The Iot Security Challenge Protecting Connected Devices From Emerging

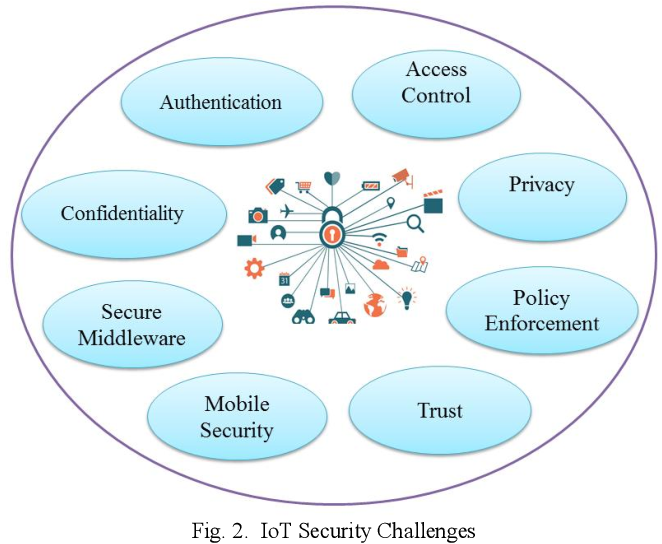
Emerging Cybersecurity Threats From Iot Devices In A Connected World The rapid expansion of iot technology presents significant security challenges that must be carefully addressed to establish a secure iot ecosystem. this article comprehensively examines security issues across different layers of iot and proposes corresponding countermeasures. Explore the complexities of iot security challenges and safeguard your connected devices against the latest cyber threats.

Iot Security Protecting Connected Devices The paper discusses common security threats, attacks, and vulnerabilities associated with iot devices and highlights the challenges associated with securing them against emerging security threats and cyberattacks. Iot protection risks relating to emerging or essential threats are identified, as well as future iot device attacks and possible threats associated with each surface. This survey investigates threats and countermeasures associated with iot ecosystems, categorizes threats targeting network infrastructure, devices, and data security, and provides a taxonomy to understand vulnerabilities. Comprehensive iot security guide for ctos and tech leaders. learn zero trust architecture, regulatory compliance, implementation strategies, and roi frameworks to protect connected infrastructure in 2025.

The Iot Security Challenge Protecting Connected Devices From Emerging This survey investigates threats and countermeasures associated with iot ecosystems, categorizes threats targeting network infrastructure, devices, and data security, and provides a taxonomy to understand vulnerabilities. Comprehensive iot security guide for ctos and tech leaders. learn zero trust architecture, regulatory compliance, implementation strategies, and roi frameworks to protect connected infrastructure in 2025. Explore emerging trends, challenges, and solutions in iot cybersecurity in our article. stay informed about the evolving landscape of securing internet of things devices and data. This paper has traversed the diverse terrain of iot security, exploring the threats that lurk within the interconnected web of devices, the protective measures designed to fortify this digital ecosystem, and the persisting challenges that cast a shadow on its secure evolution. Specifically, we highlight the latest improvements and challenges associated with iot security. finally, we discuss the state of the art research and its conclusions, as well as the outstanding problems for future iot security research. This article explores the risks associated with iot devices, the common vulnerabilities they face, and actionable strategies to safeguard these connected systems in an increasingly digital world.

Iot And Cybersecurity Protecting The Connected World From Emerging Threats Explore emerging trends, challenges, and solutions in iot cybersecurity in our article. stay informed about the evolving landscape of securing internet of things devices and data. This paper has traversed the diverse terrain of iot security, exploring the threats that lurk within the interconnected web of devices, the protective measures designed to fortify this digital ecosystem, and the persisting challenges that cast a shadow on its secure evolution. Specifically, we highlight the latest improvements and challenges associated with iot security. finally, we discuss the state of the art research and its conclusions, as well as the outstanding problems for future iot security research. This article explores the risks associated with iot devices, the common vulnerabilities they face, and actionable strategies to safeguard these connected systems in an increasingly digital world.

Security Challenges In Embedded Systems Protecting Iot Devices Specifically, we highlight the latest improvements and challenges associated with iot security. finally, we discuss the state of the art research and its conclusions, as well as the outstanding problems for future iot security research. This article explores the risks associated with iot devices, the common vulnerabilities they face, and actionable strategies to safeguard these connected systems in an increasingly digital world.
The Security Challenges Of Iot Devices Olivier Art
Comments are closed.