Thesis Topic Proposal Paper Cybersecurity Pdf Security Computer

Thesis Topic Proposal Paper Cybersecurity Pdf Security Computer The document proposes a research thesis on cybersecurity and privacy topics such as threat detection using machine learning, securing iot devices, using blockchain technology, and addressing privacy issues on social media. Pdf | on mar 12, 2023, chibuike israel uzoagba published research proposal for cyber security and resilience | find, read and cite all the research you need on researchgate.
Master Proposal Ideas In Cyber Security A comprehensive framework for cyber security that can be applied to organizations and individuals. a set of guidelines and best practices for preventing, detecting, responding to, and recovering from cyber attacks. case studies on the application of the framework to real world scenarios. Abstract urrounds cyber security investments. chief information officers (cios) operate with limited resources and typically do not know the relative risk of different cyber attack vectors, such as malicious ema. At phdservices.org, we offer a variety of cyber security thesis topics for you to choose from based on your interests. we will provide you with a concise outline for your selected topic. The objective of this research is to deeply examining the information security problems that are found in cloud computing, propose a comprehensive security solution to minimize the security risks of cloud service providers and customers.

Research Paper Cyber Security Pdf Security Computer Security At phdservices.org, we offer a variety of cyber security thesis topics for you to choose from based on your interests. we will provide you with a concise outline for your selected topic. The objective of this research is to deeply examining the information security problems that are found in cloud computing, propose a comprehensive security solution to minimize the security risks of cloud service providers and customers. With an in depth anal ysis of the code auditing process and techniques, this thesis aspires to provide a valuable understanding and hands on recommendations for developers, security professionals, and other related organizations to improve the security posture of their software applications. The research of this thesis will focus on the analysis of cybersecurity issues in the iot, the threats and security vulnerabilities that arise, the proposed countermeasures and solutions from a cyber technical point of view, through various cybersecurity frameworks, models and methodologies. The developed multi layered security framework can be employed in a real world environment to enhance the security of is. the proposed solution can be extended to other sectors with similar security requirements. table of contents certification . ii. More specific to cybersecurity, the trespass project (trespass project, 2014) identified and analyzed eighteen risk assessment methods, as well as four information security risk assessment standards.

Proposal Itt320 Pdf Security Computer Security With an in depth anal ysis of the code auditing process and techniques, this thesis aspires to provide a valuable understanding and hands on recommendations for developers, security professionals, and other related organizations to improve the security posture of their software applications. The research of this thesis will focus on the analysis of cybersecurity issues in the iot, the threats and security vulnerabilities that arise, the proposed countermeasures and solutions from a cyber technical point of view, through various cybersecurity frameworks, models and methodologies. The developed multi layered security framework can be employed in a real world environment to enhance the security of is. the proposed solution can be extended to other sectors with similar security requirements. table of contents certification . ii. More specific to cybersecurity, the trespass project (trespass project, 2014) identified and analyzed eighteen risk assessment methods, as well as four information security risk assessment standards.

Cyber Security File Pdf Computer Security Security The developed multi layered security framework can be employed in a real world environment to enhance the security of is. the proposed solution can be extended to other sectors with similar security requirements. table of contents certification . ii. More specific to cybersecurity, the trespass project (trespass project, 2014) identified and analyzed eighteen risk assessment methods, as well as four information security risk assessment standards.

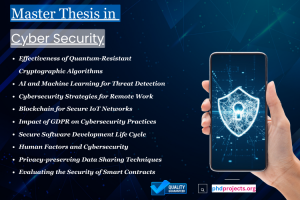
Trending Top 15 Cybersecurity Thesis Topics Research Domain
Comments are closed.