The Result Executing Final Result Of Aes Exe Issue 1 Bea Jae

The Result Shown In Aes Exe Issue 1 Bea Jae Kyeong 128bit Aes This repository was archived by the owner on feb 18, 2021. it is now read only. sign up for free to join this conversation on github. already have an account? sign in to comment. #1 bea jae kyeong opened this issue feb 13, 2021 · 0 comments assignees copy link owner bea jae kyeong commented feb 13, 2021 •.
Jae Exe Jayden De Souza Github We have finally checked our complexity by metriculator to make our program work efficiently. we made a change to our code by removing hard coded part and finding a new solution. we can say that our final program’s software quality has improved to a better quality. {"payload":{"allshortcutsenabled":false,"filetree":{"":{"items":[{"name":"html","path":"html","contenttype":"directory"},{"name":".cproject","path":".cproject","contenttype":"file"},{"name":".project","path":".project","contenttype":"file"},{"name":"aes main.cpp","path":"aes main.cpp","contenttype":"file"},{"name":"doxyfile","path":"doxyfile. Final project of software quality in jaen university with one member software quality aes main.cpp at main · bea jae kyeong software quality. The plaintext before the removal of padding will result in random bytes and is then likely reported as bad padding. in this case a different iv is used for encryption and decryption.
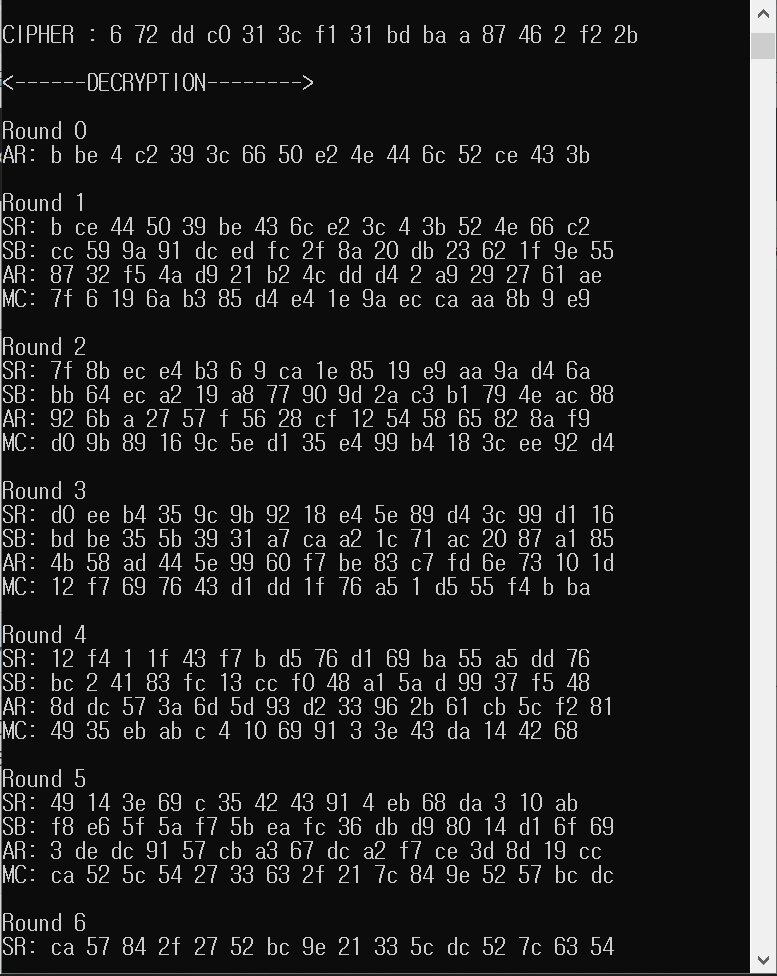
The Result Executing Final Result Of Aes Exe Issue 1 Bea Jae Final project of software quality in jaen university with one member software quality aes main.cpp at main · bea jae kyeong software quality. The plaintext before the removal of padding will result in random bytes and is then likely reported as bad padding. in this case a different iv is used for encryption and decryption. By addressing iv mismatches, padding schemes, key management, and encoding issues, you can resolve "incorrect initial bytes" errors and build robust aes cbc decryption workflows in java. This tutorial will show how two methods of implementing the aes algorithm work. it will also demonstrate how to identify these methods in assembly when reverse engineering an application. Learn how to tackle common exceptions in aes decryption in java with expert insights and code examples for smooth implementation. This blog post aims to provide a detailed overview of using aes encryption in java, including fundamental concepts, usage methods, common practices, and best practices.

The Result Of Executing Rsa Encryption Exe Issue 1 Bea Jae Kyeong By addressing iv mismatches, padding schemes, key management, and encoding issues, you can resolve "incorrect initial bytes" errors and build robust aes cbc decryption workflows in java. This tutorial will show how two methods of implementing the aes algorithm work. it will also demonstrate how to identify these methods in assembly when reverse engineering an application. Learn how to tackle common exceptions in aes decryption in java with expert insights and code examples for smooth implementation. This blog post aims to provide a detailed overview of using aes encryption in java, including fundamental concepts, usage methods, common practices, and best practices.

The Result Executing Final Result Of Aes Exe Issue 1 Bea Jae Learn how to tackle common exceptions in aes decryption in java with expert insights and code examples for smooth implementation. This blog post aims to provide a detailed overview of using aes encryption in java, including fundamental concepts, usage methods, common practices, and best practices.
Result Analysis Of Using Aes And Cp Abe Download Scientific Diagram
Comments are closed.