizen lab report. Hash function (inf.): a function h that maps a long input string to a short, fixed length, output string. A cryptographic hash function “binds” the bytes of a file together in a way that makes any alterations to the file apparent. we say that we seal the file to make it tamper proof (actually tamper resistant).

2 Cryptographic Hash Functions Pptx Free Download Parallelhash: a variable length hash function that can hash very long messages in parallel nist recommended four types of sha 3 derived functions which are mentioned as follows:. P1 and p2 could be domain names in a certificate, images, pdfs, etc. any digital image. this is one of the two ways md5 is broken (other is plain old collision resistance), and is how we generated the two images with the same md5 sum for the example from the citizen lab report. Hash function (inf.): a function h that maps a long input string to a short, fixed length, output string. A cryptographic hash function “binds” the bytes of a file together in a way that makes any alterations to the file apparent. we say that we seal the file to make it tamper proof (actually tamper resistant).

2 Cryptographic Hash Functions Pptx Hash function (inf.): a function h that maps a long input string to a short, fixed length, output string. A cryptographic hash function “binds” the bytes of a file together in a way that makes any alterations to the file apparent. we say that we seal the file to make it tamper proof (actually tamper resistant).

Cryptographic Hash Function Pdf
Comments are closed.