Two Fish Cipher Pptx

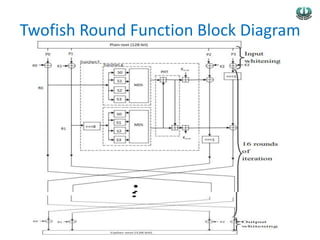
Two Fish Pdf Each round uses g functions consisting of s boxes and an mds matrix, along with a pht to diffuse the outputs which are then combined with key words. download as a pptx, pdf or view online for free. Twofish a 128 bit block chiper free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. twofish is a 128 bit block cipher that supports variable length keys up to 256 bits and operates as a 16 round feistel network.
Two Fish Cipher Pptx 16 round twofish (without whitening) should have no chosen plaintext attack requiring fewer than 280 chosen plaintexts and less than 2n time, where n is the key length. 12 round twofish (without whitening) should have no related key attack requiring fewer than 264 chosen plaintexts, and less than 2n 2 time, where n is the key length. 6 twofish. Two fish ciphers use symmetric keys where the same key is used for both encryption and decryption. two fish belongs to the family of feistel ciphers (feistel networks) and uses a block size of up to 128bites it operates on fixed key sizes of 128, 192 and 256 bits. Two fish choosing aes (table from twofish paper) aes winner: rijndael invented by joan daemen and vincent rijmen rijndael. a variant of square, the chief drawback to this cipher is the difficulty americans have pronouncing it. Twofish paper on the cd (and on our website) is a long paper describing twofish, our design rationale, and our analysis. it’s easy to read (and we think it’s interesting). additional cryptanalysis will be published as “twofish technical reports.” the first one is available outside.
Two Fish Cipher Pptx Two fish choosing aes (table from twofish paper) aes winner: rijndael invented by joan daemen and vincent rijmen rijndael. a variant of square, the chief drawback to this cipher is the difficulty americans have pronouncing it. Twofish paper on the cd (and on our website) is a long paper describing twofish, our design rationale, and our analysis. it’s easy to read (and we think it’s interesting). additional cryptanalysis will be published as “twofish technical reports.” the first one is available outside. Twofish is a symmetric key block cipher designed by bruce schneier and his team at counterpane systems. it is a block cipher variant, always operating compounding blocks of data, usually 128 bits. In cryptography, twofish is a symmetric key block cipher with a block size of 128 bits and key sizes up to 256 bits. it was one of the five finalists of the advanced encryption standard contest, but it was not selected for standardization. Twofish has efficient performance across many platforms and competitive speeds compared to other aes finalists. download as a pptx, pdf or view online for free. These are the most important findings of their cryptanalysis of twofish: a successful chosen key attack against twofish requires choosing 160 bits of a pair of keys, and needs 234 work, 232 chosen plaintext queries, and 212 adaptive chosen plaintext queries so that 10 rounds twofish can be broken.
Two Fish Cipher Pptx Twofish is a symmetric key block cipher designed by bruce schneier and his team at counterpane systems. it is a block cipher variant, always operating compounding blocks of data, usually 128 bits. In cryptography, twofish is a symmetric key block cipher with a block size of 128 bits and key sizes up to 256 bits. it was one of the five finalists of the advanced encryption standard contest, but it was not selected for standardization. Twofish has efficient performance across many platforms and competitive speeds compared to other aes finalists. download as a pptx, pdf or view online for free. These are the most important findings of their cryptanalysis of twofish: a successful chosen key attack against twofish requires choosing 160 bits of a pair of keys, and needs 234 work, 232 chosen plaintext queries, and 212 adaptive chosen plaintext queries so that 10 rounds twofish can be broken.
Two Fish Cipher Pptx Twofish has efficient performance across many platforms and competitive speeds compared to other aes finalists. download as a pptx, pdf or view online for free. These are the most important findings of their cryptanalysis of twofish: a successful chosen key attack against twofish requires choosing 160 bits of a pair of keys, and needs 234 work, 232 chosen plaintext queries, and 212 adaptive chosen plaintext queries so that 10 rounds twofish can be broken.
Comments are closed.