Tls Handshake Pdf Transport Layer Security Public Key Cryptography

Tls Handshake Pdf Transport Layer Security Public Key Cryptography After server’s certificate is verified, client generates random number, called pre master secret. client encrypts pre master secret using server’s public key and sends to the server. length of the key depends on the public key algorithm used. • uses the secret keys established in the handshake protocol to protect confidentiality, integrity, and authenticity of data exchange between the client and the server.
Transport Layer Security Tls Handshake Geeksforgeeks Understanding tls and the handshake free download as pdf file (.pdf), text file (.txt) or view presentation slides online. In this chapter, we first discuss how transport layer security works. we specifically focus on the two most important aspects of tls: handshake and data transmission. A tls handshake is the process that kicks off a communication session that uses tls. during a tls handshake, the two communicating sides exchange messages to acknowledge each other, verify each other, establish the cryptographic algorithms they will use, and agree on session keys. Both client and server generate a diffie–hellman public key. after these are exchanged, each side performs the diffie–hellman calculation to create the shared pre master secret.
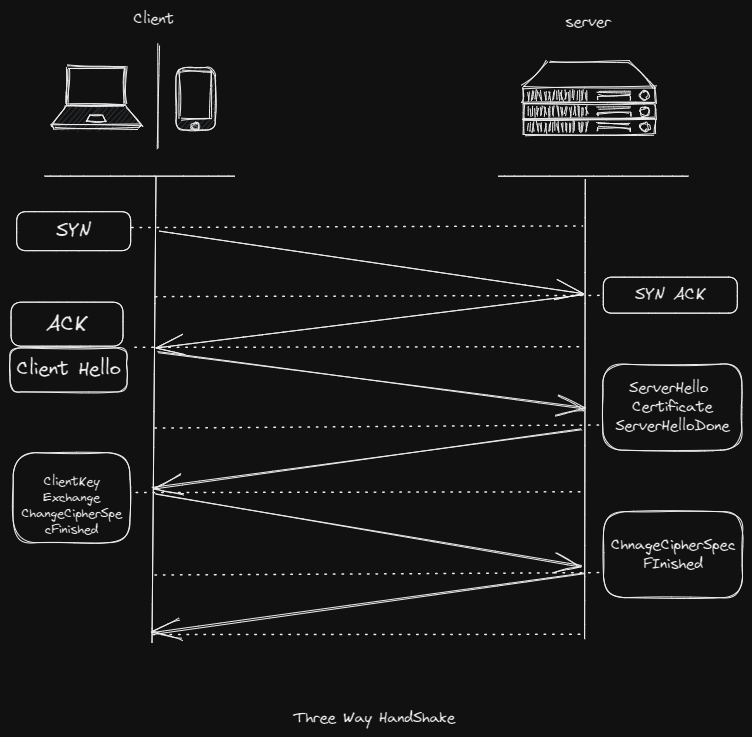
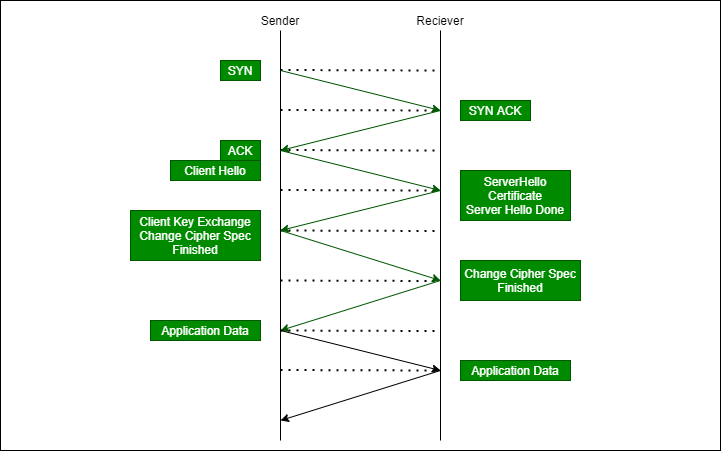
Tls Transport Layer Security Themayurkumbhar A tls handshake is the process that kicks off a communication session that uses tls. during a tls handshake, the two communicating sides exchange messages to acknowledge each other, verify each other, establish the cryptographic algorithms they will use, and agree on session keys. Both client and server generate a diffie–hellman public key. after these are exchanged, each side performs the diffie–hellman calculation to create the shared pre master secret. Tls consists of two primary components: a handshake protocol (section 4) that authenticates the communicating parties, negotiates cryptographic modes and parameters, and establishes shared keying material. This report explains what happens during the tls handshaking process. we need tls (transport layer security protocol) to make sure the data is safe, and the communication is private and. Tls is a successor to secure socket layer (ssl) protocol. ssl v3.0 and tls v1.0 were very similar but it was replaced with tls. you can also refer to transport layer security (tls). a transport layer security (tls) connection is established via handshake. tls handshake in action : figure tls handshake. Transport layer security (tls) is a cryptographic protocol that is designed to provide both security and data integrity for communications over a reli able transport protocol such as transport control protocol (tcp).

Tls Pdf Transport Layer Security Public Key Cryptography Tls consists of two primary components: a handshake protocol (section 4) that authenticates the communicating parties, negotiates cryptographic modes and parameters, and establishes shared keying material. This report explains what happens during the tls handshaking process. we need tls (transport layer security protocol) to make sure the data is safe, and the communication is private and. Tls is a successor to secure socket layer (ssl) protocol. ssl v3.0 and tls v1.0 were very similar but it was replaced with tls. you can also refer to transport layer security (tls). a transport layer security (tls) connection is established via handshake. tls handshake in action : figure tls handshake. Transport layer security (tls) is a cryptographic protocol that is designed to provide both security and data integrity for communications over a reli able transport protocol such as transport control protocol (tcp).
Comments are closed.