The Ongoing Risks Of Hardcoded Jwt Keys Api Security
Implementing Jwt For Api Security Api7 Ai The core issue lies in a hardcoded jwt – a predictable, reusable authentication key embedded within the software. attackers could exploit this vulnerability by sending api requests using this hardcoded key to the ap image download interface. According to the wallarm threatstats report for q1 2025, hardcoded secrets – alongside misconfiguration and unauthenticated api access – contributed to an overwhelming majority of api security breaches in q1, particularly in ai and healthcare sectors.
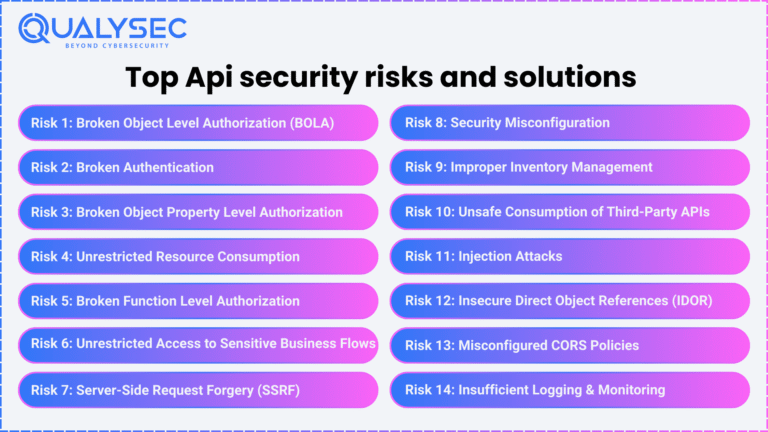
What Are Api Security Risks And How To Mitigate Them The core issue lies in a hardcoded jwt – a predictable, reusable authentication key – embedded within the software. attackers could exploit this vulnerability by sending api requests using this hardcoded key to the ap image download interface. According to the wallarm threatstats report for q1 2025, hardcoded secrets – alongside misconfiguration and unauthenticated api access – contributed to an overwhelming majority of api security breaches in q1, particularly in ai and healthcare sectors. In early may 2025, cisco released software fixes to address a flaw in its ios xe software for wireless lan controllers (wlcs). the vulnerability, tracked as cve 2025 20188, has a cvss score of 10.0 and could enable an unauthenticated, remote attacker to upload arbitrary files to a susceptible system – but the real story is that [ ]. Identify and fix jwt vulnerabilities: algorithm confusion, weak secrets, and missing validation, practical hardening techniques with examples.

Using Jwt As Api Keys Security Best Practices Implementation Guide In early may 2025, cisco released software fixes to address a flaw in its ios xe software for wireless lan controllers (wlcs). the vulnerability, tracked as cve 2025 20188, has a cvss score of 10.0 and could enable an unauthenticated, remote attacker to upload arbitrary files to a susceptible system – but the real story is that [ ]. Identify and fix jwt vulnerabilities: algorithm confusion, weak secrets, and missing validation, practical hardening techniques with examples. The vulnerability, tracked as cve 2025 20188, has a cvss score of 10.0 and could enable an unauthenticated, remote attacker to upload arbitrary files to a susceptible system – but the real story is that this vulnerability drives home the persistent risks associated with hardcoded credentials, particularly json web tokens (jwts), in network. Let's break down how hardcoded secrets become a risk, how they are exploited and most importantly, how to prevent them. what are hardcoded secrets, and why are they a problem?. This guide analyzes the essential jwt vulnerabilities list, drawing from authoritative sources to equip security teams with actionable insights for 2026. jwts power authentication in modern apis, but their compact structure invites abuse if not implemented rigorously. Critical vulnerability cve 2025 20188 in cisco software exposes hardcoded jwt key risks to systems. we provide the essential building blocks for cybersecurity solutions with comprehensive, structured, and constantly updated vulnerability and exploits data.

Understanding Jwt Basics And Security Risks Laburity The vulnerability, tracked as cve 2025 20188, has a cvss score of 10.0 and could enable an unauthenticated, remote attacker to upload arbitrary files to a susceptible system – but the real story is that this vulnerability drives home the persistent risks associated with hardcoded credentials, particularly json web tokens (jwts), in network. Let's break down how hardcoded secrets become a risk, how they are exploited and most importantly, how to prevent them. what are hardcoded secrets, and why are they a problem?. This guide analyzes the essential jwt vulnerabilities list, drawing from authoritative sources to equip security teams with actionable insights for 2026. jwts power authentication in modern apis, but their compact structure invites abuse if not implemented rigorously. Critical vulnerability cve 2025 20188 in cisco software exposes hardcoded jwt key risks to systems. we provide the essential building blocks for cybersecurity solutions with comprehensive, structured, and constantly updated vulnerability and exploits data.
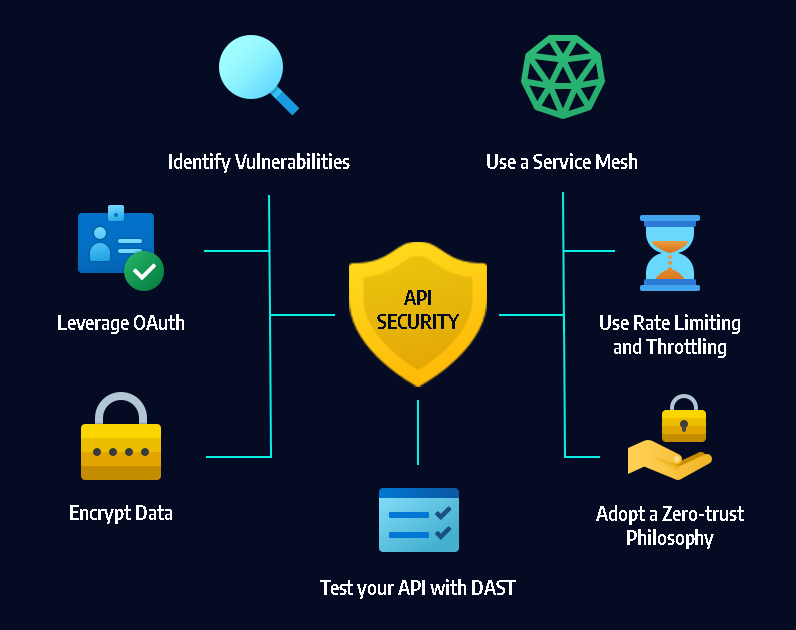
Web Penetration Testing Api Token Security Risks And Recommendations This guide analyzes the essential jwt vulnerabilities list, drawing from authoritative sources to equip security teams with actionable insights for 2026. jwts power authentication in modern apis, but their compact structure invites abuse if not implemented rigorously. Critical vulnerability cve 2025 20188 in cisco software exposes hardcoded jwt key risks to systems. we provide the essential building blocks for cybersecurity solutions with comprehensive, structured, and constantly updated vulnerability and exploits data.
Comments are closed.