Track 3 2 Malware Detection Using Ml

Malware Detection Using Machine Learning Pdf Malware Spyware In his paper “malware detection using machine learning” dragos gavrilut aimed for developing a detection system based on several modified perceptron algorithms. for different algorithms, he achieved the accuracy of 69.90% 96.18%. To fill this gap and motivate further research, we present an extensive review of malware detection using ml techniques with respect to pcs, mobile devices, iot, and cloud platforms. this paper begins with an overview of malware, including its definition, prominent types, analysis, and features.
Malware Detection Using Supervised Ml Projects Code2 Malware Detection This study uses a binary tabular classification dataset to evaluate the impact of feature selection, feature scaling, and machine learning (ml) models on malware detection. This chapter describes the implementation of the malware detection system, a web based application for analyzing executable files for malware using machine learning and static analysis. To fill this gap and motivate further research, we present an extensive review of malware detection using ml techniques with respect to pcs, mobile devices, iot, and cloud platforms. This paper focuses on developing a web application which can distinguish a malicious or legitimate binary executable file and a url using machine learning algorithms. … more.
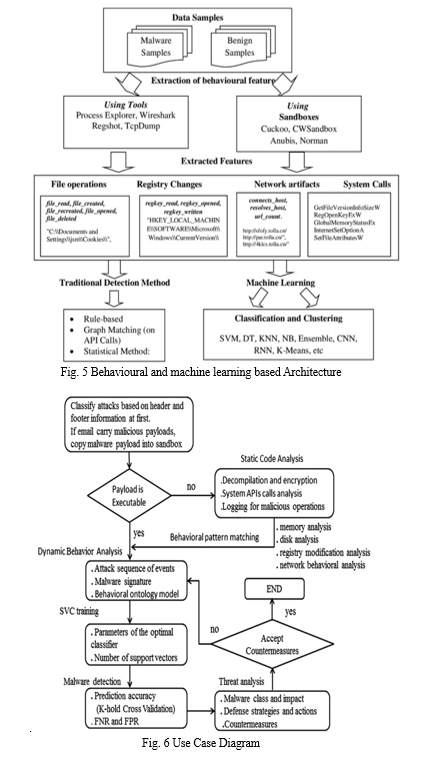
Github Kranthiksk Malware Detection Using Ml Algorithms To fill this gap and motivate further research, we present an extensive review of malware detection using ml techniques with respect to pcs, mobile devices, iot, and cloud platforms. This paper focuses on developing a web application which can distinguish a malicious or legitimate binary executable file and a url using machine learning algorithms. … more. By employing deep learning techniques such as cnn (convolutional neural network) and rnn (recurrent neural network), this study aims to classify and identify malware extracted from a dataset containing api call sequences. To address these challenges, we evaluate multiple retraining strategies that enable the timely detection of emerging malware families while tracking mutation patterns. Malware identification is essential for safeguarding digital systems from cyber attacks, and machine learning techniques are proving to be efficient in this fie. This paper examines the application of machine learning (ml) techniques—specifically supervised learning algorithms such as support vector machines (svm), random forest (rf), and neural networks—to diagnose and mitigate malware threats, particularly on windows based environments.
Github Marcinele Ml Malware Detection Malware Detection Using By employing deep learning techniques such as cnn (convolutional neural network) and rnn (recurrent neural network), this study aims to classify and identify malware extracted from a dataset containing api call sequences. To address these challenges, we evaluate multiple retraining strategies that enable the timely detection of emerging malware families while tracking mutation patterns. Malware identification is essential for safeguarding digital systems from cyber attacks, and machine learning techniques are proving to be efficient in this fie. This paper examines the application of machine learning (ml) techniques—specifically supervised learning algorithms such as support vector machines (svm), random forest (rf), and neural networks—to diagnose and mitigate malware threats, particularly on windows based environments.
Malware Detection Using Machine Learning Malware identification is essential for safeguarding digital systems from cyber attacks, and machine learning techniques are proving to be efficient in this fie. This paper examines the application of machine learning (ml) techniques—specifically supervised learning algorithms such as support vector machines (svm), random forest (rf), and neural networks—to diagnose and mitigate malware threats, particularly on windows based environments.
Malware Detection Using Machine Learning
Comments are closed.