Understanding And The Mitigating Ransomware Attacks

Understanding And The Mitigating Ransomware Attacks This whitepaper discusses the stages of a ransomware attack and the ransomware kill chain, recent ransomware trends, and mitigation strategies for organizations. Ransomware attacks have arisen as an inescapable and monetarily inspired digital danger, focusing on people, organizations, and basic framework around the world.

Understanding And Mitigating Ransomware Attacks Pdf By understanding the evolving threat and adopting comprehensive defense strategies, organizations can better safeguard their operations and resilience against ransomware attacks. In this blog, we delve into the intricacies of ransomware attacks and outline prevention techniques, response strategies, and recovery plans to help you protect your business. Part 1 provides guidance for all organizations to reduce the impact and likelihood of ransomware incidents and data extortion, including best practices to prepare for, prevent, and mitigate these incidents. prevention best practices are grouped by common initial access vectors. This research paper provides an overview of ransomware, its evolution, mechanisms, impact on victims, and preventive measures. this paper also delves into the intricate details of ransomware, including its structure, infection vectors, and proactive mitigation strategies.
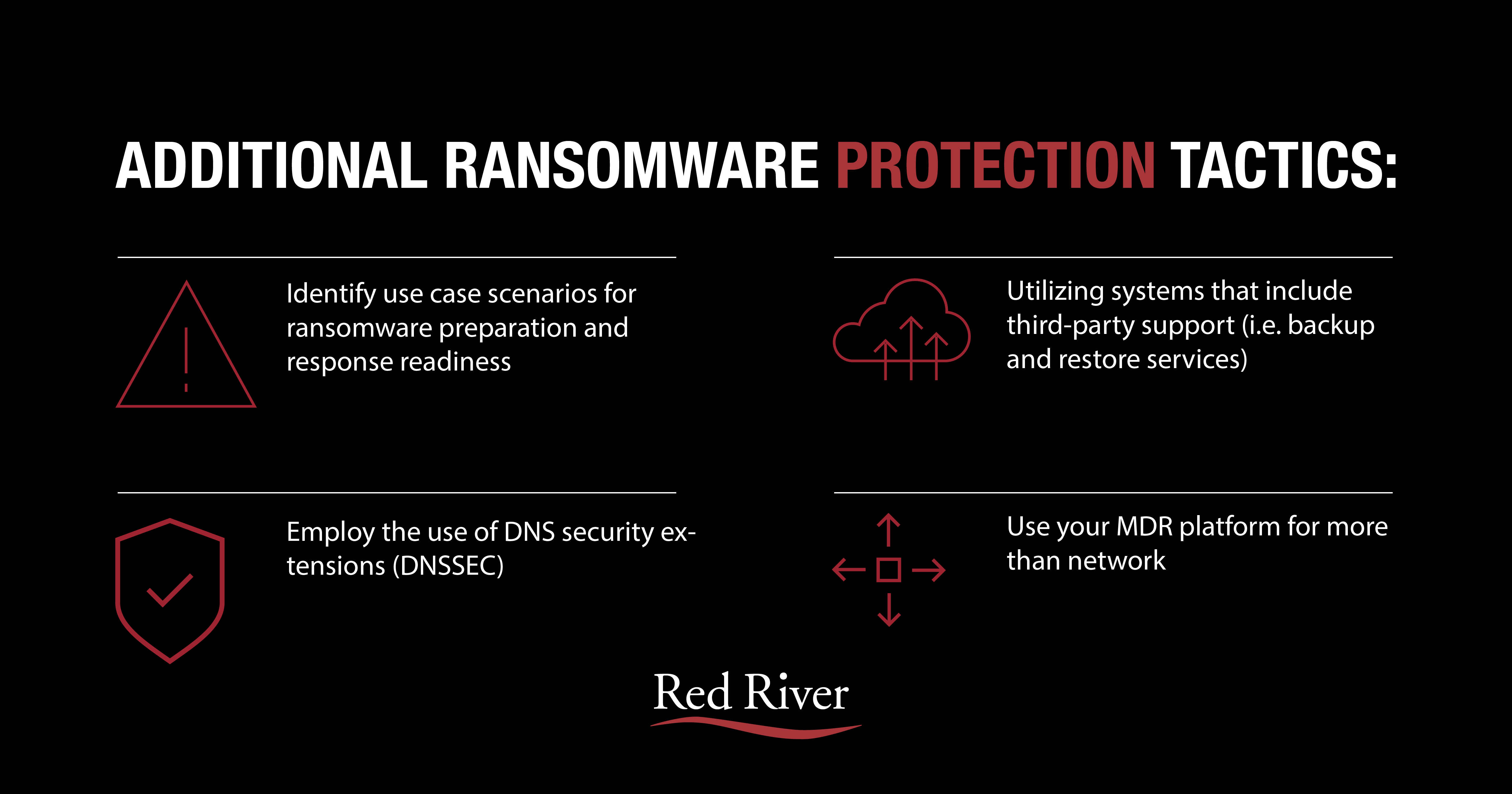
Key Recommendations To Help Mitigate Ransomware Part 1 provides guidance for all organizations to reduce the impact and likelihood of ransomware incidents and data extortion, including best practices to prepare for, prevent, and mitigate these incidents. prevention best practices are grouped by common initial access vectors. This research paper provides an overview of ransomware, its evolution, mechanisms, impact on victims, and preventive measures. this paper also delves into the intricate details of ransomware, including its structure, infection vectors, and proactive mitigation strategies. Ransomware mitigation strategies are put into place to prevent or respond to ransomware attacks. learn more about ransomware mitigation best practices and tools. The anatomy of the ransomware lifecycle ransomware has evolved into a sophisticated and pervasive threat, infiltrating organizations through various stages in its lifecycle. rney is crucial for developing efective defense strategies. this chapter delves into the anatomy of the ransomware lifecycle, exploring the key phases from. As ransomware attacks become more sophisticated, they pose ever greater risks, necessitating continuous evolution in defence mechanisms. this paper has highlighted the complex nature of ransomware, its evolution, and its operational mechanics, while also discussing effective mitigation strategies. Ransomware attacks continue to evolve, leveraging sophisticated techniques to infiltrate systems, encrypt data, and demand payment. understanding the ransomware kill chain—the stages an attacker follows—is critical for cybersecurity professionals to detect, prevent, and respond effectively.

Understanding And Mitigating Ransomware Attacks Ppt Ransomware mitigation strategies are put into place to prevent or respond to ransomware attacks. learn more about ransomware mitigation best practices and tools. The anatomy of the ransomware lifecycle ransomware has evolved into a sophisticated and pervasive threat, infiltrating organizations through various stages in its lifecycle. rney is crucial for developing efective defense strategies. this chapter delves into the anatomy of the ransomware lifecycle, exploring the key phases from. As ransomware attacks become more sophisticated, they pose ever greater risks, necessitating continuous evolution in defence mechanisms. this paper has highlighted the complex nature of ransomware, its evolution, and its operational mechanics, while also discussing effective mitigation strategies. Ransomware attacks continue to evolve, leveraging sophisticated techniques to infiltrate systems, encrypt data, and demand payment. understanding the ransomware kill chain—the stages an attacker follows—is critical for cybersecurity professionals to detect, prevent, and respond effectively.
Comments are closed.