Threat Modeling Project Devpost

Threat Modeling Project Devpost Our threat modeling application revolutionizes manual processes by empowering teams to foresee, identify, and mitigate vulnerabilities before they're exploited. Threat designer is a generativeai application designed to automate and streamline the threat modeling process for secure system design. the open threat modeling format (otm) defines a platform independent way to define the threat model of any system. templates for the microsoft threat modeling tool. this repo contains logstash of various honeypots.
Threat Modeling Project Devpost The project trains a custom bert inspired threat detection model for network packet‑level encoder learns masked‑language‑model (mlm) and self‑flow‑based (sfbo) objectives on raw packet token sequences. Your goal: build ai systems on the sift workstation that match that velocity triaging, correlating, and reporting at the pace the threat demands. this hackathon is how. This project is inspired by the growing need for automated systems to monitor and secure networks in real time. as more businesses move online, the risks of cyberattacks continue to increase, and i wanted to contribute a solution that could help mitigate these risks. Inspired by the potential of artificial intelligence to revolutionize threat detection and response, this project aims to develop a system that combines real time analysis, predictive modeling, and automation to enhance cybersecurity measures.
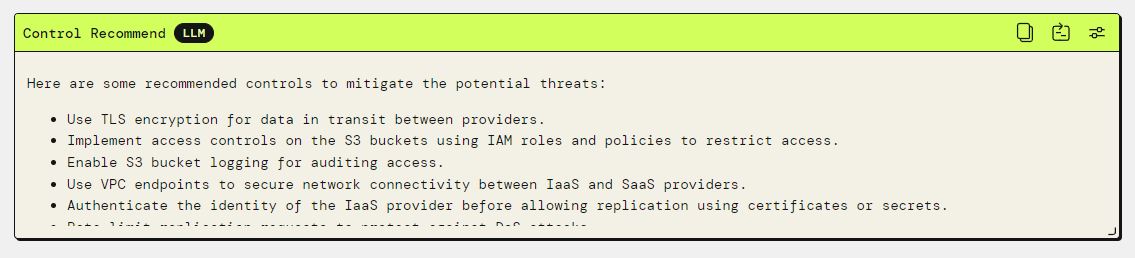
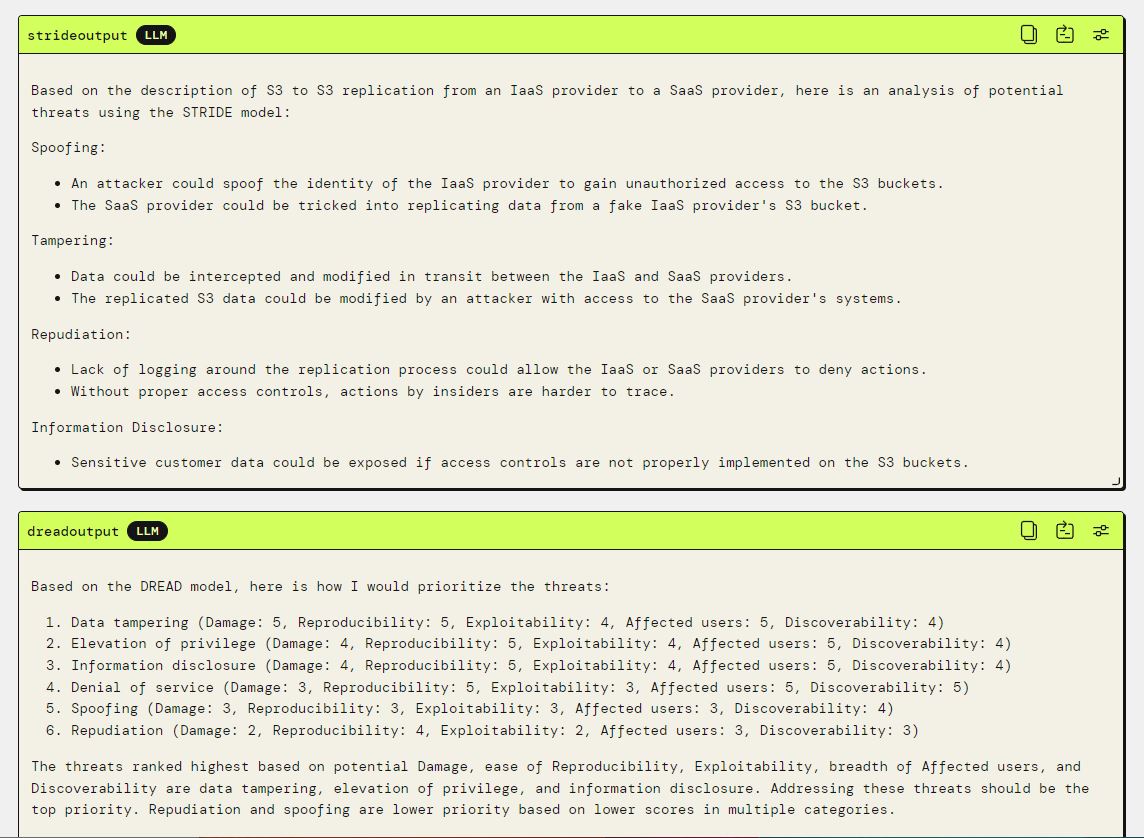
Threat Modeling Project Devpost This project is inspired by the growing need for automated systems to monitor and secure networks in real time. as more businesses move online, the risks of cyberattacks continue to increase, and i wanted to contribute a solution that could help mitigate these risks. Inspired by the potential of artificial intelligence to revolutionize threat detection and response, this project aims to develop a system that combines real time analysis, predictive modeling, and automation to enhance cybersecurity measures. Inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will break the threat modeling down into four basic steps: application decomposition, threat identification and ranking, mitigations, and review and validation. This paper contains some reflections on how it is possible to adopt threat modeling more effectively and efficiently, integrating it with modern devops methodologies and tools, and focusing on the value provided to all the various actors involved with the software development lifecycle. Explore our detailed threat modeling example list. learn stride, pasta, attack trees, and more to secure your ci cd workflows and codebases. The best resource to start learning about threat modeling or improving your existing process, is the threat modeling manifesto. this manifesto was created by a group of leading threat modeling professionals.
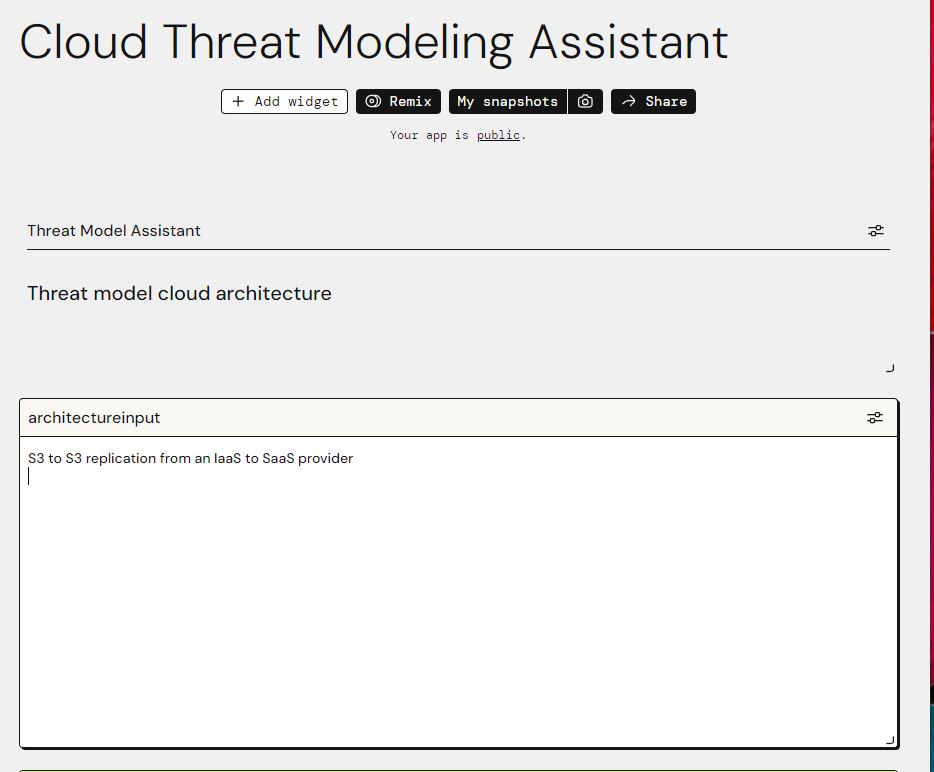
Threat Modeling Project Devpost Inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will break the threat modeling down into four basic steps: application decomposition, threat identification and ranking, mitigations, and review and validation. This paper contains some reflections on how it is possible to adopt threat modeling more effectively and efficiently, integrating it with modern devops methodologies and tools, and focusing on the value provided to all the various actors involved with the software development lifecycle. Explore our detailed threat modeling example list. learn stride, pasta, attack trees, and more to secure your ci cd workflows and codebases. The best resource to start learning about threat modeling or improving your existing process, is the threat modeling manifesto. this manifesto was created by a group of leading threat modeling professionals.

Threat Modeling Archives Threat Modeling Explore our detailed threat modeling example list. learn stride, pasta, attack trees, and more to secure your ci cd workflows and codebases. The best resource to start learning about threat modeling or improving your existing process, is the threat modeling manifesto. this manifesto was created by a group of leading threat modeling professionals.
Threat Modeling And Devops Threat Modeling
Comments are closed.