Threat Modeling Ebell S Docs
301 Moved Permanently We threat model to anticipate problems when it is inexpensive to deal with them. threat modeling falls under threat assessment in the software assurance maturity model. This document explains the threat modeling processes regarded as industry best practice and now required as a precondition for audits requested from the sdf audit bank.

Threat Modeling 101 Png Here is an example of a threat modeling document which talks about the architecture and different phases involved in the threat modeling. this document can be used as reference template for creating threat modeling documents. Inspired by these commonalities and guided by the four key questions of threat modeling discussed above, this cheatsheet will break the threat modeling down into four basic steps: application decomposition, threat identification and ranking, mitigations, and review and validation. Definition of threat modeling: a structured process for identifying and evaluating potential threats, and determining ways to mitigate the risks posed by these threats. Making threat modeling a core component of your sdlc can help increase product security. the threat modeling process can be decomposed into four high level steps. frequently, each step is documented as it is carried out. the resulting document is the threat model for the application.
Getting Started With Threat Modeling Pdf Vulnerability Computing Definition of threat modeling: a structured process for identifying and evaluating potential threats, and determining ways to mitigate the risks posed by these threats. Making threat modeling a core component of your sdlc can help increase product security. the threat modeling process can be decomposed into four high level steps. frequently, each step is documented as it is carried out. the resulting document is the threat model for the application. These models can be considered as reference template to show how we can construct threat modeling document. each of the labeled entities in the figures below are accompanied by meta information which describe the threats, recommended mitigations, and the associated security principle or goal. That’s why we want to create a guideline for every technical people to help them to start with threat modelling and to choose the most effective threat modelling method for the purpose. We designed the tool with non security experts in mind, making threat modeling easier for all developers by providing clear guidance on creating and analyzing threat models. Explore the four high level steps of threat modeling. this engineering technique identifies potential threats early in the development lifecycle.
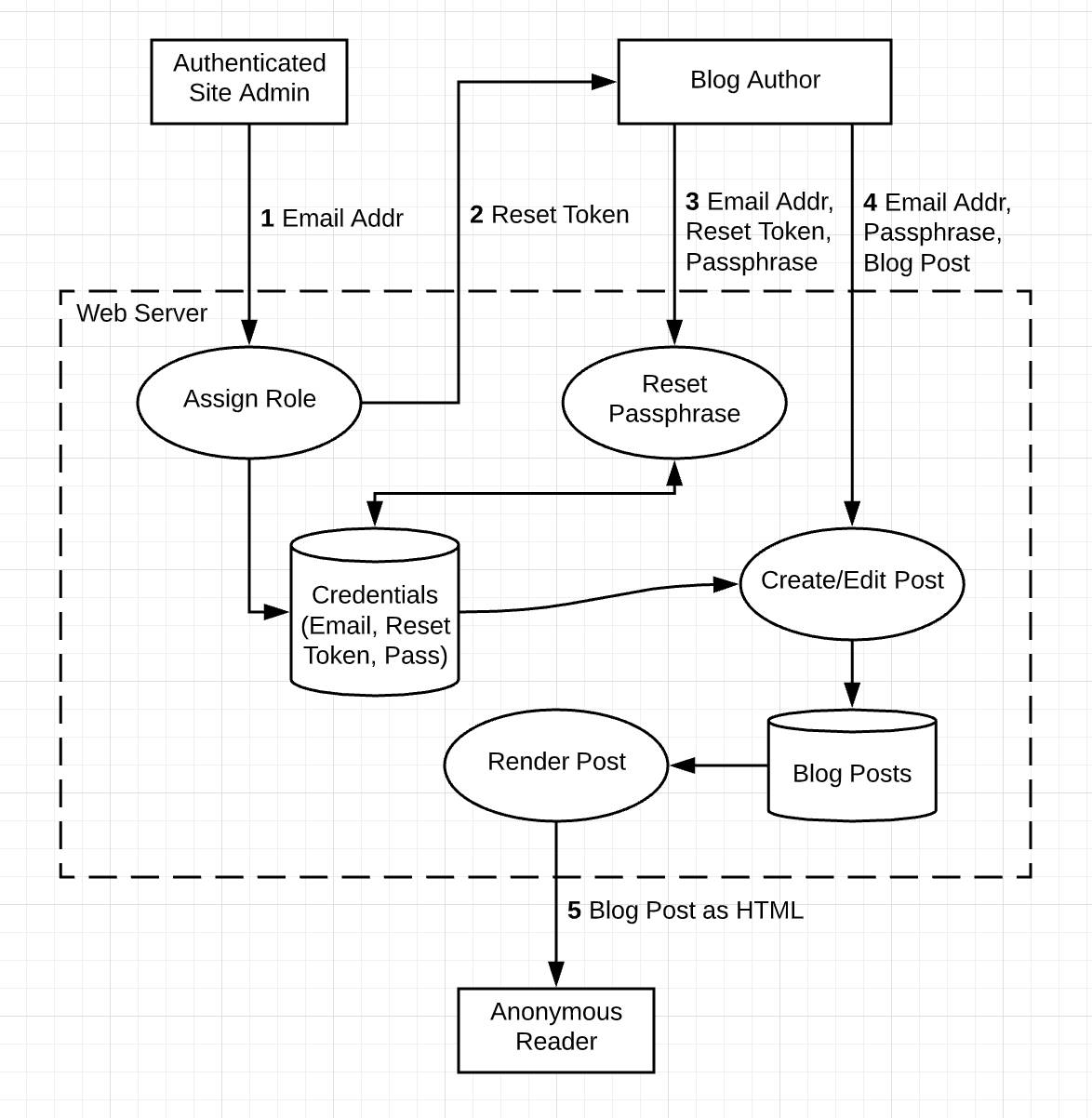
Threat Modeling Ebell S Docs These models can be considered as reference template to show how we can construct threat modeling document. each of the labeled entities in the figures below are accompanied by meta information which describe the threats, recommended mitigations, and the associated security principle or goal. That’s why we want to create a guideline for every technical people to help them to start with threat modelling and to choose the most effective threat modelling method for the purpose. We designed the tool with non security experts in mind, making threat modeling easier for all developers by providing clear guidance on creating and analyzing threat models. Explore the four high level steps of threat modeling. this engineering technique identifies potential threats early in the development lifecycle.

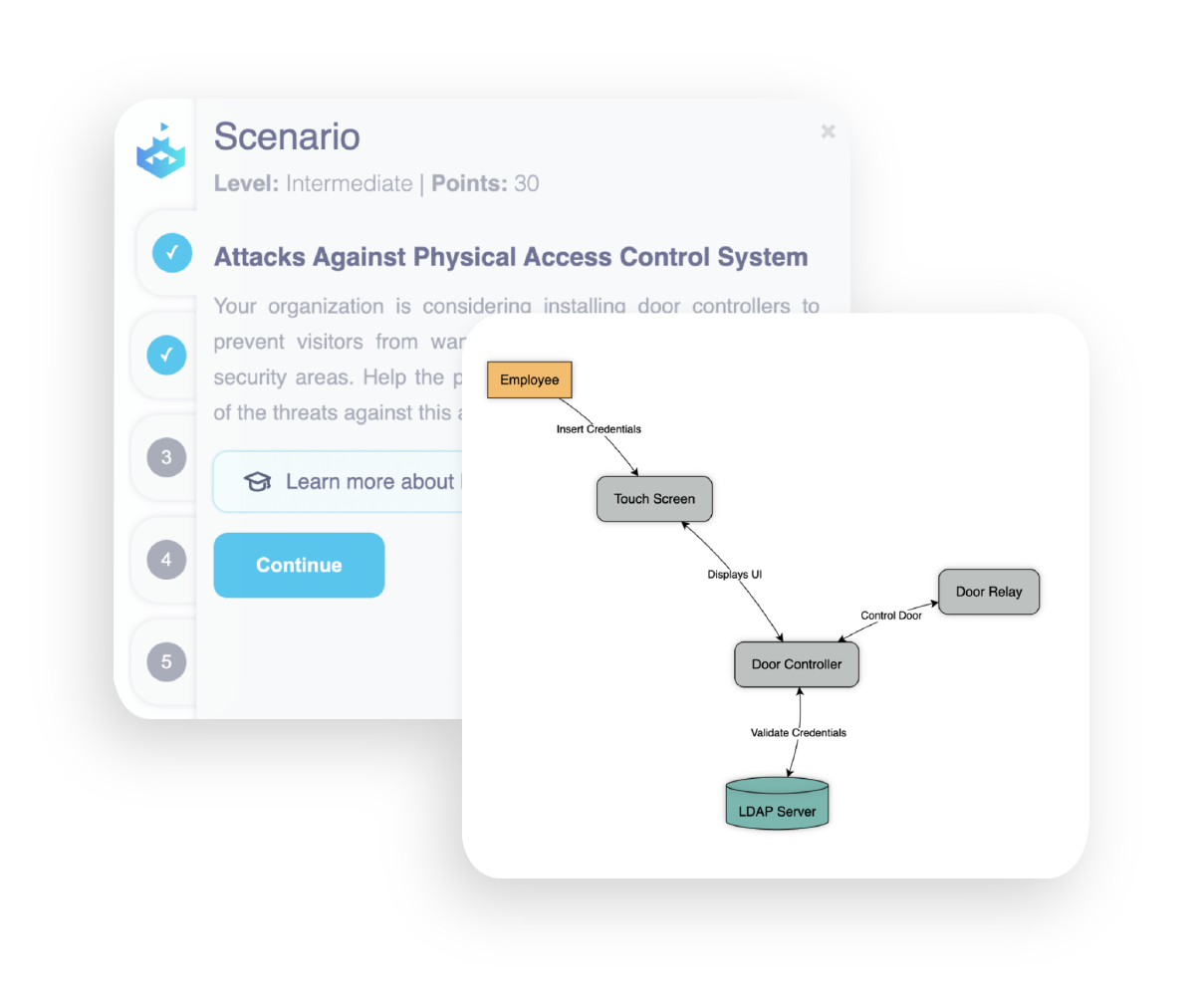
Threat Modeling Tool Visual Paradigm We designed the tool with non security experts in mind, making threat modeling easier for all developers by providing clear guidance on creating and analyzing threat models. Explore the four high level steps of threat modeling. this engineering technique identifies potential threats early in the development lifecycle.
Comments are closed.