Thesis Pdf Cryptography Applied Mathematics
Mathematics In Cryptography Pdf Encryption Cryptography Ryptography and public key cryptography. in symmetric key encryp tion the message is encrypted using a key and the same key is used to decrypt the message, wh. ch makes it easy to use but less secure. the data encryption standard (des) and the advance encryption stan dard (aes) are exampl. In [15], nist gives an overview of lightweight cryptography, and summarizes their findings under some main titles such as target devices and performance metrics.

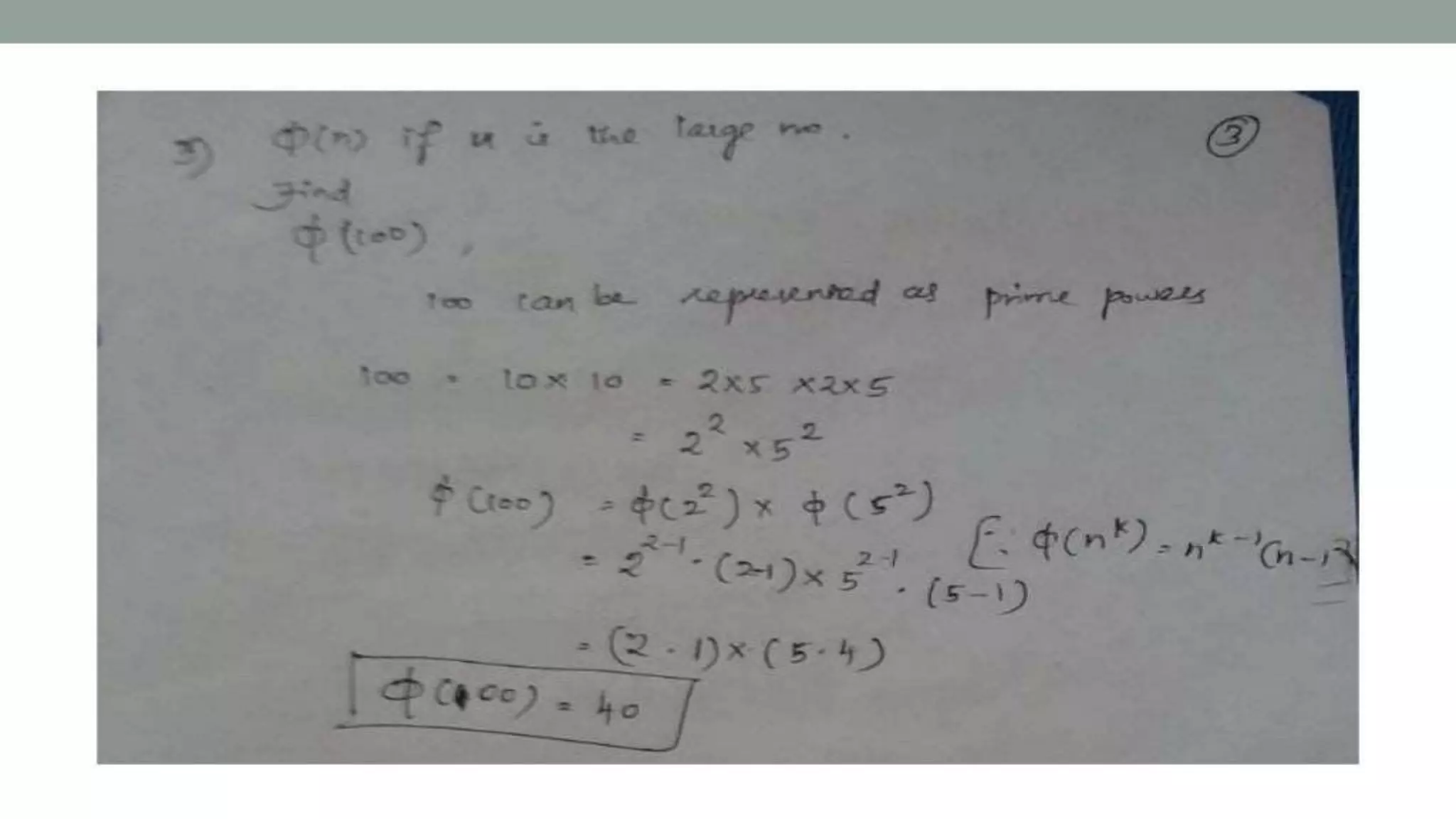
3 Mathematics Of Cryptography Download Free Pdf Matrix Mathematics The document is eleftheria makri's phd dissertation presented to ku leuven's faculty of engineering science. the dissertation, supervised by prof. bart preneel and prof. frederik vercauteren, focuses on secure and efficient computing on private data. Abstract— cryptography has a crucial role in securing data by preventing unauthorized access and ensuring the confidentiality and integrity of data. among various cryptographic techniques that have been developed, the hill cipher stands out as an early method founded on linear algebra principles. Mathematics of cryptography is the study of mathematical theories and techniques used to secure communication and data through encryption and decryption processes. Pdf | this thesis explores how number theory forms the backbone of modern cryptography, ensuring secure digital communication and data protection.

Number Theory Applications In Cryptography Pdf Cryptography Mathematics of cryptography is the study of mathematical theories and techniques used to secure communication and data through encryption and decryption processes. Pdf | this thesis explores how number theory forms the backbone of modern cryptography, ensuring secure digital communication and data protection. List of dissertations theses on the topic 'cryptography – mathematics'. scholarly publications with full text pdf download. related research topic ideas. Quantum safe cryptographic systems is based on lattices. in order to im prove the performance in lattice based systems, number theoretic transforms (ntt) are used. in this thesis. A mathematical object called an elliptic curve can be used in the construction of public key cryptosystems. this thesis focuses on speeding up elliptic curve cryptography which is an attractive alternative to traditional public key cryptosystems such as rsa. Imperfect forward secrecy: how diffie hellman fails in practice (2015) adrian, bhargavan, durumeric, gaudry, green, halderman, heninger, springall, thomé, valenta, vandersloot, wustrow, zanella béguelin, zimmermann.pdf.
Mathematics Of Asymmetric Cryptography Pptx List of dissertations theses on the topic 'cryptography – mathematics'. scholarly publications with full text pdf download. related research topic ideas. Quantum safe cryptographic systems is based on lattices. in order to im prove the performance in lattice based systems, number theoretic transforms (ntt) are used. in this thesis. A mathematical object called an elliptic curve can be used in the construction of public key cryptosystems. this thesis focuses on speeding up elliptic curve cryptography which is an attractive alternative to traditional public key cryptosystems such as rsa. Imperfect forward secrecy: how diffie hellman fails in practice (2015) adrian, bhargavan, durumeric, gaudry, green, halderman, heninger, springall, thomé, valenta, vandersloot, wustrow, zanella béguelin, zimmermann.pdf.
Comments are closed.