The Layer 8 Difference Layer 8 Security
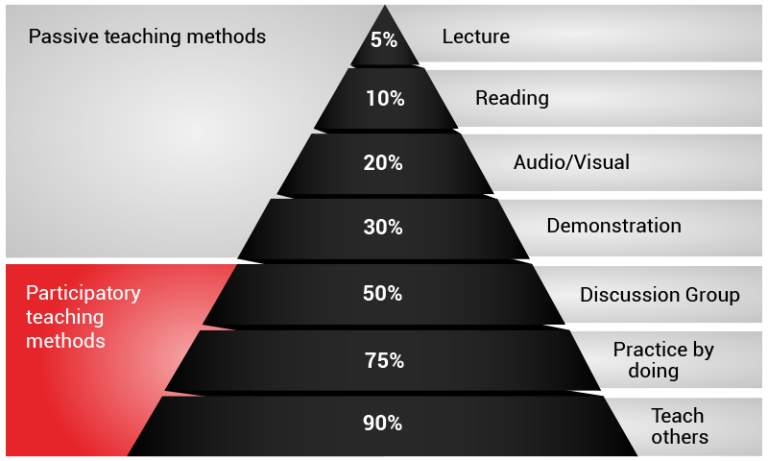
The Layer 8 Difference Layer 8 Security This is where layer 8 steps in. instead of providing formal training that ticks boxes, we have a customised learning approach for each individual within the organisation based on their security profile, encompassing their behaviour, attitude, and knowledge towards security. Security teams often focus on "layer 3" or "layer 4" data when trying to detect security issues or mitigate attacks. many are now moving up the stack to consider "layer 7.".

The Layer 8 Difference Layer 8 Security Everything you need to learn about the seven layers of cybersecurity, from human training and network protection to securing mission critical assets. While these measures are undeniably important, they address only one layer of the problem. with studies suggesting that up to 95% of security incidents trace back to human error, the most critical weakness isn’t technological at all; it’s human, often referred to by it teams as “layer 8.”. In today’s interconnected digital landscape, the human element—layer 8—is both the driving force and a potential vulnerability in cybersecurity. while technological defenses are essential, they are incomplete without considering the users who interact with these systems. Layer 8 champions® covers a vast spectrum of activity to enable your people to maintain and enhance your cyber resilience. talk to us about strategy, recruitment, our capability framework, measurement, and learning pathways for security champions.

The Layer 8 Difference Layer 8 Security In today’s interconnected digital landscape, the human element—layer 8—is both the driving force and a potential vulnerability in cybersecurity. while technological defenses are essential, they are incomplete without considering the users who interact with these systems. Layer 8 champions® covers a vast spectrum of activity to enable your people to maintain and enhance your cyber resilience. talk to us about strategy, recruitment, our capability framework, measurement, and learning pathways for security champions. Here, we must first define our perimeter before determining the sort of data being transmitted across this layer, and then we must secure both the data and the device. Layer 8 represents the human element in cybersecurity. it encompasses the individuals, their behavior, and the decisions they make. this layer recognizes that humans are both the weakest link and the strongest defense against cyber threats. If we don’t recognize the human as the fictitious eighth layer, we must at least acknowledge the risks it presents and enforce security controls for risk management and governance. Understanding and differentiating between layer 8 issues and technical failures is crucial for any it department aiming to bolster its system's reliability and security.

The Layer 8 Difference Layer 8 Security Here, we must first define our perimeter before determining the sort of data being transmitted across this layer, and then we must secure both the data and the device. Layer 8 represents the human element in cybersecurity. it encompasses the individuals, their behavior, and the decisions they make. this layer recognizes that humans are both the weakest link and the strongest defense against cyber threats. If we don’t recognize the human as the fictitious eighth layer, we must at least acknowledge the risks it presents and enforce security controls for risk management and governance. Understanding and differentiating between layer 8 issues and technical failures is crucial for any it department aiming to bolster its system's reliability and security.

The Layer 8 Difference Layer 8 Security If we don’t recognize the human as the fictitious eighth layer, we must at least acknowledge the risks it presents and enforce security controls for risk management and governance. Understanding and differentiating between layer 8 issues and technical failures is crucial for any it department aiming to bolster its system's reliability and security.
Comments are closed.