Transmitted Data Vs Intercepted Data Internal Attack Download

Transmitted Data Vs Intercepted Data Internal Attack Download Download scientific diagram | transmitted data vs. intercepted data (internal attack). from publication: network coding based d2d transmission for public safety networks over lte. Data communicated over the network can be intercepted by anyone who controls a node on that network. in attacks such as these, therefore, adversaries take control of data as it’s being transmitted over the network.
Transmitted Data Vs Eavesdropped Data Internal Attack Download Data in transit is actively moving across networks—such as emails, file transfers, or api communications—making it vulnerable to interception. in contrast, data at rest remains stored on devices, databases, or cloud environments, where unauthorized access is the primary concern. A list of publicly available pcap files network traces that can be downloaded for free. In this tutorial, we’ll learn about four categories of cybersecurity attacks: interruption, interception, modification, and fabrication. we’ll study their characteristics and differences. Understanding these cross language relationships becomes essential for identifying where transmitted data manipulation could occur without network interception.
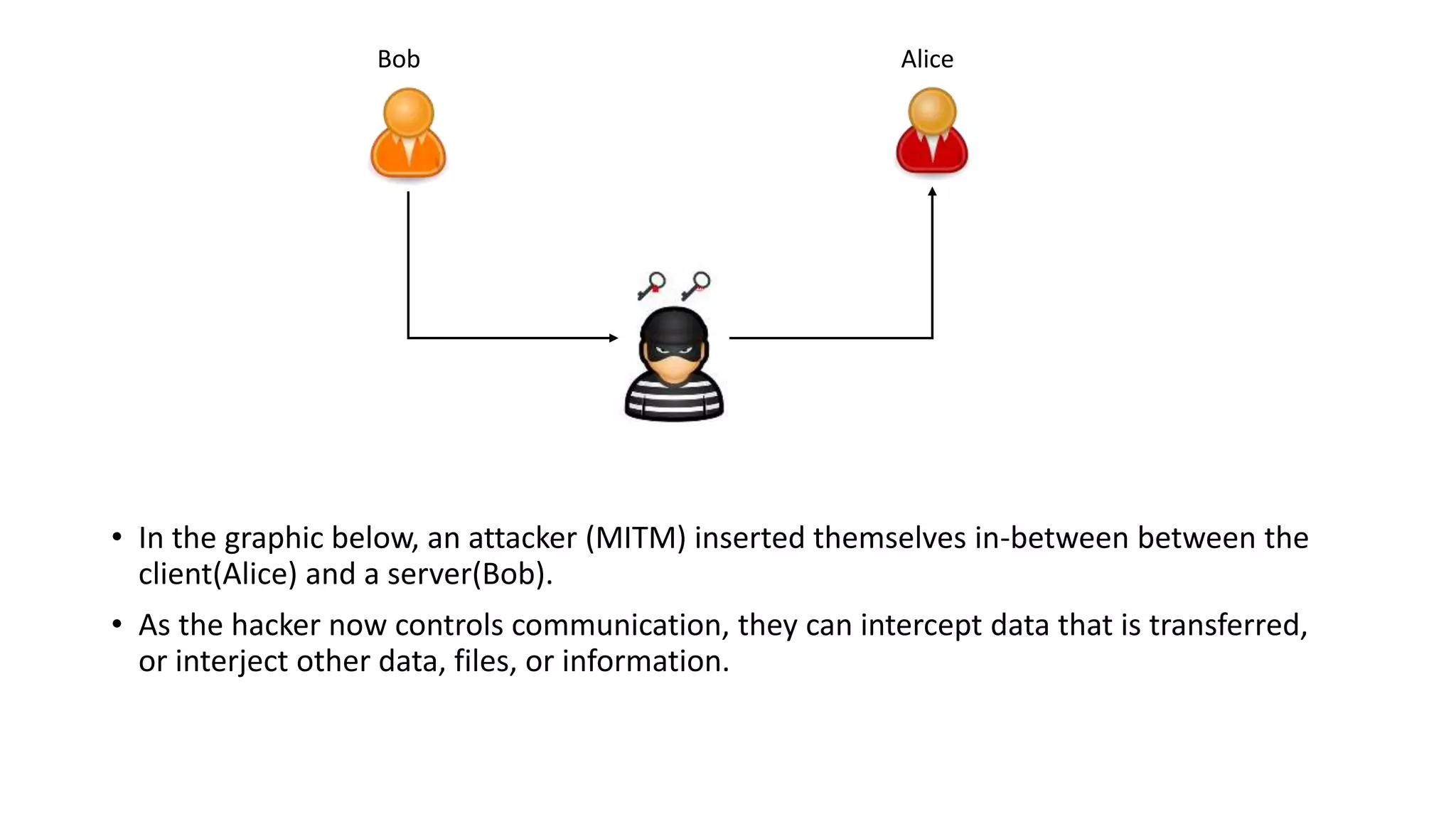
Man In The Middle Attack Mitm Pptx In this tutorial, we’ll learn about four categories of cybersecurity attacks: interruption, interception, modification, and fabrication. we’ll study their characteristics and differences. Understanding these cross language relationships becomes essential for identifying where transmitted data manipulation could occur without network interception. Monitor for anomalies in transmitted data streams, including mismatched file integrity checks, api interception, or man in the middle modifications. detect unexpected use of apis that handle network i o where transmitted data integrity could be manipulated. Distinct from passive interception, where the perpetrator simply listens but does not interfere with the communication, active interception takes an extra step involving not only unauthorized data access but also potential manipulation. These networks can be vulnerable to various cyber threats, including eavesdropping and data interception, so it’s advisable to avoid transmitting sensitive information or use a virtual private network (vpn) for added security when connecting to such networks. This cybercrime compromised the confidentiality of data (by gaining unauthorized access to the website and system and stealing information) and the integrity of data (by defacing websites).

Chapter 1 Introduction Ppt Download Monitor for anomalies in transmitted data streams, including mismatched file integrity checks, api interception, or man in the middle modifications. detect unexpected use of apis that handle network i o where transmitted data integrity could be manipulated. Distinct from passive interception, where the perpetrator simply listens but does not interfere with the communication, active interception takes an extra step involving not only unauthorized data access but also potential manipulation. These networks can be vulnerable to various cyber threats, including eavesdropping and data interception, so it’s advisable to avoid transmitting sensitive information or use a virtual private network (vpn) for added security when connecting to such networks. This cybercrime compromised the confidentiality of data (by gaining unauthorized access to the website and system and stealing information) and the integrity of data (by defacing websites).
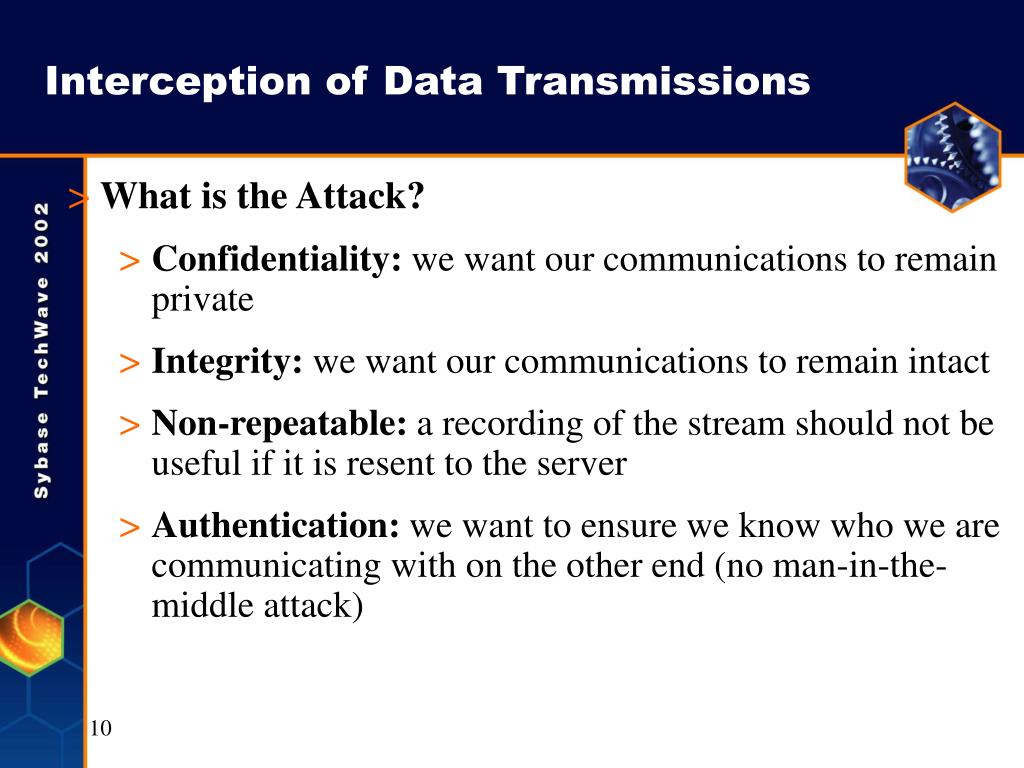
Ppt M421 Mobile Data Security Powerpoint Presentation Free Download These networks can be vulnerable to various cyber threats, including eavesdropping and data interception, so it’s advisable to avoid transmitting sensitive information or use a virtual private network (vpn) for added security when connecting to such networks. This cybercrime compromised the confidentiality of data (by gaining unauthorized access to the website and system and stealing information) and the integrity of data (by defacing websites).
Ppt Cybersecurity Powerpoint Presentation Free Download Id 5138894
Comments are closed.