Traditional Network Security Architecture The Improved 5g Network

Traditional Network Security Architecture The Improved 5g Network To this end, an improved adaptive weighted fusion algorithm is proposed to achieve accurate terminal collection and data fusion upload based on the edge side of the power iot edge computing. This document provides an overview of 5g network security, describing various components of the 5g core network architecture and what kind of security services are offered by these 5g components.

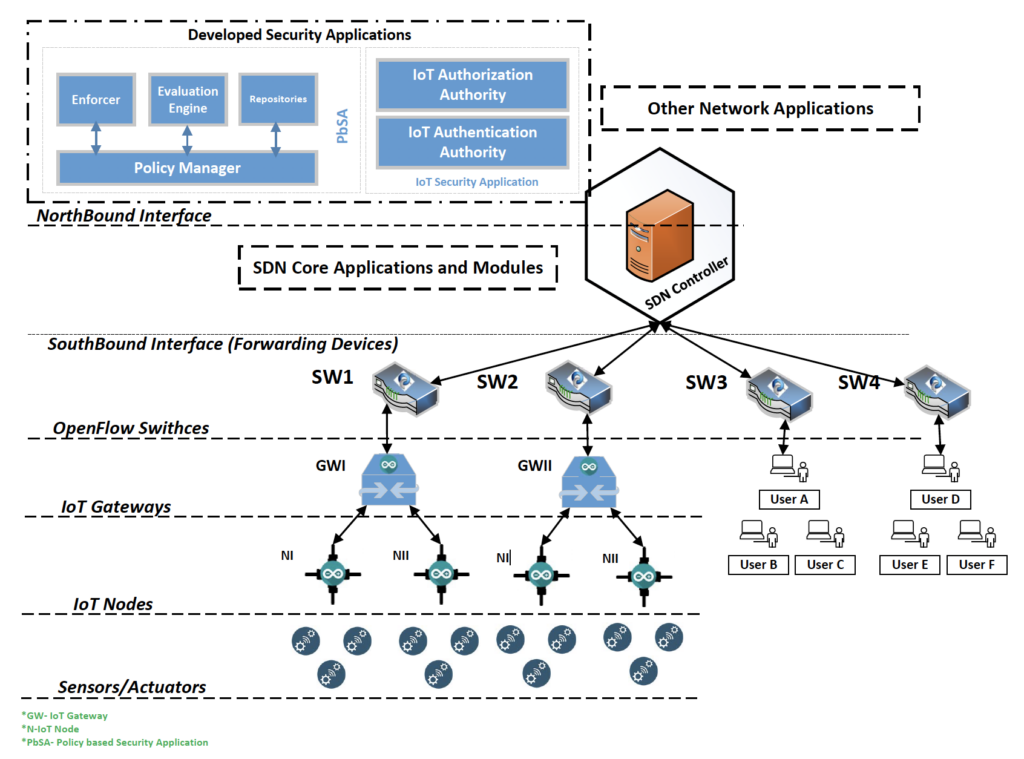
Traditional Network Security Architecture The Improved 5g Network The presented security architecture builds upon concepts from the 3g and 4g security architectures but extends and enhances them to cover the new 5g environment. The network infrastructure supporting nccoe’s 5g system uses a spine leaf architecture. this architecture is designed so that every leaf is connected to every spine to ensure that all leaf switches are no more than one hop away from one another. The components of a 5g security architecture—from authentication and key hierarchy to nfv sdn security, network slicing protection, and intelligent orchestration—ensure that 5g is not only speedy but also secure, resilient, and trustworthy. The framework leverages existing standards and technologies, such as 3gpp specifications and gsma guidelines, to ensure robust security measures tailored to evolving telecommunication needs.

Traditional Network Security Architecture The Improved 5g Network The components of a 5g security architecture—from authentication and key hierarchy to nfv sdn security, network slicing protection, and intelligent orchestration—ensure that 5g is not only speedy but also secure, resilient, and trustworthy. The framework leverages existing standards and technologies, such as 3gpp specifications and gsma guidelines, to ensure robust security measures tailored to evolving telecommunication needs. Learn about 5g security architecture, features, benefits and challenges. also, find out the differences between 5g and 4g security controls. This research investigates the laws and technologies related to 5g cybersecurity, focusing on how 5g networks are constructed, including software based networking and virtual network. 5g is transforming industries with ultra low latency, massive connectivity, and cloud native design. this guide explains how 5g works, its architecture, use cases, protocols, and the real security challenges operators face today. With useful diagrams and clear explanations, it explains the fundamentals of modern 5g networks and then goes deeper into the security architecture of these networks.

Cyber Security Network Architecture Stable Diffusion Online Learn about 5g security architecture, features, benefits and challenges. also, find out the differences between 5g and 4g security controls. This research investigates the laws and technologies related to 5g cybersecurity, focusing on how 5g networks are constructed, including software based networking and virtual network. 5g is transforming industries with ultra low latency, massive connectivity, and cloud native design. this guide explains how 5g works, its architecture, use cases, protocols, and the real security challenges operators face today. With useful diagrams and clear explanations, it explains the fundamentals of modern 5g networks and then goes deeper into the security architecture of these networks.
Network Security Architecture Diagram Sase Network Security That 5g is transforming industries with ultra low latency, massive connectivity, and cloud native design. this guide explains how 5g works, its architecture, use cases, protocols, and the real security challenges operators face today. With useful diagrams and clear explanations, it explains the fundamentals of modern 5g networks and then goes deeper into the security architecture of these networks.
Comments are closed.