The Role Of Jwt Tokens In Ma Risks What You Need To Know Documentationmatters Apisecurity

Jwt Vs Opaque Tokens All You Need To Know By Udara Pathum Identity Major security incidents have demonstrated these risks. understanding how jwts work and where they fail helps security teams protect their apis effectively. what is jwt? json web token (jwt) is an open standard (rfc 7519) for securely transmitting information between parties as a json object. What is a jwt token? a json web token (jwt) is a compact, url safe means of representing claims to be transferred between two parties. the token consists of json objects and is.

A Study On A Jwt Based User Authentication And Api Pdf Computer Deep dive into common jwt security vulnerabilities and learn how to prevent replay attacks, key leaks, signature forgery and other security issues. provides practical security recommendations and best practices. But jwts come with risks. if a token gets stolen, an attacker can use it until it expires. unlike traditional sessions, there's no built in way to revoke a jwt once it's issued. plus, if the signing algorithm is weak or misconfigured, hackers can forge tokens and bypass security. In this comprehensive guide, you'll learn the inner workings of jwt tokens, their structure, security best practices, common vulnerabilities, debugging techniques, and implementation examples in 8 programming languages. If the key is weak, guessable, or hardcoded, an attacker can brute force it using a known jwt and use it to forge arbitrary tokens. this vulnerability can be common in poorly secured apis and test environments, and it often affects production systems due to careless key management.

Jwt Tokens And Their Security Risks In this comprehensive guide, you'll learn the inner workings of jwt tokens, their structure, security best practices, common vulnerabilities, debugging techniques, and implementation examples in 8 programming languages. If the key is weak, guessable, or hardcoded, an attacker can brute force it using a known jwt and use it to forge arbitrary tokens. this vulnerability can be common in poorly secured apis and test environments, and it often affects production systems due to careless key management. In this article, we take a detailed look at how json web tokens (jwts) work: their usefulness, structure, advantages and limitations. we have also identified the most common vulnerabilities, possible exploitation techniques and best practices for protecting against them. Json web tokens play a crucial role in authentication, particularly in web applications that use single sign on (sso). to reduce security risks associated with jwts, developers should adhere to best practices and rely on well established jwt libraries instead of creating custom implementations. Jwts are an excellent tool for stateless authentication, but they need to be handled carefully to avoid introducing security risks. by avoiding common pitfalls and following best coding practices, i have learnt to create secure authentication systems and faced all these problems as a beginner. There are several types of attacks that can target json web tokens (jwts), exploiting vulnerabilities in their implementation, transmission, or validation. here are some common types of jwt attacks: jwt libraries typically provide one method for verifying tokens and another that just decodes them.

Jwt Security Flaws Decoded Exploits Risks And How To Secure Your In this article, we take a detailed look at how json web tokens (jwts) work: their usefulness, structure, advantages and limitations. we have also identified the most common vulnerabilities, possible exploitation techniques and best practices for protecting against them. Json web tokens play a crucial role in authentication, particularly in web applications that use single sign on (sso). to reduce security risks associated with jwts, developers should adhere to best practices and rely on well established jwt libraries instead of creating custom implementations. Jwts are an excellent tool for stateless authentication, but they need to be handled carefully to avoid introducing security risks. by avoiding common pitfalls and following best coding practices, i have learnt to create secure authentication systems and faced all these problems as a beginner. There are several types of attacks that can target json web tokens (jwts), exploiting vulnerabilities in their implementation, transmission, or validation. here are some common types of jwt attacks: jwt libraries typically provide one method for verifying tokens and another that just decodes them.
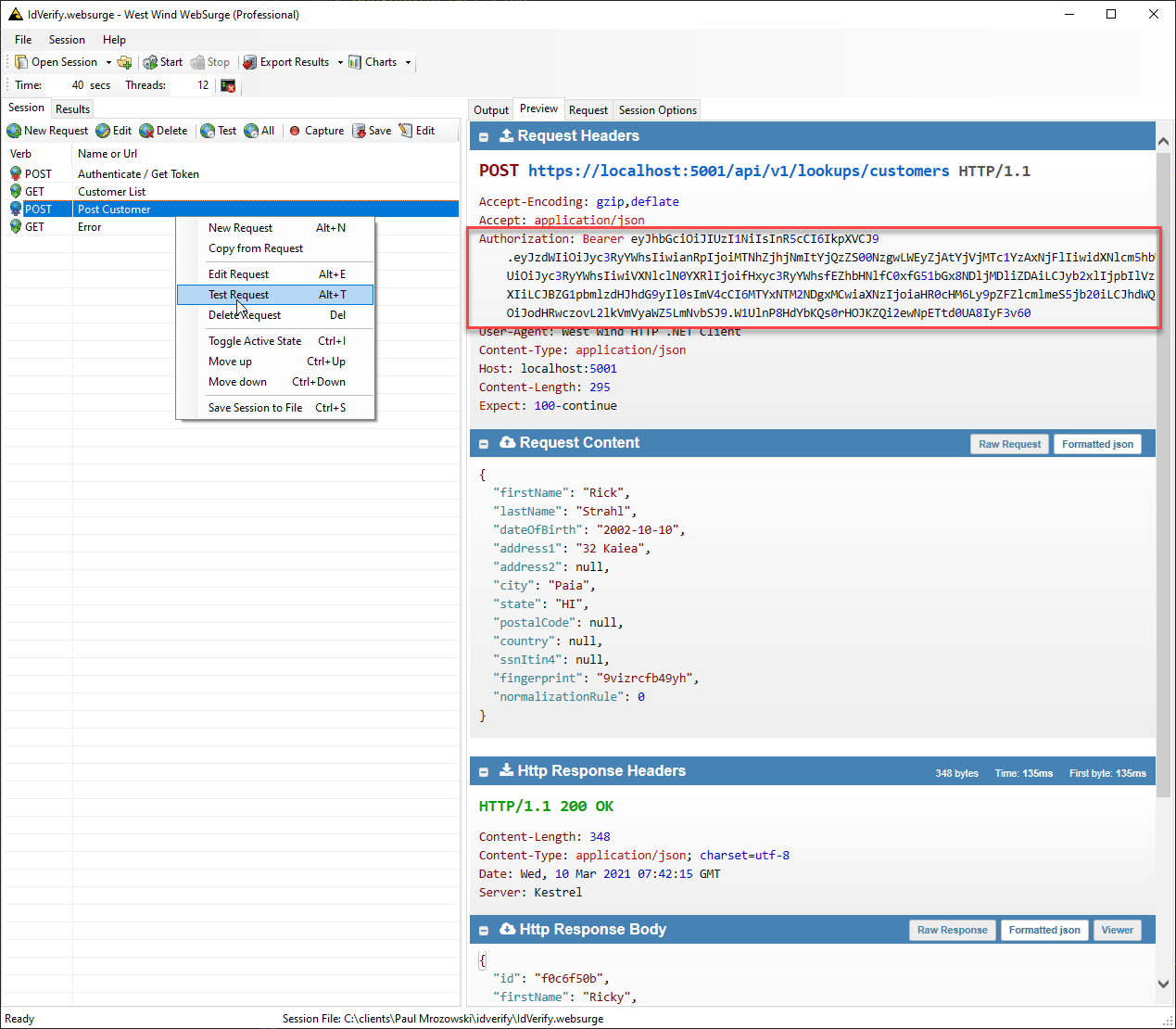
Role Based Jwt Tokens In Asp Net Core Apis Rick Strahl S Web Log Jwts are an excellent tool for stateless authentication, but they need to be handled carefully to avoid introducing security risks. by avoiding common pitfalls and following best coding practices, i have learnt to create secure authentication systems and faced all these problems as a beginner. There are several types of attacks that can target json web tokens (jwts), exploiting vulnerabilities in their implementation, transmission, or validation. here are some common types of jwt attacks: jwt libraries typically provide one method for verifying tokens and another that just decodes them.
Comments are closed.