Understanding And Implementing Soar In Cybersecurity

Soar In Cybersecurity Enterprise Strategy For Leaders Through the integration and automation of various security tools, processes, and workflows, soar platforms help teams respond to threats faster, reduce manual effort, and improve overall efficiency. Discover how soar (security orchestration, automation, and response) streamlines threat response. learn how it boosts efficiency and fortifies security.

Understanding Soar Cyber Defence Kit In this article, we will explore the foundational principles of soar, examine its core components, delve into its benefits and challenges, discuss real world use cases, and outline best practices for implementing a soar platform. Those organizations implementing soar solutions realize 50% faster threat detection and up to 80% improved operational efficiency. this article will break down the basics of soar, how it differs from siem and xdr, key benefits, uses, and how to implement it. This document is intended for cyber security practitioners. in greater technical details, it defines siem soar platforms, outlines the benefits and challenges, and provides best practice. Security orchestration, automation, and response (soar) is a set of technologies that enable organisations to collect security threat data and alerts from multiple sources.
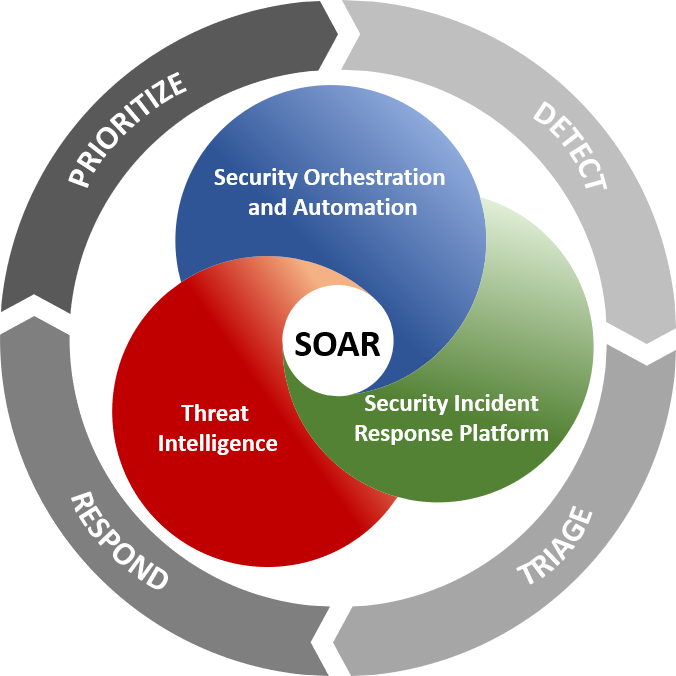
How Soar Platforms Can Streamline Incident Response And Improve This document is intended for cyber security practitioners. in greater technical details, it defines siem soar platforms, outlines the benefits and challenges, and provides best practice. Security orchestration, automation, and response (soar) is a set of technologies that enable organisations to collect security threat data and alerts from multiple sources. Discover what soar is, why it is important for security, its benefits and how to successfully implement it. learn more today!. Learn how to successfully implement soar in your iam and cybersecurity strategy. this guide covers planning, integration, automation, and maintenance. This publication provides high level guidance for cyber security practitioners on security information and event management (siem) and security orchestration, automation, and response (soar) platforms. Security orchestration and automated response (soar) represents a sophisticated approach to managing cybersecurity incidents. by integrating various tools and automating tasks, it aims to streamline and enhance the efficiency of security operations.

What Is Soar In Cybersecurity A7 Security Hunters Discover what soar is, why it is important for security, its benefits and how to successfully implement it. learn more today!. Learn how to successfully implement soar in your iam and cybersecurity strategy. this guide covers planning, integration, automation, and maintenance. This publication provides high level guidance for cyber security practitioners on security information and event management (siem) and security orchestration, automation, and response (soar) platforms. Security orchestration and automated response (soar) represents a sophisticated approach to managing cybersecurity incidents. by integrating various tools and automating tasks, it aims to streamline and enhance the efficiency of security operations.

Cyber Security Comnet This publication provides high level guidance for cyber security practitioners on security information and event management (siem) and security orchestration, automation, and response (soar) platforms. Security orchestration and automated response (soar) represents a sophisticated approach to managing cybersecurity incidents. by integrating various tools and automating tasks, it aims to streamline and enhance the efficiency of security operations.

Nsa Asd S Acsc And Other Agencies Publish Three Cybersecurity
Comments are closed.