This Github Action Was Malware
How To Find Malware On Github Astral When your workflow ran trivy [email protected] (or any of the other 74 compromised tags), github pulled the code from the new commit the tag pointed to, not the original release. Trivy, a popular open source vulnerability scanner maintained by aqua security, was compromised a second time within the span of a month to deliver malware capable of stealing sensitive ci cd secrets.

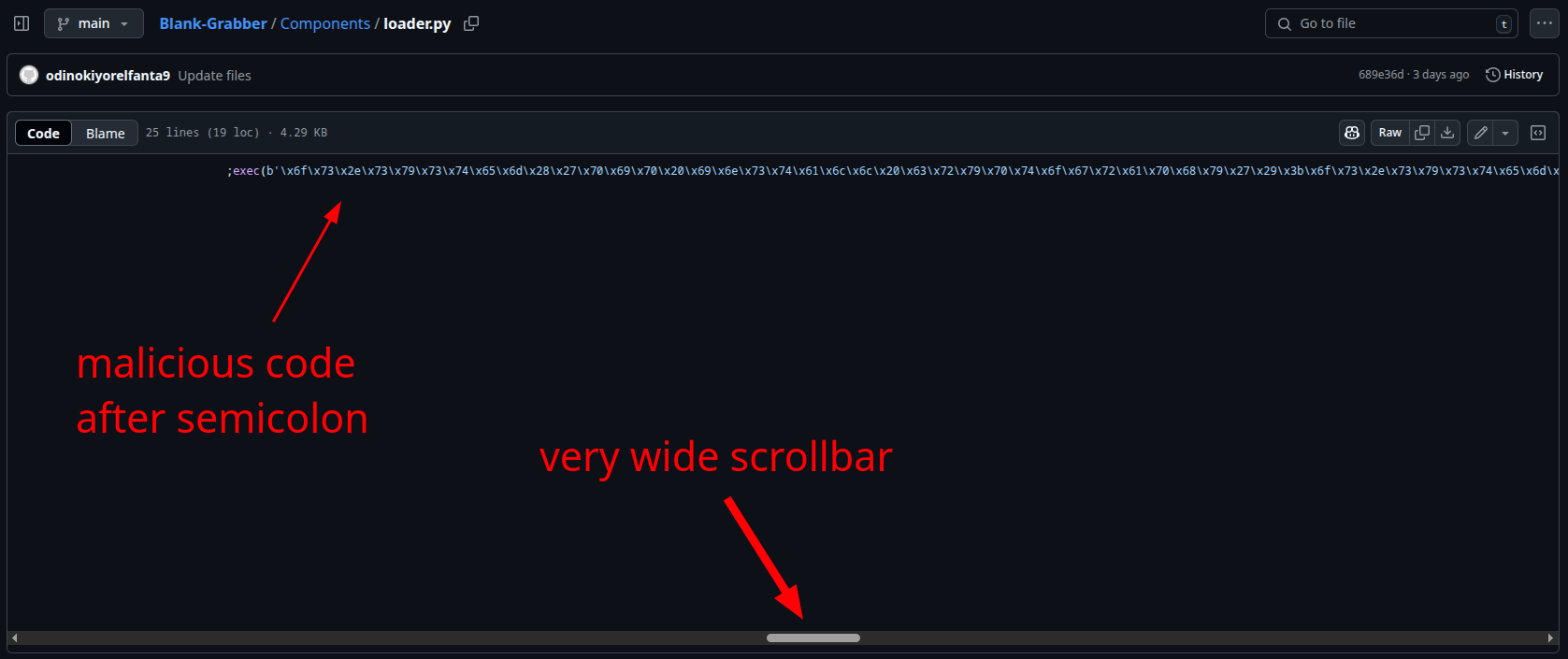
Malware In Github Repositories Is Spread From Fake Security Company Name A malicious script has been injected into all existing git tags. while the master branch currently appears clean, every release tag now points to a malicious commit that was not authored by the original maintainers. The stepsecurity threat intelligence team has discovered an ongoing campaign in which an attacker is compromising hundreds of github accounts and injecting identical malware into hundreds of python repositories. The software supply chain is under siege from “shai hulud v2,” a sophisticated malware campaign that has compromised 834 packages across the npm and maven ecosystems. A supply chain attack on the widely used 'tj actions changed files' github action, used by 23,000 repositories, potentially allowed threat actors to steal ci cd secrets from github.
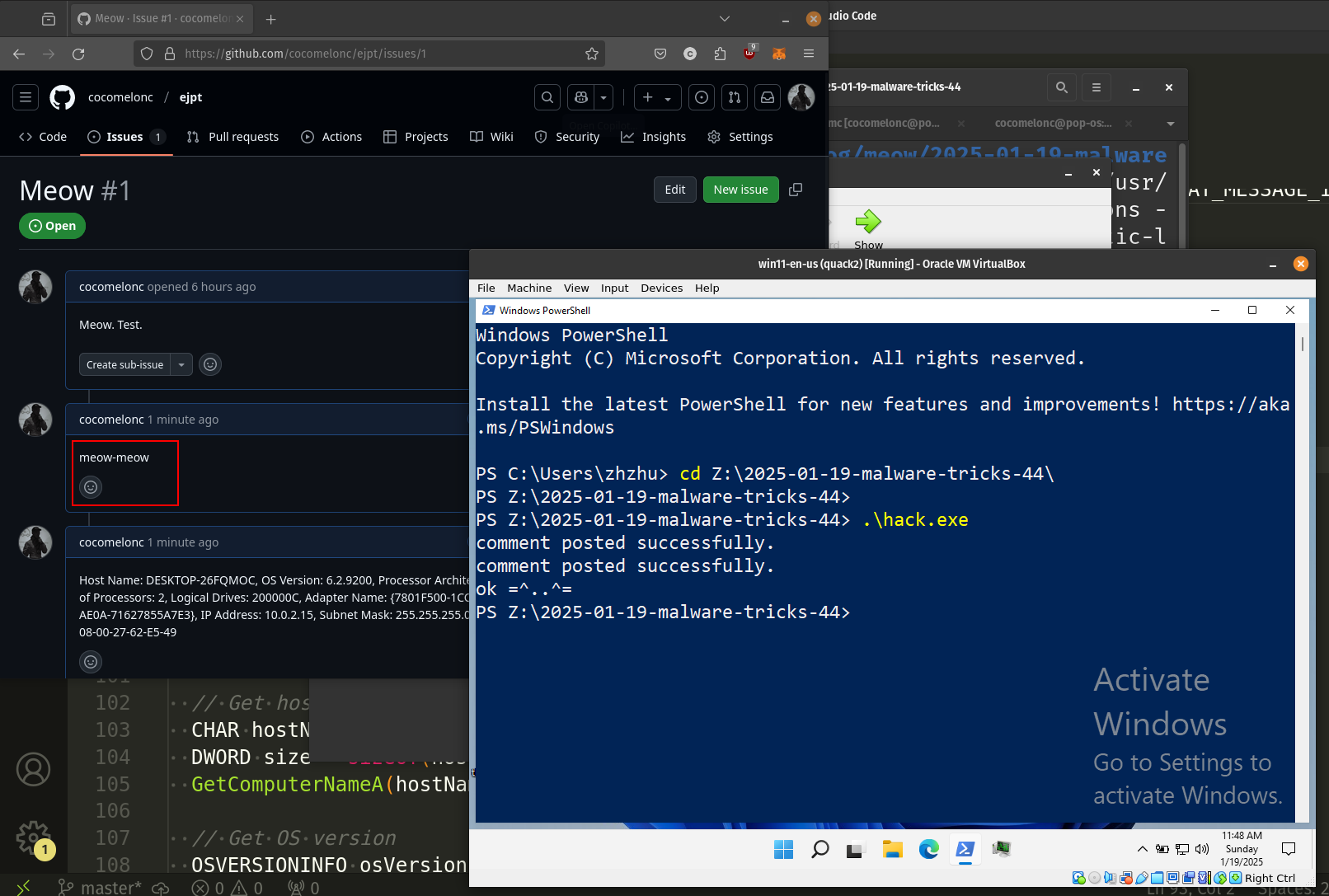
Malware Development Trick 44 Stealing Data Via Legit Github Api The software supply chain is under siege from “shai hulud v2,” a sophisticated malware campaign that has compromised 834 packages across the npm and maven ecosystems. A supply chain attack on the widely used 'tj actions changed files' github action, used by 23,000 repositories, potentially allowed threat actors to steal ci cd secrets from github. In this article, we’ll begin to explore a few of the github repositories that the sysdig trt was able to compromise and help secure, including projects maintained by organizations like mitre, splunk, and others built by the community. Over the past weekend, security researchers discovered that the popular github action tj actions changed files has been compromised. malicious code added to the action attempts to extract secrets from ci cd workflows, posing a significant security threat to thousands of repositories. We created a closed demo environment to show how a github actions worm takes advantage of the methods used to spread malware to any infectable repository across the github actions dependency tree. On september 5, 2025, gitguardian discovered ghostaction, a massive supply chain attack affecting 327 github users across 817 repositories. attackers injected malicious workflows that exfiltrated 3,325 secrets, including pypi, npm, and dockerhub tokens via http post requests to a remote endpoint.
Comments are closed.