Tokenization For Improved Data Security Main Data Security Tokenization

Tokenization For Improved Data Security Main Data Security Tokenization Tokenization (data security) this is a simplified example of how mobile payment tokenization commonly works via a mobile phone application with a credit card. [1][2] methods other than fingerprint scanning or pin numbers can be used at a payment terminal. Learn how data tokenization works, key benefits, types and real world tokenization examples to protect sensitive information.
Tokenization For Improved Data Security Data Tokenization Tools Key Data tokenization makes it possible for an organization to remove or disguise any or all sensitive data elements from their in house data systems. as a result, there is less—or no—valuable data for hackers to steal, which helps reduce the organization’s vulnerability to data breaches. Learn how tokenization enhances data security by replacing sensitive information with tokens, reducing risk of breaches and supporting robust cybersecurity strategies. Industries subject to financial, data security, regulatory, or privacy compliance standards are increasingly looking for tokenization solutions to minimize distribution of sensitive data, reduce risk of exposure, improve security posture, and alleviate compliance obligations. Tokenization in data security is a powerful technique, transforming sensitive data into meaningless substitutes, known as tokens. this process protects confidential information without compromising its usability.

Tokenization For Improved Data Security Tokenization Global Market Industries subject to financial, data security, regulatory, or privacy compliance standards are increasingly looking for tokenization solutions to minimize distribution of sensitive data, reduce risk of exposure, improve security posture, and alleviate compliance obligations. Tokenization in data security is a powerful technique, transforming sensitive data into meaningless substitutes, known as tokens. this process protects confidential information without compromising its usability. Data tokenization is a data security technique that replaces sensitive information with non sensitive equivalents called tokens. these tokens serve as surrogates for actual data, which remains securely stored in a separate controlled environment known as a token vault. Protect sensitive data with tokenization. learn how data tokenization works, its benefits, real world examples, and how to implement it for security and compliance. Discover how we guide you through implementing tokenization best practices, avoiding common missteps to ensure secure data protection. Tokenization provides a powerful way to protect sensitive information while still allowing for essential data operations. by replacing sensitive data with non sensitive substitutes, tokens.

Tokenization For Improved Data Security Tokenization Performance Data tokenization is a data security technique that replaces sensitive information with non sensitive equivalents called tokens. these tokens serve as surrogates for actual data, which remains securely stored in a separate controlled environment known as a token vault. Protect sensitive data with tokenization. learn how data tokenization works, its benefits, real world examples, and how to implement it for security and compliance. Discover how we guide you through implementing tokenization best practices, avoiding common missteps to ensure secure data protection. Tokenization provides a powerful way to protect sensitive information while still allowing for essential data operations. by replacing sensitive data with non sensitive substitutes, tokens.
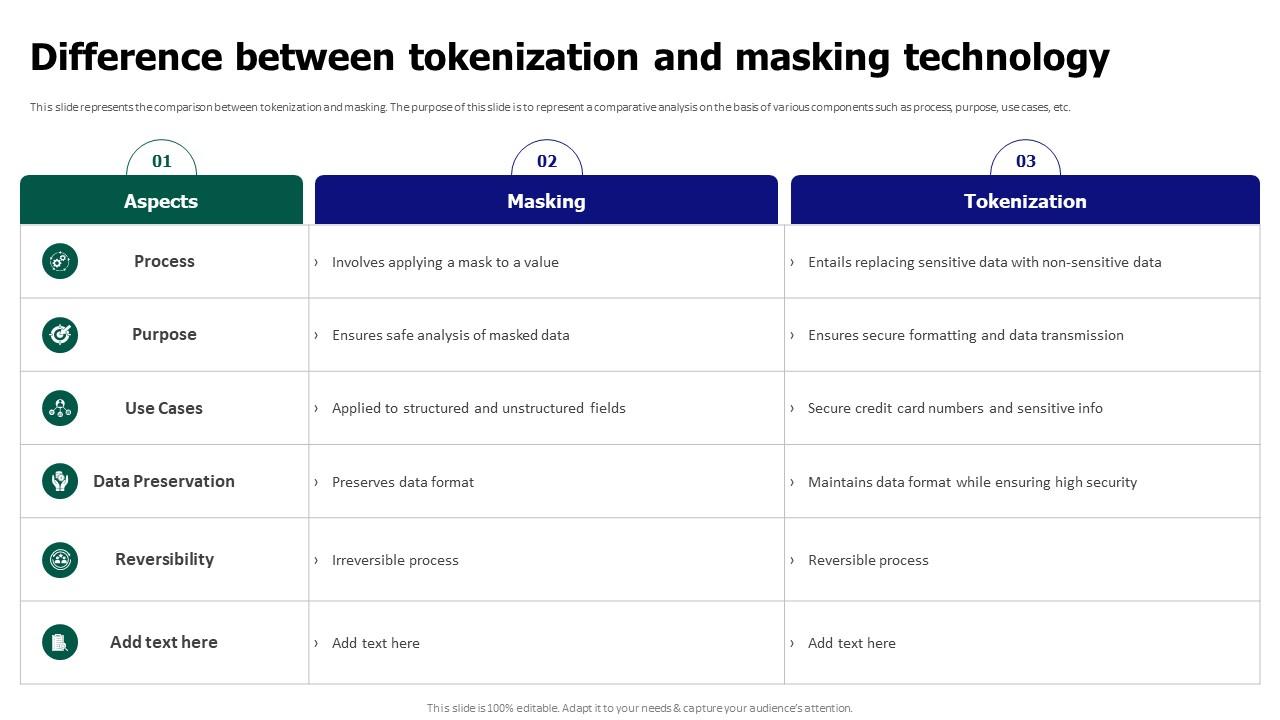
Tokenization For Improved Data Security Difference Between Tokenization Discover how we guide you through implementing tokenization best practices, avoiding common missteps to ensure secure data protection. Tokenization provides a powerful way to protect sensitive information while still allowing for essential data operations. by replacing sensitive data with non sensitive substitutes, tokens.
Comments are closed.