The Problem With Modern Kill Chains

Loss Chains And Kill Chains In this article, i critically examine the ‘cyber kill chain’, a methodological framework for thought and action that shapes both contemporary cybersecurity practice and the discursive. But in 2025, with ai driven attacks, ransomware as a service models, and cloud specific threats compressing or bypassing traditional stages, many cybersecurity professionals question whether the kill chain remains relevant in an evolving landscape. it’s time to re examine the kill chain.
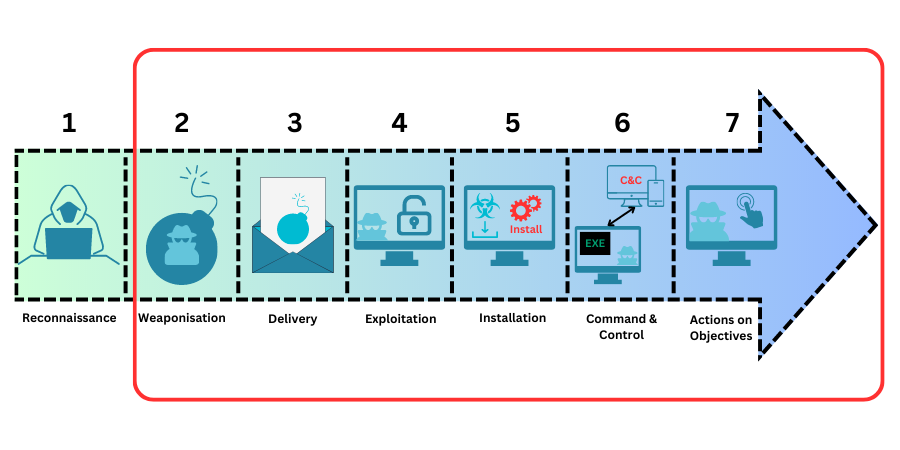
Kill Chains An Overview In this article, i critically examine the ‘cyber kill chain’, a methodological framework for thought and action that shapes both contemporary cybersecurity practice and the discursive construction of security threats. Insider threats, supply chain compromises, cloud native attacks… these don’t fit the old perimeter focused model. this is where the unified kill chain comes in. this guide will teach you what it is, why it was created, and how it addresses the critical gaps left by its predecessor. The research objective of this paper is to identify how each stage of the cyber kill chain is affected by advancements in ai, and what are some notable offensive examples and opportunities for cybersecurity experts. Created by lockheed martin, the kill chain outlined seven sequential steps attackers follow to execute a breach. but by 2025, attackers no longer follow linear paths, and defenders can no.
Kill Chains An Overview The research objective of this paper is to identify how each stage of the cyber kill chain is affected by advancements in ai, and what are some notable offensive examples and opportunities for cybersecurity experts. Created by lockheed martin, the kill chain outlined seven sequential steps attackers follow to execute a breach. but by 2025, attackers no longer follow linear paths, and defenders can no. The cyber kill chain provides not just a technical framework but a conceptual foundation—reminding defenders that security isn't about perfect protection but about understanding attack sequences and creating multiple opportunities for disruption. This article argues that the defining characteristic of modern warfare is not only the compression of kill chains – the sequence linking detection, decision, and destruction – but their diversification and resilience under continuous disruption. The department of defense should lead the next generation of kill chain dynamics in joint all domain operations by adopting object based storage solutions within its intelligence apparatuses to. While traditional security focuses on perimeter defense or isolated incidents, the kill chain provides context, showing how attackers advance and where defenses can most effectively intervene.
Kill Chains An Overview The cyber kill chain provides not just a technical framework but a conceptual foundation—reminding defenders that security isn't about perfect protection but about understanding attack sequences and creating multiple opportunities for disruption. This article argues that the defining characteristic of modern warfare is not only the compression of kill chains – the sequence linking detection, decision, and destruction – but their diversification and resilience under continuous disruption. The department of defense should lead the next generation of kill chain dynamics in joint all domain operations by adopting object based storage solutions within its intelligence apparatuses to. While traditional security focuses on perimeter defense or isolated incidents, the kill chain provides context, showing how attackers advance and where defenses can most effectively intervene.

Kill Chains An Overview The department of defense should lead the next generation of kill chain dynamics in joint all domain operations by adopting object based storage solutions within its intelligence apparatuses to. While traditional security focuses on perimeter defense or isolated incidents, the kill chain provides context, showing how attackers advance and where defenses can most effectively intervene.
Comments are closed.