The Hackers Guide To Jwt Security
The Hacker S Guide To Jwt Security Pdf This talk guides you through various security risks of jwt, including confidentiality problems, vulnerabilities in algorithms and libraries, token cracking, token sidejacking, and more. Master jwt security with this in depth guide to web hacking and appsec. learn how to exploit and defend against real world jwt vulnerabilities like algorithm confusion, weak secrets, and kid injection — with hands on labs from pentesterlab.
The Hacker S Guide To Jwt Security Pdf The hacker’s guide to jwt security patrycja wegrzynowicz yon labs #jwtsecurity #jfuture @yonlabs. Jwts are widely used for authentication and authorization, but when misconfigured, they can open doors to serious vulnerabilities. here i am trying to sove the jwt security lab from. It emphasizes the need to require specific secure algorithms, long keys, https, and other best practices like token timeouts and blacklisting to prevent misuse of stolen tokens. overall it aims to educate developers on properly securing jwt usage. download as a pdf, pptx or view online for free. Introduction: json web tokens (jwt) have become the bedrock of authentication in modern, stateless web applications. however, misconfigurations and implementation flaws can transform this secure token standard into a gateway for severe security breaches.
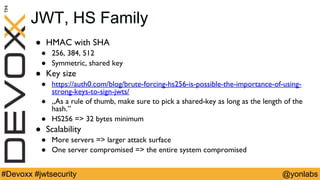
The Hacker S Guide To Jwt Security Pdf It emphasizes the need to require specific secure algorithms, long keys, https, and other best practices like token timeouts and blacklisting to prevent misuse of stolen tokens. overall it aims to educate developers on properly securing jwt usage. download as a pdf, pptx or view online for free. Introduction: json web tokens (jwt) have become the bedrock of authentication in modern, stateless web applications. however, misconfigurations and implementation flaws can transform this secure token standard into a gateway for severe security breaches. Learn the essential security measures to protect your json web tokens (jwts) from vulnerabilities and misuse, including key management, token verification, and anti xss practices to ensure secure stateless sessions and data exchange. This talk guides you through various security risks of jwt, including confidentiality problems, vulnerabilities in algorithms and libraries, token cracking, token sidejacking, and more. Discover how json web tokens (jwt) revolutionize web authentication. this guide covers everything from basic concepts to advanced security measures, helping you implement secure, scalable authentication in modern applications. Learn how to identify and exploit json web token (jwt) vulnerabilities using several different testing methods. read the article now!.

The Hacker S Guide To Jwt Security Pdf Learn the essential security measures to protect your json web tokens (jwts) from vulnerabilities and misuse, including key management, token verification, and anti xss practices to ensure secure stateless sessions and data exchange. This talk guides you through various security risks of jwt, including confidentiality problems, vulnerabilities in algorithms and libraries, token cracking, token sidejacking, and more. Discover how json web tokens (jwt) revolutionize web authentication. this guide covers everything from basic concepts to advanced security measures, helping you implement secure, scalable authentication in modern applications. Learn how to identify and exploit json web token (jwt) vulnerabilities using several different testing methods. read the article now!.
The Hacker S Guide To Jwt Security Pdf Discover how json web tokens (jwt) revolutionize web authentication. this guide covers everything from basic concepts to advanced security measures, helping you implement secure, scalable authentication in modern applications. Learn how to identify and exploit json web token (jwt) vulnerabilities using several different testing methods. read the article now!.
Github Redbalancer Jwt Security Example
Comments are closed.