Tornado Cash Dao Hack Explained Create2 Selfdestruct Sanctions

Tornado Cash Sanctions Explained Decoding Crypto Omny Fm Our team has performed a little analysis of the recent tornado cash governance hack. in this article, we aim to walk you through the entire incident, explaining our perspective on what happened, its implications and potential solutions. Tornadocash dao votes to approve the proposal contract, and then tornadocashdao contract calls approve for proposal. attacker calls emergencystop and kill for proposal and deployer, self destructing both.

Tornado Cash Dao Proposal Seeks Legal Fight Against Us Sanctions Tokenist Tl;dr — the attacker mainly used create, create2, and selfdestruct to exploit the governance. they proposed a contract identical to the previously passed proposal, but this proposal has a selfdestruct function that went unnoticed. “today, treasury is sanctioning tornado cash, a virtual currency mixer that launders the proceeds of cybercrimes, including those committed against victims in the united states,” said under secretary of the treasury for terrorism and financial intelligence brian e. nelson. Going over the latest #tornadocash #dao hack and how us sanctions on torn, the notorious crypto bundler, are being fought by lawyers.stay tuned i will uploa. Tl;dr — the attacker mainly used create, create2, and selfdestruct to exploit the governance. they proposed a contract identical to the previously passed proposal, but this proposal has a selfdestruct function that went unnoticed.

Tornado Cash Sanctions Key To Drop In Crypto Hacks Last Quarter Trm Labs Going over the latest #tornadocash #dao hack and how us sanctions on torn, the notorious crypto bundler, are being fought by lawyers.stay tuned i will uploa. Tl;dr — the attacker mainly used create, create2, and selfdestruct to exploit the governance. they proposed a contract identical to the previously passed proposal, but this proposal has a selfdestruct function that went unnoticed. On may 13th, tornado cash governance was hacked. let’s understand how it was possible and what was the vulnerability. this post won’t be about the statistics but more about the technical. In this article, we will be focusing on two of these opcodes (create and create2), their differences, and how they were smartly combined in the execution of the tornado cash dao hack. On may 13th, tornado cash governance was hacked. let’s understand how it was possible and what was the vulnerability. this post won’t be about the statistics but more about the technical route of the attack. the attacker mainly used create, create2, and selfdestruct to exploit the governance. Option ii: use create2 to create the deployer contract (0x7dc8), which further deploys the malicious proposal contract (0xc503) using create. then the deployer contract is self destructed (to reset the nonce), and it can create a new proposal at the same address (0xc503).
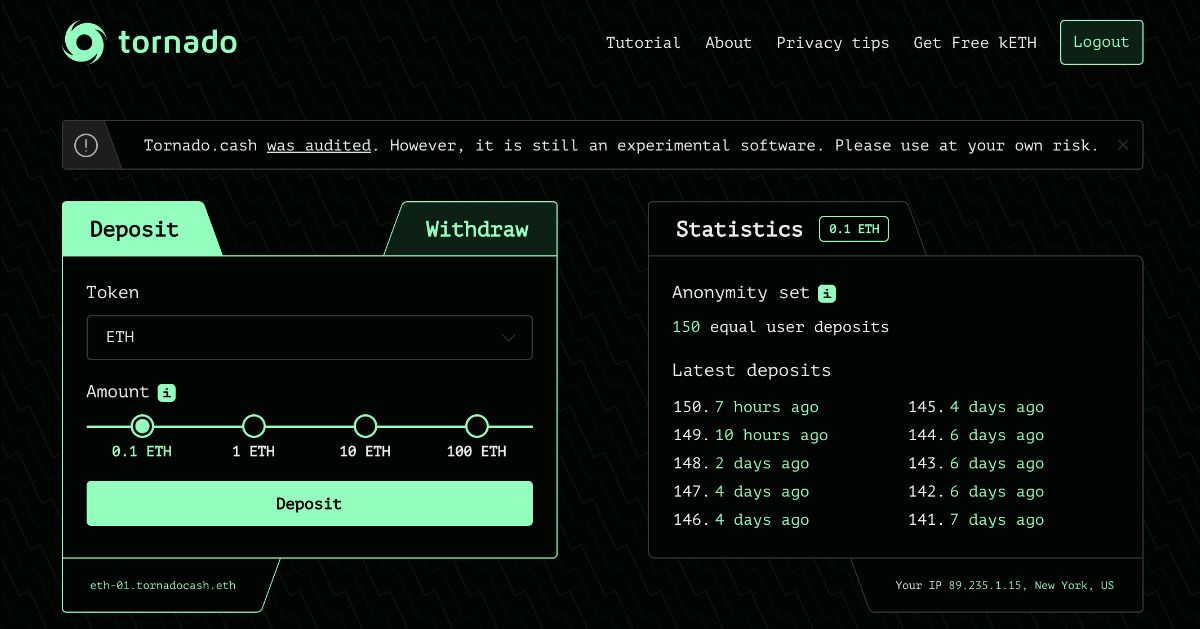
Us Treasury Ofac Releases Clarifications On Tornado Cash Sanctions On may 13th, tornado cash governance was hacked. let’s understand how it was possible and what was the vulnerability. this post won’t be about the statistics but more about the technical. In this article, we will be focusing on two of these opcodes (create and create2), their differences, and how they were smartly combined in the execution of the tornado cash dao hack. On may 13th, tornado cash governance was hacked. let’s understand how it was possible and what was the vulnerability. this post won’t be about the statistics but more about the technical route of the attack. the attacker mainly used create, create2, and selfdestruct to exploit the governance. Option ii: use create2 to create the deployer contract (0x7dc8), which further deploys the malicious proposal contract (0xc503) using create. then the deployer contract is self destructed (to reset the nonce), and it can create a new proposal at the same address (0xc503).
What You Need To Know About Tornado Cash Sanctions On may 13th, tornado cash governance was hacked. let’s understand how it was possible and what was the vulnerability. this post won’t be about the statistics but more about the technical route of the attack. the attacker mainly used create, create2, and selfdestruct to exploit the governance. Option ii: use create2 to create the deployer contract (0x7dc8), which further deploys the malicious proposal contract (0xc503) using create. then the deployer contract is self destructed (to reset the nonce), and it can create a new proposal at the same address (0xc503).

Tornado Cash And Blockchain Privacy A Primer For Economists And
Comments are closed.