The Ot Vulnerability Management Workflow

5 Surprising Findings From Ot Vulnerability Assessments Pdf With the help of an advanced ot cybersecurity platform, your organization can easily extend existing it vulnerability management workflows to your ot environment by integrating seamlessly with cmdb, orchestration, ticketing, siem, and related sources. The ot vulnerability management handbook from otbase outlines a performance based approach shaped by more than twenty years of experience in ot security consulting in everything from automotive factories to nuclear power plants.
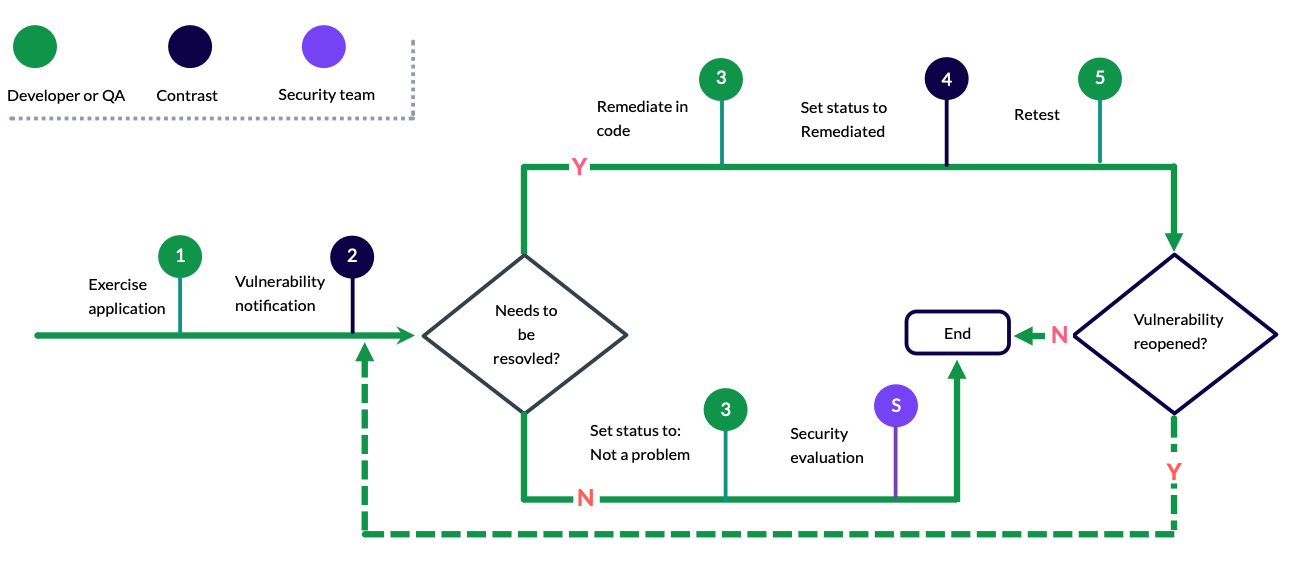
Vulnerability Management Workflow Webinar: securing your factory in the world of it ot convergence webinar: streamlining operational technology management and fortifying security in industrial environments. This guide walks through every phase of the ot vulnerability management lifecycle, addresses the challenges unique to industrial environments, and provides a framework for building a sustainable program. This vulnerability management workflow is recognized across the cybersecurity industry and is described in detail by the ot cyber security alliance. yet, ot vulnerability management is not a simple task. although the process can be stated succinctly, it is complicated in practice. Each action is implementable in a 0–90 day sprint, carries measurable outcomes, and prioritizes operational safety above all else. whether you are building a program from scratch or accelerating a stalled one, start here.

Vulnerability Management Workflow Seemplicity This vulnerability management workflow is recognized across the cybersecurity industry and is described in detail by the ot cyber security alliance. yet, ot vulnerability management is not a simple task. although the process can be stated succinctly, it is complicated in practice. Each action is implementable in a 0–90 day sprint, carries measurable outcomes, and prioritizes operational safety above all else. whether you are building a program from scratch or accelerating a stalled one, start here. Octoplant helps you stay ahead by making hidden risks visible and actionable. its vulnerability management solution continuously matches device and firmware data with public cve databases, identifying security gaps across your production environment without requiring active scans or manual audits. Our step by step playbook is specifically designed for ot environments, providing insights and tools to prioritize, track, and mitigate vulnerabilities effectively. Today’s post provides a comprehensive guide to ot vulnerability management, including the consequences of neglecting vm, practical steps for building a program, best practices, and recommendations from iec 62443, nerc cip, nis2, and nist csf. This handbook acts as a how to guide for the implementation of an effective ot vulnerability management process that is repeatable and delivers measurable and meaningful reductions of the attack surface.
Comments are closed.