Two Factor Authentication For Learning Management Systems Avesei

Two Factor Authentication For Learning Management Systems Avesei In this article we will seek to understand two factor authentication, the importance of two factor authentication for lms, its implementation, and the future trends in elearning security. In this article we will seek to understand two factor authentication, the importance of two factor authentication for lms, its implementation, and the future trends in elearning security.

Guide To Learning Management Systems Everything You Need Avesei Through the inception of this innovative authentication solution, a thorough evaluation and comparative analysis of authentication methodologies prevalent in diverse e learning systems was undertaken. This novel authentication solution is intro duced by thoroughly analyzing and comparing various authentication methods employed in prominent e learning systems available in the market. With the innovative authentication scheme, the users have gained confidence, are satisfied with the new solution, and have not reported security breaches. the result is increased security, data protection, and better account management. Ensuring secure access involves using robust authentication methods such as strong passwords and multi factor authentication to control who can access online learning platforms and materials.
Development Of A Two Factor Authentication Login System Using One Time With the innovative authentication scheme, the users have gained confidence, are satisfied with the new solution, and have not reported security breaches. the result is increased security, data protection, and better account management. Ensuring secure access involves using robust authentication methods such as strong passwords and multi factor authentication to control who can access online learning platforms and materials. A systematic literature review of a multi factor authentication framework was conducted through five primary databases: scopus, ieee, science direct, springer link, and web of science. the review examined the proposed solution and the underlying methods in a multi factor authentication framework. The proposed solution introduces a new authentication factor using digital certificates stored on physical devices or the cloud to address the evolving authentication and security challenges effectively. Therefore, this study evaluates the effectiveness of multi factor authentication (mfa) in protecting student privacy in an educational environment. this study uses a systematic literature. Metode two factor authentication (2fa) verifikasi dengan kolaborasi aplikasi telegram diterapkan agar dapat membantu meminimalisir kelemahan pada keamanan sistem informasi akademik.
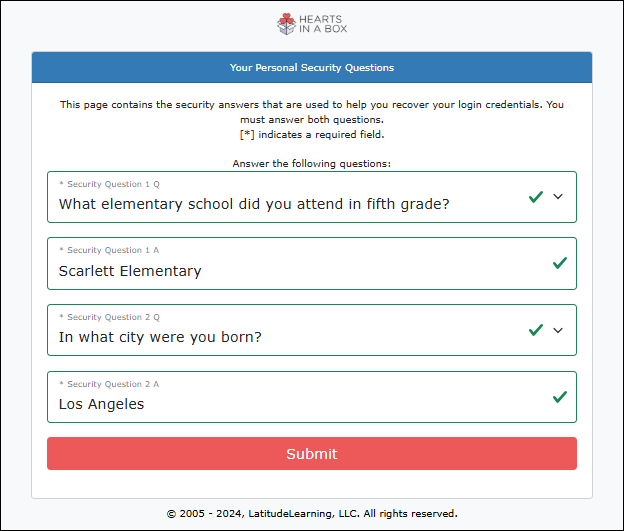
Log In Using Two Factor Authentication Latitudelearning A systematic literature review of a multi factor authentication framework was conducted through five primary databases: scopus, ieee, science direct, springer link, and web of science. the review examined the proposed solution and the underlying methods in a multi factor authentication framework. The proposed solution introduces a new authentication factor using digital certificates stored on physical devices or the cloud to address the evolving authentication and security challenges effectively. Therefore, this study evaluates the effectiveness of multi factor authentication (mfa) in protecting student privacy in an educational environment. this study uses a systematic literature. Metode two factor authentication (2fa) verifikasi dengan kolaborasi aplikasi telegram diterapkan agar dapat membantu meminimalisir kelemahan pada keamanan sistem informasi akademik.
Two Factor Authentication Eagle Eye Networks Therefore, this study evaluates the effectiveness of multi factor authentication (mfa) in protecting student privacy in an educational environment. this study uses a systematic literature. Metode two factor authentication (2fa) verifikasi dengan kolaborasi aplikasi telegram diterapkan agar dapat membantu meminimalisir kelemahan pada keamanan sistem informasi akademik.

How To Use Tutor Lms Two Factor Authentication Full Guide
Comments are closed.