The Threath Intelligence Handbook Moving Toward A Security

Threat Intelligence Handbook Pdf Intelligence Analysis Computer 140 page ebook describing how enterprises can implement a best in class security intelligence program. To find out how security experts use threat intelligence to reduce reactivity in incident response, watch the joint recorded future and lifars webinar “fuel incident response with threat intelligence to lower breach impact.”.

The Threat Intelligence Handbook Pdf Introduction moving toward a security intelligence program today, cyber threats are coming from everywhere — the open web and dark web, but also part. We’ve given this edition a subtitle of “moving toward a security intelligence program,” and these new chapters address this shift that every organization is going to have to take: toward security intelligence, a new paradigm of security of which threat intelligence is only one part. 140 page ebook describing how enterprises can implement a best in class security intelligence program. The threat intelligence handbook: a practical guide for security teams to google books.

Intelligence Handbook Fourth Edition Reducido Pdf Security 140 page ebook describing how enterprises can implement a best in class security intelligence program. The threat intelligence handbook: a practical guide for security teams to google books. Read full download now the threat intelligence handbook 2nd edition christopher ahlberg. How can threat intelligence strengthen all the teams in a cybersecurity organization? this book answers this question. it reviews the kinds of threat intelligence that are useful to security teams and how each team can use that intelligence to solve problems and address challenges. No matter what security role you play, intelligence enables smarter, faster decisions. the new, fourth edition of our most popular book is your definitive guide for developing an intelligence led security program. This book describes how security intelligence may help teams in security operations, incident response, vulnerability management, risk analysis, threat analysis, fraud prevention, and security leadership make better, faster decisions and have a greater effect.
The Threath Intelligence Handbook Moving Toward A Security Read full download now the threat intelligence handbook 2nd edition christopher ahlberg. How can threat intelligence strengthen all the teams in a cybersecurity organization? this book answers this question. it reviews the kinds of threat intelligence that are useful to security teams and how each team can use that intelligence to solve problems and address challenges. No matter what security role you play, intelligence enables smarter, faster decisions. the new, fourth edition of our most popular book is your definitive guide for developing an intelligence led security program. This book describes how security intelligence may help teams in security operations, incident response, vulnerability management, risk analysis, threat analysis, fraud prevention, and security leadership make better, faster decisions and have a greater effect.
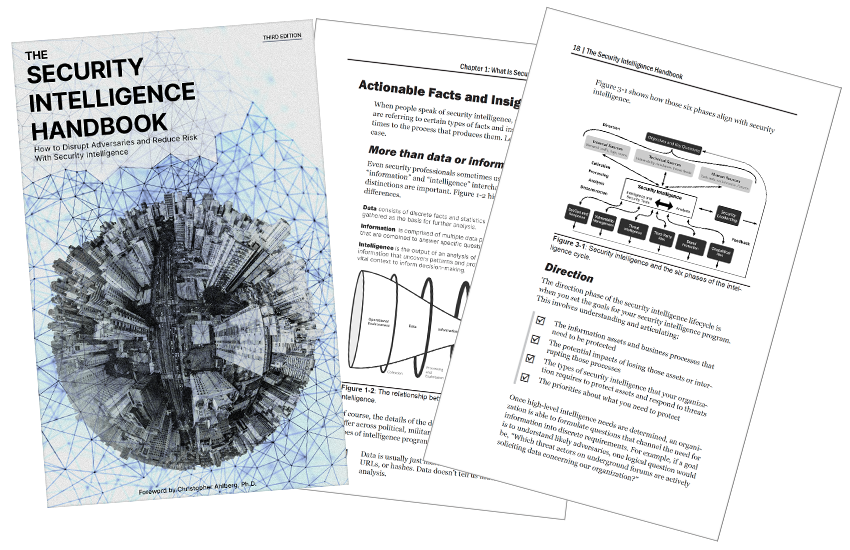
The Security Intelligence Handbook Third Edition Cyberedge Group No matter what security role you play, intelligence enables smarter, faster decisions. the new, fourth edition of our most popular book is your definitive guide for developing an intelligence led security program. This book describes how security intelligence may help teams in security operations, incident response, vulnerability management, risk analysis, threat analysis, fraud prevention, and security leadership make better, faster decisions and have a greater effect.
Comments are closed.