Threat Modeling Template
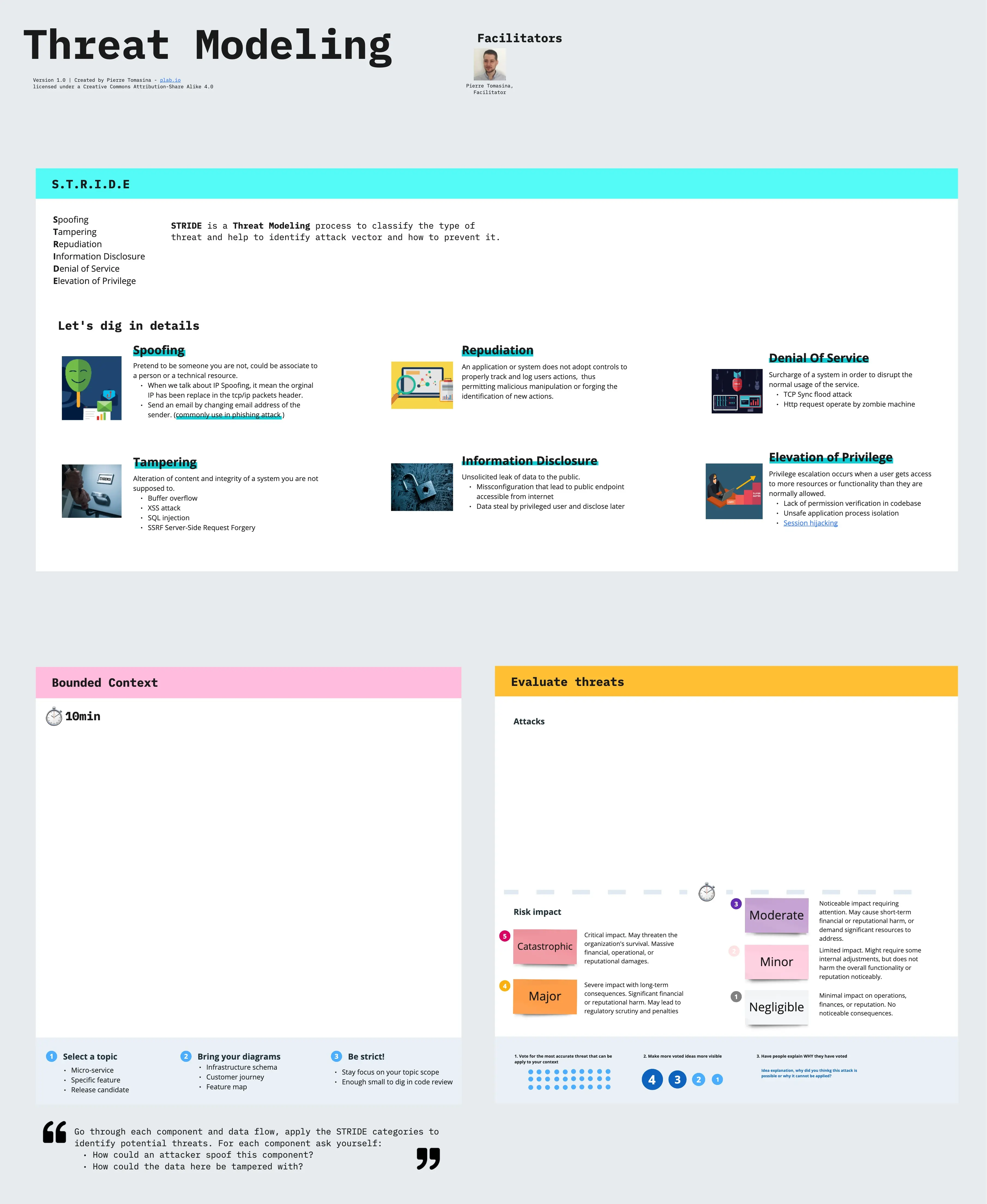
Threat Modeling Stride Template Miroverse Templates for the microsoft threat modeling tool. contribute to azurearchitecture threat model templates development by creating an account on github. A steb by step guide to creating a structured and repeatable threat model to identify threats and mitigate them against valuable assets in a system.
Threat Modeling Template Inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will break the threat modeling down into four basic steps: application decomposition, threat identification and ranking, mitigations, and review and validation. A cybersecurity risk assessment template is a repeatable blueprint that guides organizations through the systematic identification, analysis, and treatment of cyber‑related threats to their most …. The miro threat model template offers an efficient, inclusive, and comprehensive approach to threat modeling. by using miro’s collaborative features and integration capabilities, teams can transcend traditional methods and ensure robust security practices. Our custom made threat model templates ensure your threat assessments maintain professional consistency and visual impact. deploy these powerpoint slides to strengthen your cybersecurity strategy and secure stakeholder buy in.
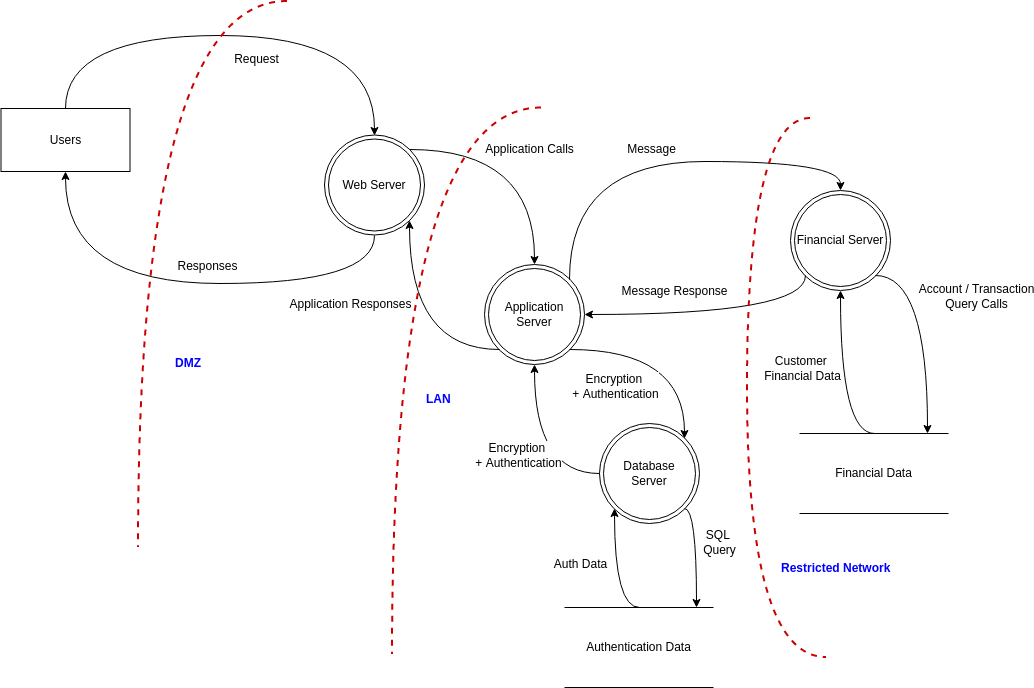
Threat Modeling Template The miro threat model template offers an efficient, inclusive, and comprehensive approach to threat modeling. by using miro’s collaborative features and integration capabilities, teams can transcend traditional methods and ensure robust security practices. Our custom made threat model templates ensure your threat assessments maintain professional consistency and visual impact. deploy these powerpoint slides to strengthen your cybersecurity strategy and secure stakeholder buy in. This document covers the threat modeling templates provided in this repository, which are xml based template files designed for use with the microsoft threat modeling tool. Use this threat modeling template with stride and dread to identify application threats, assess risk, and plan mitigations early. The goal of this section is to capture the documentation needed to accomplish building a successful threat model. if it is discovered later that additional information is required, ensure the “what are we working on?” section is updated with the latest information. Learn how to get started using the threat modeling tool. create a diagram, identify threats, mitigate threats, and validate each mitigation.
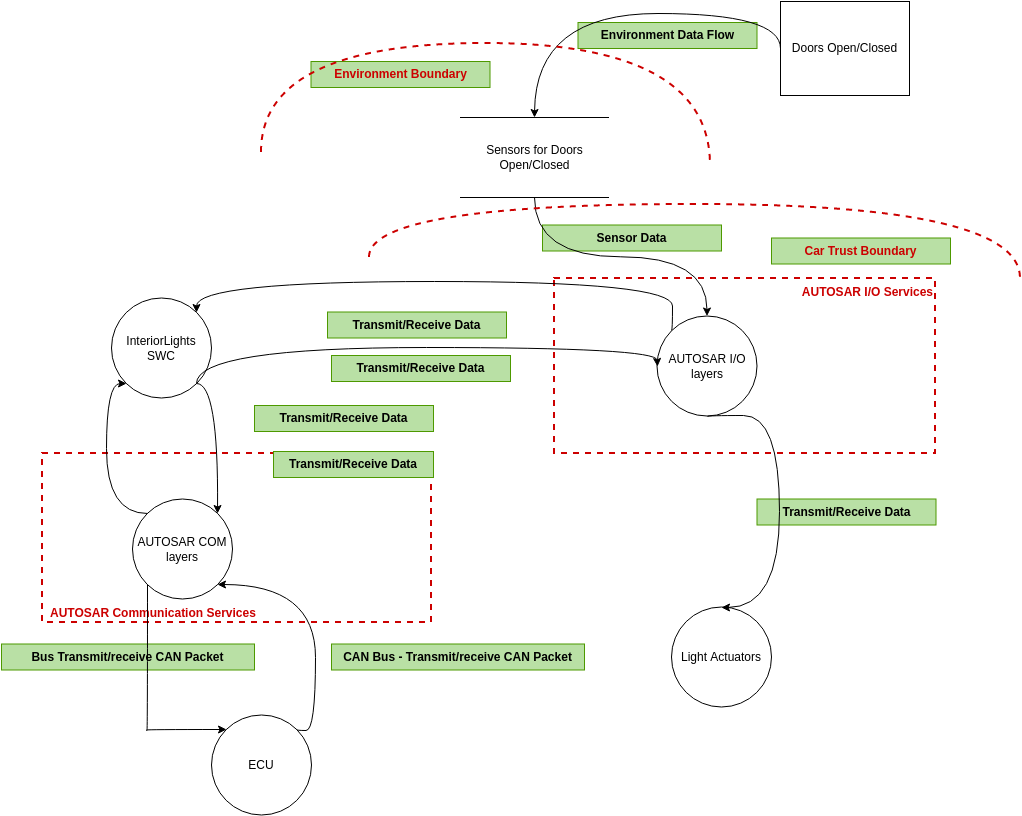
Threat Modeling Template This document covers the threat modeling templates provided in this repository, which are xml based template files designed for use with the microsoft threat modeling tool. Use this threat modeling template with stride and dread to identify application threats, assess risk, and plan mitigations early. The goal of this section is to capture the documentation needed to accomplish building a successful threat model. if it is discovered later that additional information is required, ensure the “what are we working on?” section is updated with the latest information. Learn how to get started using the threat modeling tool. create a diagram, identify threats, mitigate threats, and validate each mitigation.
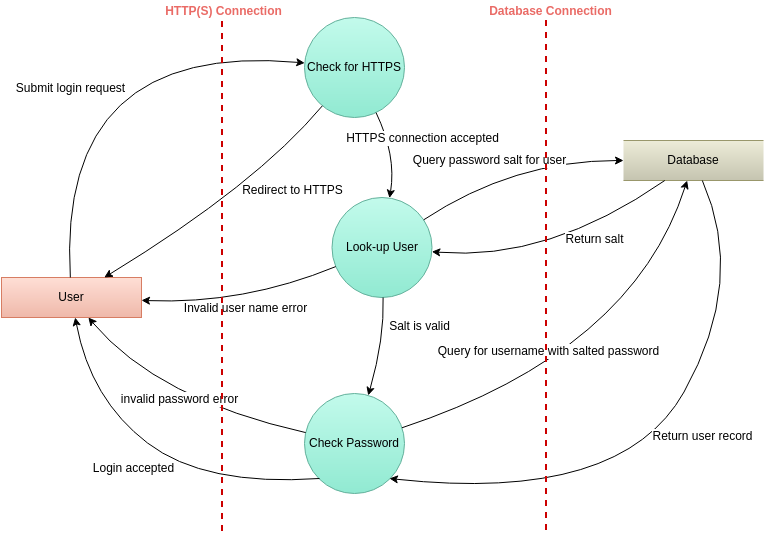
Stride Threat Modeling Example For Better Understanding And Learning The goal of this section is to capture the documentation needed to accomplish building a successful threat model. if it is discovered later that additional information is required, ensure the “what are we working on?” section is updated with the latest information. Learn how to get started using the threat modeling tool. create a diagram, identify threats, mitigate threats, and validate each mitigation.
Comments are closed.