Understanding Conditional Access 2024 Complete Guide

What Is Conditional Access Kamind It Conditional access is a security feature provided by entra id to p1 and p2 premium tenants. it lets you implement policies that control access to applications and resources based on certain conditions or criteria, including user identity, device compliance, location, and more. Explore microsoft entra conditional access, the zero trust policy engine that integrates signals to secure access to resources.
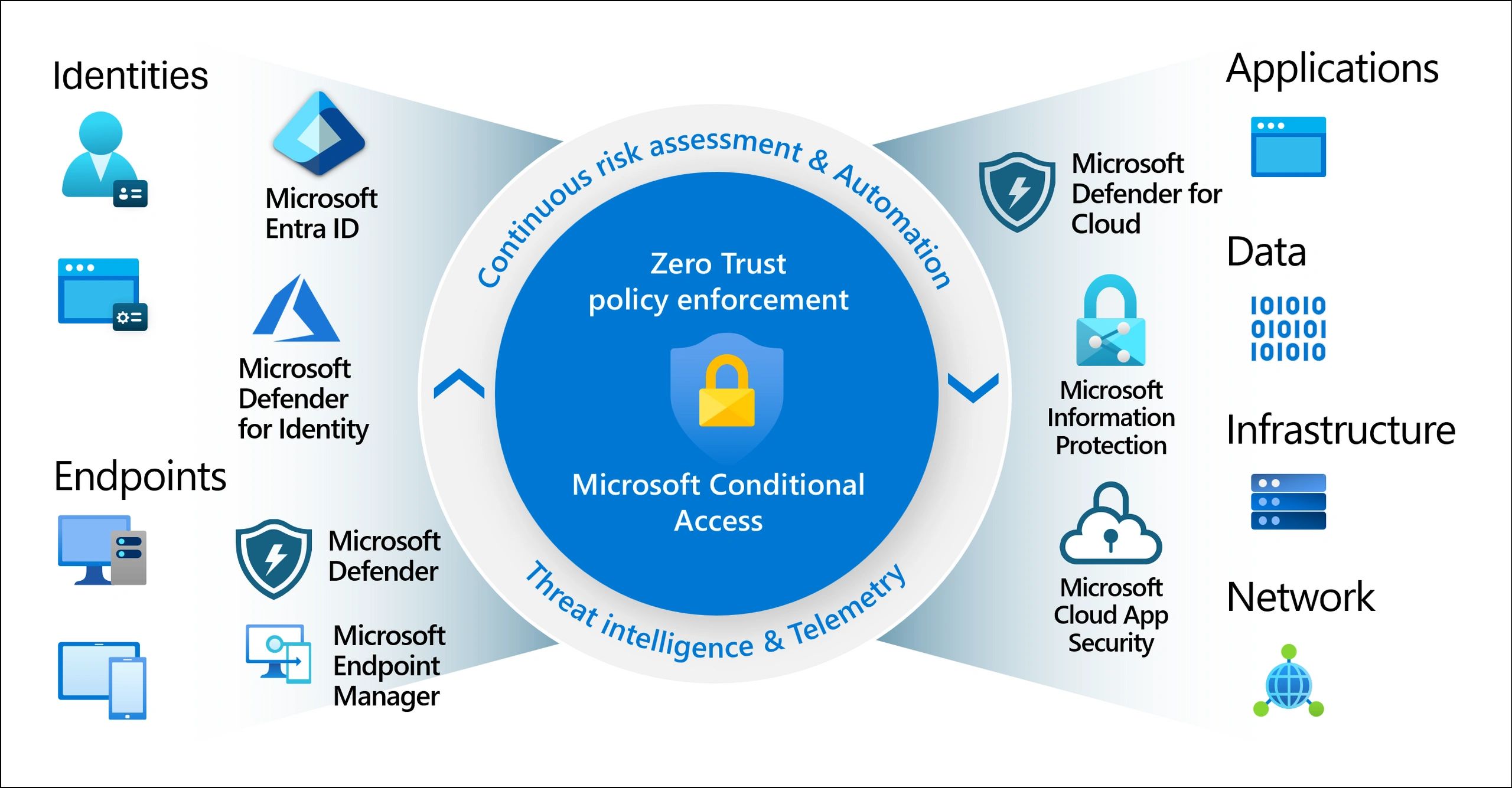
Conditional Access Policies An In Depth Guide Learn how microsoft entra id conditional access policies work, common misconfigurations that create security gaps, and how to validate policy enforcement for zero trust security. This article compiles all of microsoft’s explicit conditional access recommendations from official documentation into one structured, actionable reference. each recommendation includes a direct link to the source material for further context and detail. Conditional access (ca) policies are a cornerstone of identity security in microsoft entra id (formerly azure ad). they help control how and when users access resources. Master conditional access in microsoft entra id. secure your organization with top practices for device code flow, authentication, and compliance.

How To Monitor Conditional Access Policy Changes Conditional access (ca) policies are a cornerstone of identity security in microsoft entra id (formerly azure ad). they help control how and when users access resources. Master conditional access in microsoft entra id. secure your organization with top practices for device code flow, authentication, and compliance. Discover the essentials of microsoft entra conditional access in this beginner friendly guide. learn how to implement foundational policies that secure your environment with zero trust principles—assume breach, verify explicitly, and use least privilege access. Conditional access simplifies restricting access to company data or system functions according to job requirements. it streamlines identity management by consolidating all components within the same system for access and multi factor authentication rules. Think of it as the bridge between productivity and protection. this guide will walk through what is conditional access, why it matters, and how enterprises are adopting it as a foundation of identity first security. At their simplest, conditional access policies are ‘if then’ statements; if a user wants to access a resource, then they must complete an action. these kinds of policies make it harder for threat actors to access data and networks they shouldn’t, reducing the risk of a cyberattack or breach.
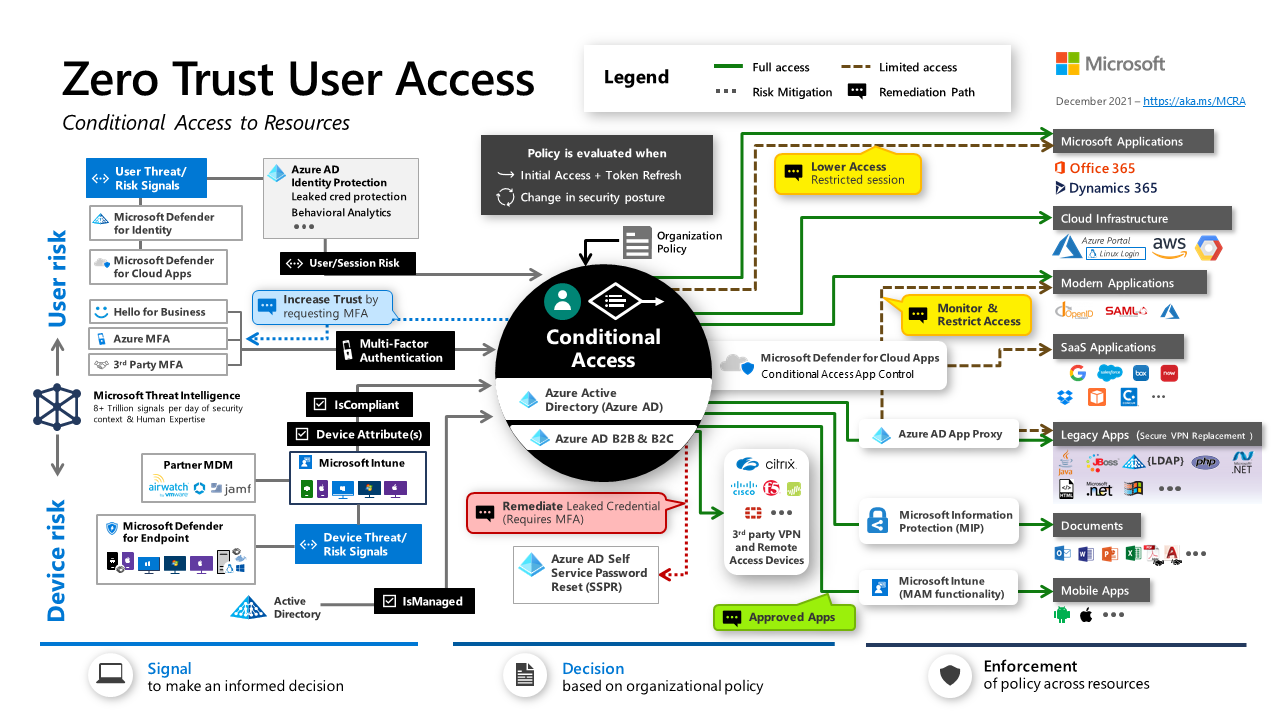
Conditional Access Design Principles And Dependencies Azure Discover the essentials of microsoft entra conditional access in this beginner friendly guide. learn how to implement foundational policies that secure your environment with zero trust principles—assume breach, verify explicitly, and use least privilege access. Conditional access simplifies restricting access to company data or system functions according to job requirements. it streamlines identity management by consolidating all components within the same system for access and multi factor authentication rules. Think of it as the bridge between productivity and protection. this guide will walk through what is conditional access, why it matters, and how enterprises are adopting it as a foundation of identity first security. At their simplest, conditional access policies are ‘if then’ statements; if a user wants to access a resource, then they must complete an action. these kinds of policies make it harder for threat actors to access data and networks they shouldn’t, reducing the risk of a cyberattack or breach.
Comments are closed.