The Vulnerability Life Cycle

The Vulnerability Life Cycle Pdf Exploit Computer Security Explore the vulnerability management lifecycle, from discovery to remediation. learn its five key steps, challenges, and best practices for cybersecurity. The vulnerability management lifecycle is a continuous process for discovering, prioritizing and addressing vulnerabilities in a company's it assets.
Vulnerability Management Lifecycle 5 Step Process Explained There are five main stages in the vulnerability management lifecycle include: assess, prioritize, act, reassess, improve. learn more here. Learn the key stages of a modern vulnerability management lifecycle and find out how a unified approach to visibility can improve multi cloud security. The guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification scanning phase, the reporting phase, and remediation phase. The vulnerability management lifecycle is a continuous process to identify, prioritize, report, resolve, and verify vulnerabilities within your information systems and continually monitor, refine, and improve this process.
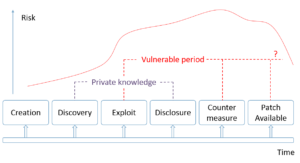
Vulnerability Life Cycle And Vulnerability Disclosures Alexander V The guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification scanning phase, the reporting phase, and remediation phase. The vulnerability management lifecycle is a continuous process to identify, prioritize, report, resolve, and verify vulnerabilities within your information systems and continually monitor, refine, and improve this process. The vulnerability management life cycle is a continuous process involving the discovery, assessment, prioritization, remediation, and verification of security vulnerabilities in an organization's it environment. What is the vulnerability management lifecycle (vml)? the vulnerability management lifecycle (vml) is a continuous process to plan, find vulnerabilities, prioritize fixes, resolve issues, and monitor for new threats. As cloud adoption accelerates and digital ecosystems expand, a consistent and mature vulnerability management lifecycle becomes essential for maintaining visibility, prioritizing risk, and driving effective remediation. Vulnerability management lifecycle represents the systematic evolution from episodic security activities to continuous operational discipline.

Exploring The Life Cycle Of Vulnerability Management In A Nutshell The vulnerability management life cycle is a continuous process involving the discovery, assessment, prioritization, remediation, and verification of security vulnerabilities in an organization's it environment. What is the vulnerability management lifecycle (vml)? the vulnerability management lifecycle (vml) is a continuous process to plan, find vulnerabilities, prioritize fixes, resolve issues, and monitor for new threats. As cloud adoption accelerates and digital ecosystems expand, a consistent and mature vulnerability management lifecycle becomes essential for maintaining visibility, prioritizing risk, and driving effective remediation. Vulnerability management lifecycle represents the systematic evolution from episodic security activities to continuous operational discipline.
Vulnerability Management Life Cycle As cloud adoption accelerates and digital ecosystems expand, a consistent and mature vulnerability management lifecycle becomes essential for maintaining visibility, prioritizing risk, and driving effective remediation. Vulnerability management lifecycle represents the systematic evolution from episodic security activities to continuous operational discipline.
Comments are closed.