Tutorial Mac Address Spoofing
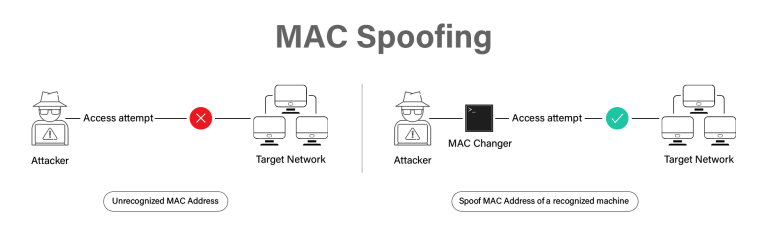
Mac Spoofing Attacks Explained A Technical Overview While mac address filtering is generally applied at the network layer and not typically used for controlling access to web servers, but for demonstration we will simulate a scenario where a script checks the mac address before allowing access to content. In this lab, you will learn the end to end process of bypassing mac address filtering. you will first identify a target network, find the mac address of an already authorized client, and then change your own wireless adapter's mac address to impersonate that client.
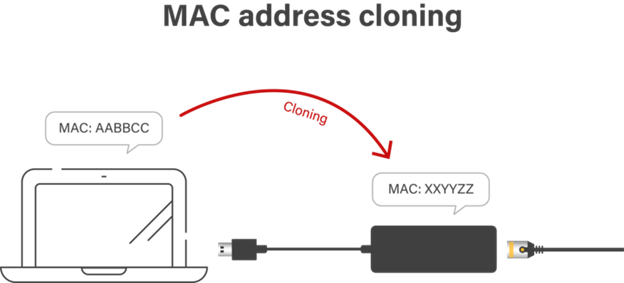
Mac Spoofing Attacks Explained A Technical Overview A mac address is intended to be permanent for a device, but you can spoof (change) it to a random address or to a specific device’s mac address to impersonate that device. This comprehensive guide explores the practical implementation of mac address modification across various platforms, providing verified commands for penetration testers, network administrators, and cybersecurity enthusiasts. learning objectives: master mac address manipulation techniques across windows, linux, and macos systems. This blog post will provide you with a detailed understanding of mac address spoofing in linux, including fundamental concepts, usage methods, common practices, and best practices. Learn what mac spoofing is, how attackers use it, and how to prevent it. this 2025 guide covers detection tools, real world risks, and expert prevention techniques for businesses and individuals.
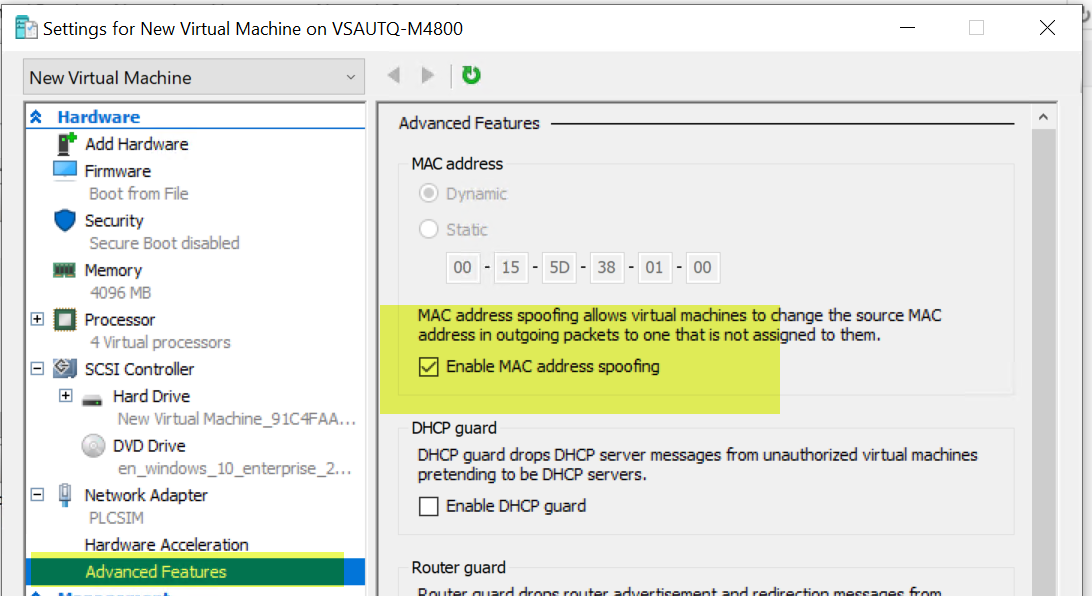
Enable Mac Address Spoofing Microsoft Q A This blog post will provide you with a detailed understanding of mac address spoofing in linux, including fundamental concepts, usage methods, common practices, and best practices. Learn what mac spoofing is, how attackers use it, and how to prevent it. this 2025 guide covers detection tools, real world risks, and expert prevention techniques for businesses and individuals. Learn what mac spoofing is, why it protects your privacy on public wi fi, and how to change your mac address. discover windscribe's built in mac spoofing feature. We will not just tell you what mac spoofing is; we are going to show you exactly how attackers bypass your firewalls using it, and more importantly, how you can catch them. from deep packet analysis in wireshark to writing your own detection algorithms in python, this is the only guide you will ever need. Macchanger is a powerful tool for spoofing or changing the mac (media access control) address of a network interface card. by temporarily or permanently altering a mac address, cybersecurity professionals can enhance privacy, bypass network filters, or simulate devices for testing purposes. In this tutorial, we'll show you how to use macchanger on linux to easily spoof your mac address. whether yo more.
Mac Spoofing Attacks Explained A Technical Overview Learn what mac spoofing is, why it protects your privacy on public wi fi, and how to change your mac address. discover windscribe's built in mac spoofing feature. We will not just tell you what mac spoofing is; we are going to show you exactly how attackers bypass your firewalls using it, and more importantly, how you can catch them. from deep packet analysis in wireshark to writing your own detection algorithms in python, this is the only guide you will ever need. Macchanger is a powerful tool for spoofing or changing the mac (media access control) address of a network interface card. by temporarily or permanently altering a mac address, cybersecurity professionals can enhance privacy, bypass network filters, or simulate devices for testing purposes. In this tutorial, we'll show you how to use macchanger on linux to easily spoof your mac address. whether yo more.
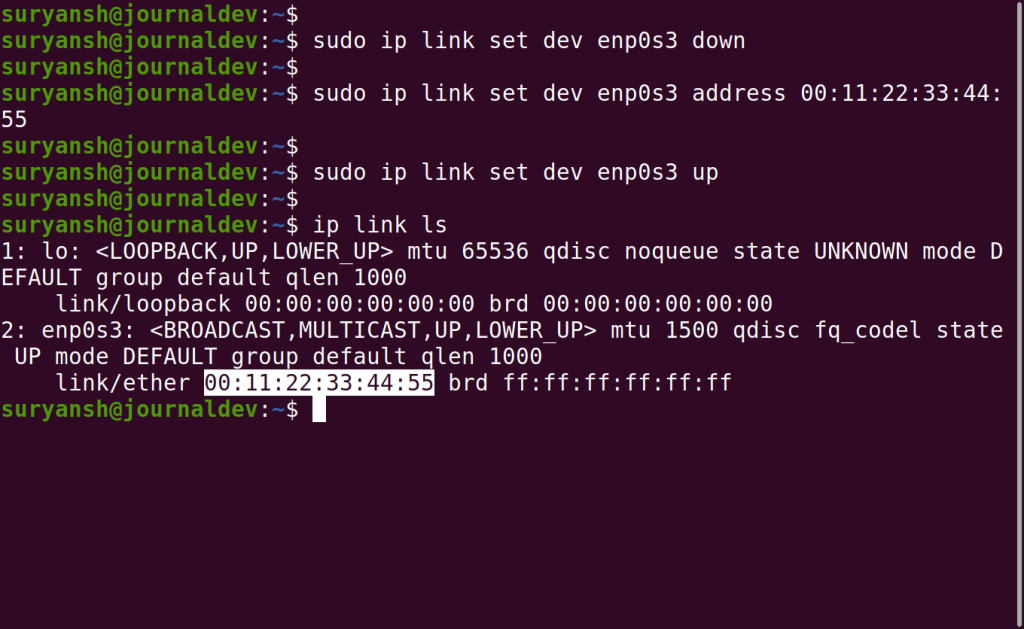
How To Change Or Spoof Mac Address In Ubuntu Linuxfordevices Macchanger is a powerful tool for spoofing or changing the mac (media access control) address of a network interface card. by temporarily or permanently altering a mac address, cybersecurity professionals can enhance privacy, bypass network filters, or simulate devices for testing purposes. In this tutorial, we'll show you how to use macchanger on linux to easily spoof your mac address. whether yo more.
Comments are closed.