Tutorial 2 Vulnerability Scanning Tutorial 3 Vulnerability Scanning

The Ultimate Guide To Vulnerability Scanning And Resolution Wiz Learn how to use openvas, a powerful vulnerability scanning tool, to identify and prioritize security risks in your network. Let’s look at how to set up this tool as well as how to run a basic cve scan. the nmap script engine searches http responses to identify cpes for the given script.

A Step By Step Guide To Vulnerability Scanning Nmap is a powerful tool for vulnerability scanning. learn how to use nmap to discover and assess network vulnerabilities. Vulnerability analysis with openvas installing and configuring openvas searchsploit searching for exploits introduction to vulnerability scanning how to install & configure nessus host discovery & vulnerability scanning with nessus log4j cve 2021 44228 (log4shell) exploitation & mitigation. Build an effective vulnerability scanning capability with this openvas tutorial. with expert tips to crush network security weakness. Aict006 4 2 dsf digital security and forensics 2022 this part of the tutorial is designed to test your understanding on threats, risk and vulnerabilities. you will learn how to differentiate the terms and how they are interrelated by attempting the questions following key questions.
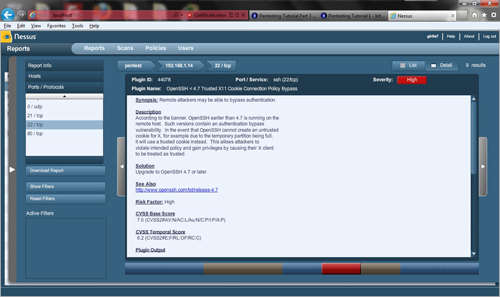
Pentesting Tutorial Part 3 Vulnerability Scanning And Authentication Build an effective vulnerability scanning capability with this openvas tutorial. with expert tips to crush network security weakness. Aict006 4 2 dsf digital security and forensics 2022 this part of the tutorial is designed to test your understanding on threats, risk and vulnerabilities. you will learn how to differentiate the terms and how they are interrelated by attempting the questions following key questions. Learn how to run a web vulnerability scan and generate a report using burp scanner in burp suite professional. This guide outlines the process of performing a basic vulnerability scan on a personal pc using nessus essentials, a free tool, to identify and address security weaknesses. Every day we discover new vulnerabilities that impact our computer systems, which become more complex. the process of interpreting and addressing threats found in a vulnerability scan can often appear complex. Let’s walk through the steps to prepare your virtual machine for vulnerability scanning in a controlled environment. this guide prioritizes security and isolation while offering flexibility for.
Comments are closed.