Unauthorized Fdi Attacks Shielding Smart Grid No 1 Approach
Impact Of Integrity Attacks On Real Time Pricing In Smart Grids Smart Solution: to address this issue, the proposed solutions include using advanced techniques such as convolutional neural network (cnn) and cumulative sum algorithm (cusum) to detect anomalies and ensure the integrity of power flow measurements. Securing the smart grid is now paramount to ensuring its optimal performance. this document aims to provide a comprehensive analysis of the smart grid. we begin by examining its inherent weaknesses, followed by a classification of common attacks and their potential impacts.

Defending The Smart Grid From Threats And Attacks Cisco Blogs This paper underscores the critical need to enhance the security of dr mechanisms to mitigate the impact of sophisticated fdi attacks on the robustness of smart grids. Cyber–physical smart grid systems must be secured against increasing security threats and attacks. the most widely studied attacks in smart grids are false data injection attacks (fdia), denial of service, distributed denial of service (ddos), and spoofing attacks. The increasing integration of smart grids has introduced vulnerabilities in advanced metering infrastructure (ami), particularly through false data injection (fdi) attacks, which can compromise grid operations. Modern security technologies are almost perfect for detecting and preventing numerous attacks on the smart grid. they are unable to meet the challenging cyber security standards, nevertheless. we need many methods and techniques to effectively defend against cyber threats.

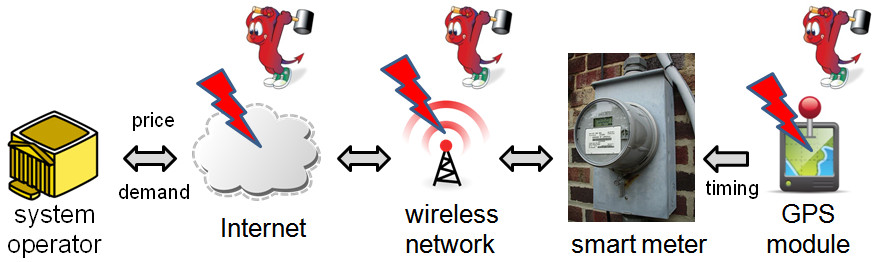
Smart Grid Security Key Attacks And Defense Techniques Infosys Bpm The increasing integration of smart grids has introduced vulnerabilities in advanced metering infrastructure (ami), particularly through false data injection (fdi) attacks, which can compromise grid operations. Modern security technologies are almost perfect for detecting and preventing numerous attacks on the smart grid. they are unable to meet the challenging cyber security standards, nevertheless. we need many methods and techniques to effectively defend against cyber threats. False data injection (fdi) attack in smart grid can cause catastrophic impact in energy management and distribution. here, a novel hybrid model combining the state of the art transformer and lstm is developed to detect the presence of fdi as well as the location of attack in smart grid. : a rogue interloper attack on smart grids occurs when an unauthorized device or entity infiltrates the network. the rogue device, through identi y spoofing or other forms of deception, presents itself as a legitimate component within the smart grid network. once accepted as part of the system, it can engage in various malicious activities. Fdi aims to attack especially a smart metre and pmu. the man in the middle attacks are notorious for intercepting data among sg devices, such as a smart metre, a breaker, switch, and an sg control centre. Di attacks becomes particularly evident when considering its reliance on accurate demand data. in emphasizing the importance of fortifying dr’s security against fdi, the ensemble and transfe adversarial attack (etaa) based on adversarial machine learning (aml) techniques is proposed. this method facilitates the inject.
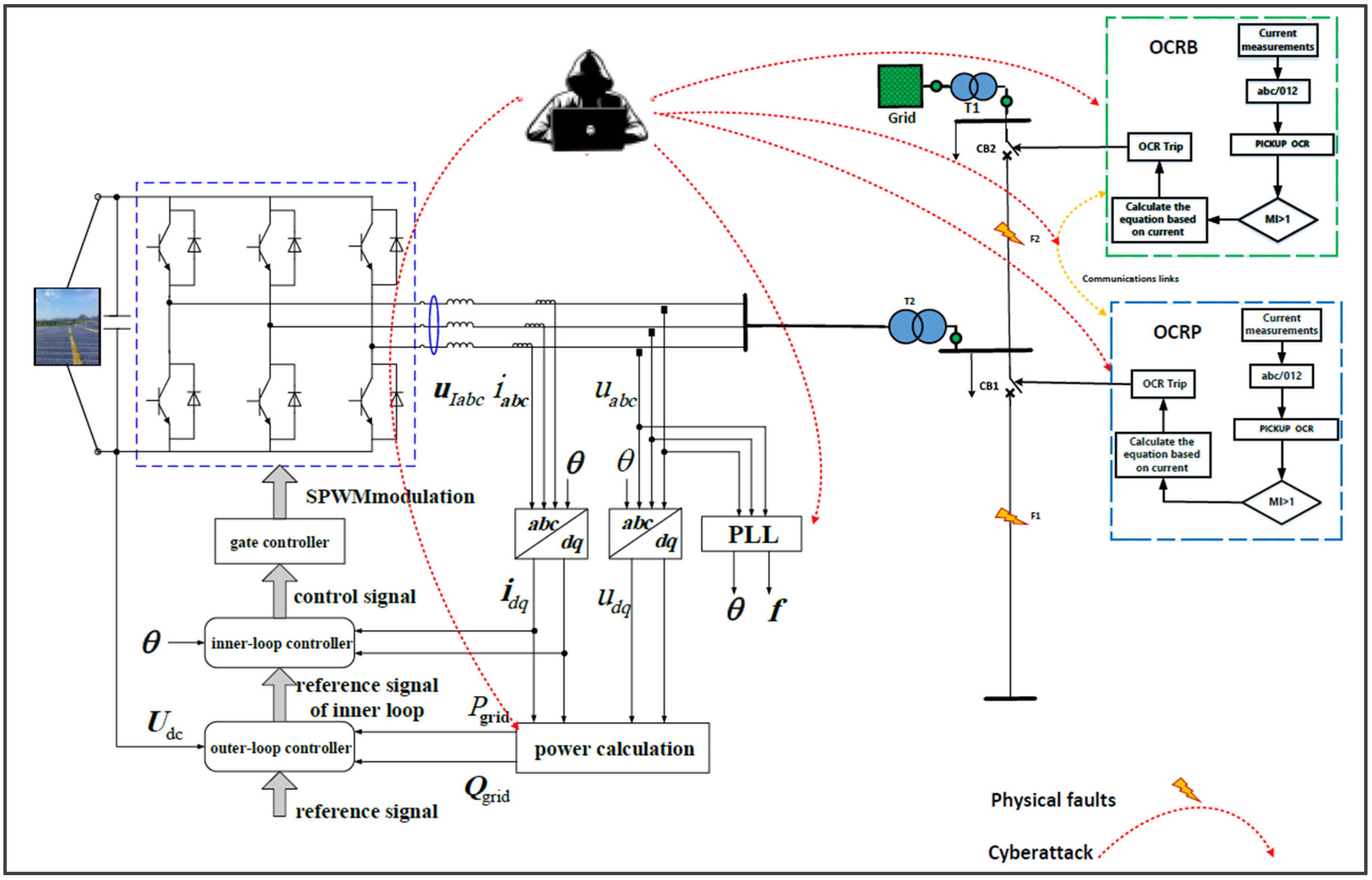
Smart Grid Resilience For Grid Connected Pv And Protection Systems False data injection (fdi) attack in smart grid can cause catastrophic impact in energy management and distribution. here, a novel hybrid model combining the state of the art transformer and lstm is developed to detect the presence of fdi as well as the location of attack in smart grid. : a rogue interloper attack on smart grids occurs when an unauthorized device or entity infiltrates the network. the rogue device, through identi y spoofing or other forms of deception, presents itself as a legitimate component within the smart grid network. once accepted as part of the system, it can engage in various malicious activities. Fdi aims to attack especially a smart metre and pmu. the man in the middle attacks are notorious for intercepting data among sg devices, such as a smart metre, a breaker, switch, and an sg control centre. Di attacks becomes particularly evident when considering its reliance on accurate demand data. in emphasizing the importance of fortifying dr’s security against fdi, the ensemble and transfe adversarial attack (etaa) based on adversarial machine learning (aml) techniques is proposed. this method facilitates the inject.
Comments are closed.