The Ultimate Guide To Zero Trust Deception Tech
The Ultimate Guide To Zero Trust Deception Technology Countercraft Fortify your zero trust environments where other controls fail. download the ultimate guide to deception based active defense that detects zero trust compromises no one else can. Discover the benefits and best practices of zero trust with our comprehensive guide. learn from kuppingercole experts and enhance your security strategy today.
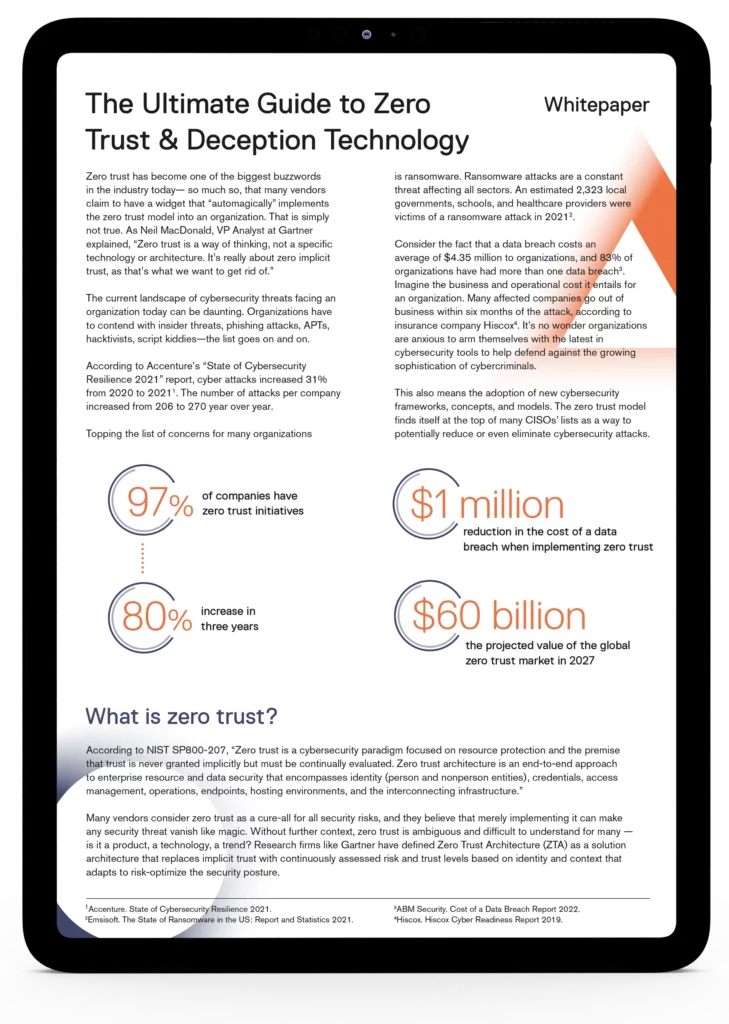
The Ultimate Guide To Zero Trust Deception Tech Learn how a zero trust strategy helps protect your organization’s identities, data, endpoints, apps, networks, and ai against sophisticated cyberthreats. In this sprawling digital kingdom, the old approach of “trust everything inside” is not just outdated — it’s dangerous. that’s where zero trust comes in. it tears down the old walls and replaces them with a new philosophy: never trust, always verify. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. Zero trust security: what is it? a contemporary cybersecurity strategy known as “zero trust security” does away with the idea of a trusted network perimeter. until confirmed, it considers all users, devices, and connections—whether internal or external to the company—to be potentially untrusted.
The Ultimate Guide To Zero Trust Deception Tech This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. Zero trust security: what is it? a contemporary cybersecurity strategy known as “zero trust security” does away with the idea of a trusted network perimeter. until confirmed, it considers all users, devices, and connections—whether internal or external to the company—to be potentially untrusted. To help shift from strategy to practice, we’ll clarify key zero trust concepts, explain the most influential models, explore top benefits, and share best practices in this complete guide to zero trust. 🛡️ {get it now} our new ultimate guide to zero trust and deception technology is full of information, explanations, and tips about how to combine the powerful duo of zero trust. Zero trust replaces “castle and moat” with “trust but verify.” a zero trust philosophy outlines a more dynamic, adaptive and realistic posture that assumes breaches have or will occur and seeks to reduce exposure by eliminating unnecessary access and maintaining dynamic control over privileges. This article offers an in depth review of zero trust security, including its benefits, best practices, and common barriers to implementation. you’ll gain a deeper understanding of zero trust models like ztaa and ztna and learn the tools and techniques you need to apply frictionless zero trust access control to your infrastructure. let’s.

The Ultimate Guide To Zero Trust Deception Tech To help shift from strategy to practice, we’ll clarify key zero trust concepts, explain the most influential models, explore top benefits, and share best practices in this complete guide to zero trust. 🛡️ {get it now} our new ultimate guide to zero trust and deception technology is full of information, explanations, and tips about how to combine the powerful duo of zero trust. Zero trust replaces “castle and moat” with “trust but verify.” a zero trust philosophy outlines a more dynamic, adaptive and realistic posture that assumes breaches have or will occur and seeks to reduce exposure by eliminating unnecessary access and maintaining dynamic control over privileges. This article offers an in depth review of zero trust security, including its benefits, best practices, and common barriers to implementation. you’ll gain a deeper understanding of zero trust models like ztaa and ztna and learn the tools and techniques you need to apply frictionless zero trust access control to your infrastructure. let’s.
Comments are closed.