Tutorial Arbitrary Read Write

Memory Read And Write Operations Explained Pdf In this example, we will perform one of the basic kernel exploitation techniques which is essentially an arbitrary write (write what where). This project helps researchers, redteamers, and defenders better understand exploitation techniques for linux by providing an intentionally vulnerable service with ready to use exploit primitives like stack out of bounds, arbitrary write, and arbitrary read vulnerabilities.

Solved Beginner Still Needs Help With Simplereadwrite Ni Community An arbitrary write primitive, or colloquially named as a write what where primitive, enables an attacker to arbitrarily write a value to any address we supply. it’s quite a powerful primitive and grants the attacker a lot of creativity on how they exploit the application system. You can basically write the token stealing shellcode from the previous blog using the arbitrary read write primitive. there is a slight distinction in that, in the shellcode we have the pointer to our own process (from the gs register), and search for the pid 4 (system) process. By the end of this post, we will have learned how to turn this second, more powerful uaf either into kernel code execution via rop or into an arbitrary read write primitive via pipes. This is a writeup on a kernel pwn challenge from imaginary ctf 2023, and aims to introduce kernel pwn in a beginner friendly manner. the beginner in ‘beginner friendly’ refers to someone who has never touched kernel exploitation before.
Arbitrary Read And Write In Webkit Exploit By the end of this post, we will have learned how to turn this second, more powerful uaf either into kernel code execution via rop or into an arbitrary read write primitive via pipes. This is a writeup on a kernel pwn challenge from imaginary ctf 2023, and aims to introduce kernel pwn in a beginner friendly manner. the beginner in ‘beginner friendly’ refers to someone who has never touched kernel exploitation before. In this blogpost, we will start by giving the reader a bit of context on heap exploitation and glibc internals. we will then tackle the challenge itself and how we solved it. if you want to try this challenge yourself, here is a link to the binary, dockerfile, and our solution: setjmp.tar.gz. In this post we will be revisiting the write what where vulnerability. by implementing a powerful ring0 read write primitive we can create an exploit that works on windows 7, 8, 8.1 and 10 (pre v1607) and targets both 32 and 64 bit architectures!. After a reliable linear read write primitive was established we needed arbitrary read. to establish an arbitrary read we can modify the token >bnoisolationhandlesentry and point it to a controlled userspace address, see once again k0shls blog. In the last tutorial, we used code and stack pointers freely leaked by the binary in our control hijacking attacks. in this tutorial, we'll exploit the same program again, but this time without any a priori information leaks, and also in x86 64 (64 bit).
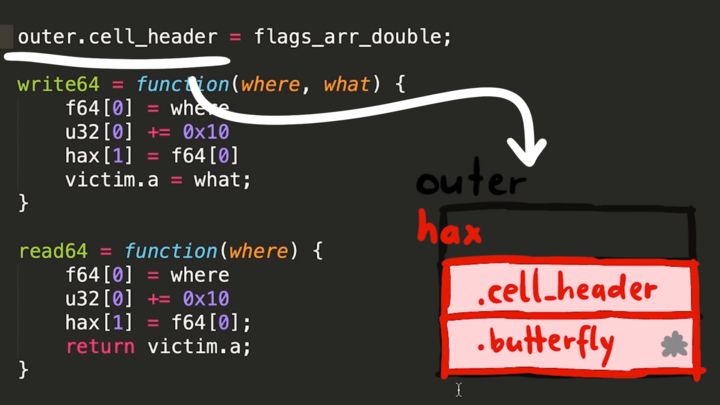
Arbitrary Read And Write In Webkit Exploit In this blogpost, we will start by giving the reader a bit of context on heap exploitation and glibc internals. we will then tackle the challenge itself and how we solved it. if you want to try this challenge yourself, here is a link to the binary, dockerfile, and our solution: setjmp.tar.gz. In this post we will be revisiting the write what where vulnerability. by implementing a powerful ring0 read write primitive we can create an exploit that works on windows 7, 8, 8.1 and 10 (pre v1607) and targets both 32 and 64 bit architectures!. After a reliable linear read write primitive was established we needed arbitrary read. to establish an arbitrary read we can modify the token >bnoisolationhandlesentry and point it to a controlled userspace address, see once again k0shls blog. In the last tutorial, we used code and stack pointers freely leaked by the binary in our control hijacking attacks. in this tutorial, we'll exploit the same program again, but this time without any a priori information leaks, and also in x86 64 (64 bit).
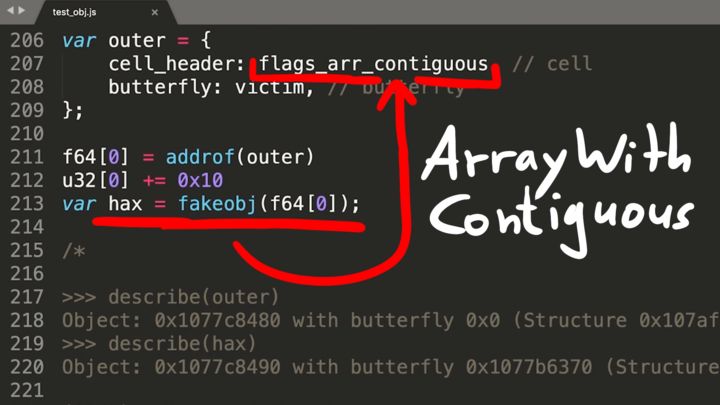
Arbitrary Read And Write In Webkit Exploit After a reliable linear read write primitive was established we needed arbitrary read. to establish an arbitrary read we can modify the token >bnoisolationhandlesentry and point it to a controlled userspace address, see once again k0shls blog. In the last tutorial, we used code and stack pointers freely leaked by the binary in our control hijacking attacks. in this tutorial, we'll exploit the same program again, but this time without any a priori information leaks, and also in x86 64 (64 bit).
Comments are closed.