Tryhackme Blaster Walkthrough

Tryhackme Blaster Task 2 Walkthrough Tryhackme — blaster walkthrough. step by step walkthrough for tryhackme… | by atharva | medium. task 1: mission start! throughout this room, we’ll be looking at alternative modes of. From the username and password we have successfully logged in and we can see the user.txt file is present on the desktop you can view the user.txt file and submit the user flag. after checking the browser’s history we got some useful information.

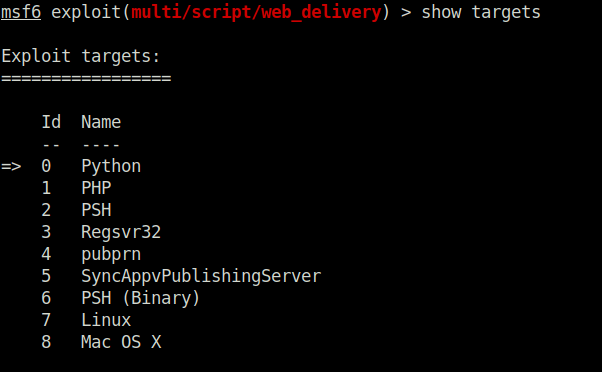
Tryhackme Blaster Aldeid 概要 tryhackme「blaster」のwalkthroughです。 task2 q1.how many ports are open on our target system? ポートスキャンを実行します。 $ nmap pn t4 svc a. We're a gamified, hands on cyber security training platform that you can access through your browser. a blast from the past!. Follow me on twitter: twitter darkstar7471join my community discord server: discord.gg ns9ushnthumbnail design by varg: twitter.c. After setting your payload, set your lhost and lport accordingly such that you know which port the msf web server is going to run on and that it'll be running on the tryhackme network.

Blaster Walkthrough Hey Guys Today We Re Gonna Hack Into By Follow me on twitter: twitter darkstar7471join my community discord server: discord.gg ns9ushnthumbnail design by varg: twitter.c. After setting your payload, set your lhost and lport accordingly such that you know which port the msf web server is going to run on and that it'll be running on the tryhackme network. Blaster — tryhackme walkthrough task 1: mission start! throughout this room, we’ll be looking at alternative modes of exploitation without the use of metasploit or really exploitation tools. This is my 3rd writeup followed up by ice. the purpose of this writeup is to document the steps i took to complete the blaster a vulnerable windows based room. which is created by darkstar in. Go to retro and start looking for any useful information. you will find a user called wade. search further on the website to find the password. if you click on wade you will go to his profile. from there click on comments rss on the right pane of the page, and you will be prompted with a window to download a file. Blaster writup ~ tryhackme task 1 : mission start! start this room by hitting the “deploy” button on the right!once you have deployed machine you have assigned a vulnerable machine ip.it is a ….
Tryhackme Blaster Blaster — tryhackme walkthrough task 1: mission start! throughout this room, we’ll be looking at alternative modes of exploitation without the use of metasploit or really exploitation tools. This is my 3rd writeup followed up by ice. the purpose of this writeup is to document the steps i took to complete the blaster a vulnerable windows based room. which is created by darkstar in. Go to retro and start looking for any useful information. you will find a user called wade. search further on the website to find the password. if you click on wade you will go to his profile. from there click on comments rss on the right pane of the page, and you will be prompted with a window to download a file. Blaster writup ~ tryhackme task 1 : mission start! start this room by hitting the “deploy” button on the right!once you have deployed machine you have assigned a vulnerable machine ip.it is a ….
Tryhackme Blaster Go to retro and start looking for any useful information. you will find a user called wade. search further on the website to find the password. if you click on wade you will go to his profile. from there click on comments rss on the right pane of the page, and you will be prompted with a window to download a file. Blaster writup ~ tryhackme task 1 : mission start! start this room by hitting the “deploy” button on the right!once you have deployed machine you have assigned a vulnerable machine ip.it is a ….
Comments are closed.